
A 3AM ransomware is carrying out highly targeted attacks using affiliated email bombing and spoiling IT support calls to give credentials for remote access to socially engineer employees for corporate systems.
This strategy was previously associated with the Black Basta Rainmware Gang and was later seen in the Fin7 attacks, but its effectiveness has adopted widely.
Sophos, taking advantage of this technology between November 2024 and January 2025, are connected to two different threats in view of at least 55 attacks.
Those attacks followed the Blackbasta Playbook, including email bombing, visioning through Microsoft teams, and quick assistance misuse. The leakage of the internal interaction of the black bag helped to speed up other danger actors, as it included a template to use during Microsoft teams, which included the fishing attacks affecting the dish that aids it.
3AM ransomware attack, Target a sophos clientThe first quarter of 2025 occurred and used a similar approach, but with a twist of real phone fishing instead of Microsoft teams.
The danger actors spoiled the phone number of the Real IT department of the target to legalize the call. The call occurred during an email bombing wave of 24 unwanted emails received in three minutes.
The attacker forbidden the employee to open the Microsoft Quick Assist and give remote access, believed to be a reaction to malicious activity.
Subsequently, the attacker downloaded and extracted a malicious collection from a spufted domain, with a VBS script, a cumu emulator, and a Windows 7 image is pre-loaded with a pre-load with the cudendor backdoor.
Qemu was used to find out by rooting the network traffic through the virtual machines made on the platform, which allows the access to the network to continuously, yet unlike, yet united.
Through this, the attackers demonstrated the reconnaissance using WMIC and POWERSHELL, created a local administrator account to connect via RDP, established commercial RMM tool XEoxremote, and compromised on a domain administrator administrator account.
Although Sophos says its products have blocked the lateral movement and efforts for defense inaction, the attacker has still abolished 868 GB of data for cloud storage to cloud storage using the GoodsyNC tool.
Sophos’s tool also blocked the efforts after running the 3AM ransomware encrypter, so the damage was contained to the encryption of data theft and compromised hosts.
Source: Sophos
The attack lasted for 9 days, in which data stolen was done by three days, in which the danger actors were later blocked by spreading further.
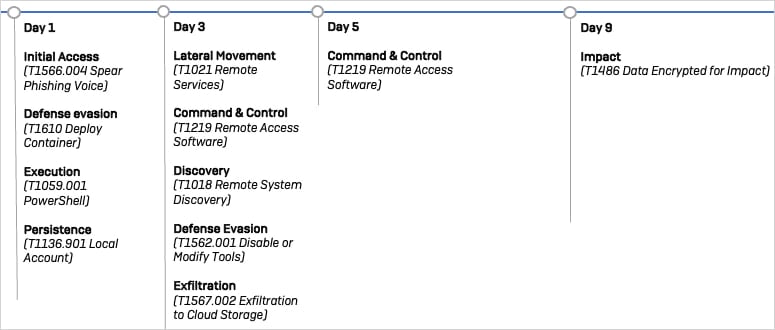
Source: Sophos
Sophos suggested several major defense steps, which can be taken to block these attacks, including auditing administrative accounts for poor security, using XDR tools using XDR tools to block the unique legitimate equipment like QEMU and Goodsync, and only apply the signed scrippt signed through the Powershell Prevision Policy.
It is also recommended Available indicators of agreement Used to install blacklists preventing infiltration from known malicious sources.
Ultimately, email bombing and voice phishing can only be effectively blocked by increasing employee awareness.
The 3AM ranmware operation was launched at the end of 2023 and was later linked to the Cotty and Royal Rainmware Gangs.



