
Results from 4th of Pentera Pentesting ReportThe one who surveyed around 500 Siso globally shows that the exposure management practices are maturing, yet there are some intervals that have to address the market yet.
The surface of the modern attack is spacious, dynamic, distributed and dangerously opaque. Since the enterprises expand into cloud-country or hybrid architecture, deploy APIs by thousands, and integrates the IOT and OT devices in core operations, the surface area for cyber hazards increases both in size and complication. Today, the average enterprise manages 75 safety devices, and about half the CISOS report continued to increase its safety stack year by year.
This complexity is not stopping the attackers. This enables them. The actor of danger works opportunisticly. No surface is safe because the attackers are motivated to exploit whatever is exposed; They are eventually motivated to target surfaces that are relatively weak compared to the next. For security leaders, this means that it is not a question of how to cover more land, but focus on maximum security – on the surface of the attack where the risk of risk is the highest?
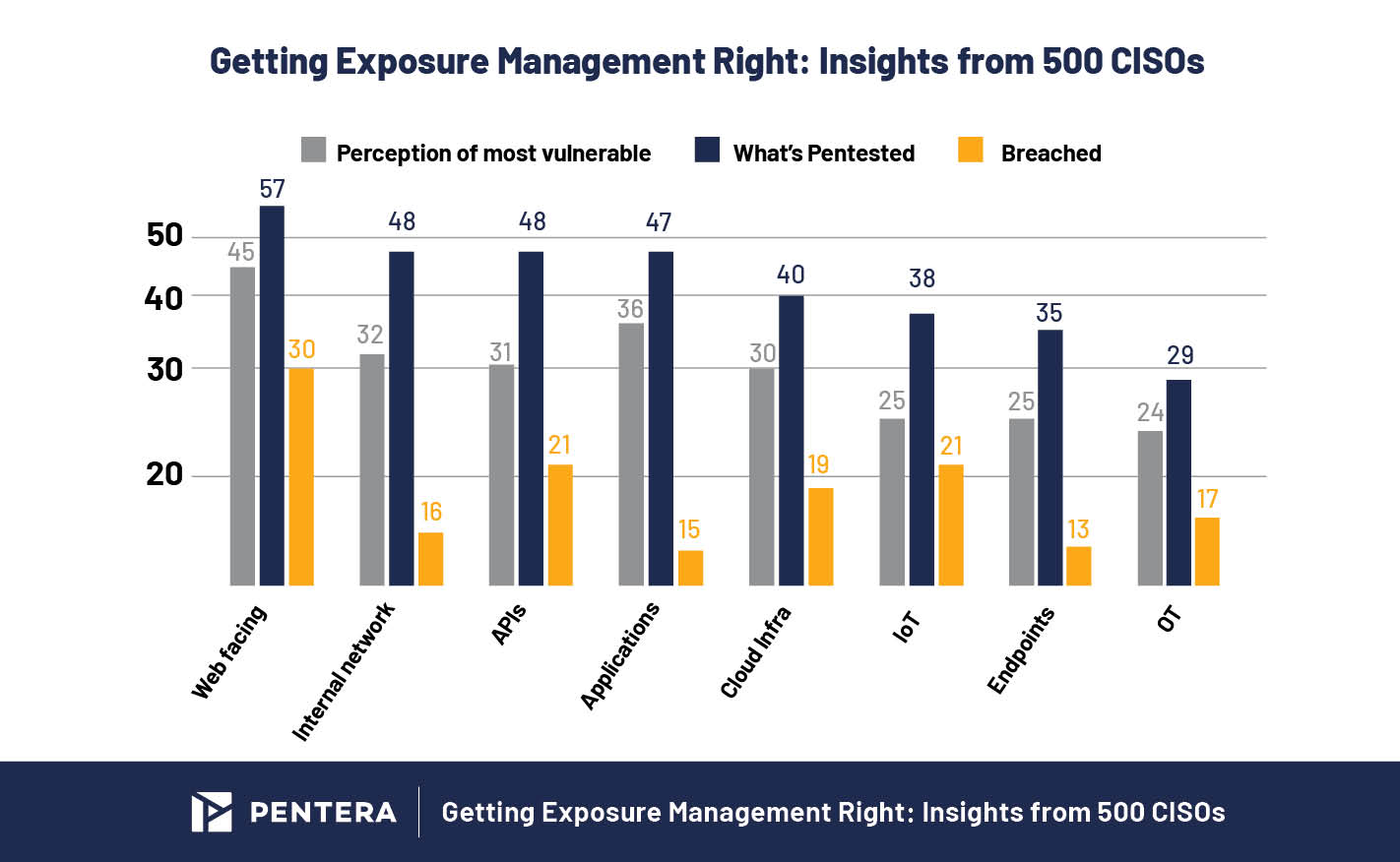
Recently released 2025 Pentating status report by Pentera Cloud manifests the vulnerability relative to various attack surfaces from infrastructure and web-festing assets to APIs, endpoints and even IOT systems. The CISOS of 500 enterprises was asked where they experience risk in their network, where the painting efforts are directed, and which areas were eventually dissolved.
Results provide insight to security teams to intensify their attention, direct their test strategies and close rapidly risky exposure.
Adopt an active approach to manage and reduce cyber risk, get expert insights from cyber security leaders on securing enterprise-wide networks, and listen to how top industry players are continuously threats to the stages of exposure management (CTEM).
Xposure provides an forward thinking approach to cyber flexibility.
A little felt about exposure management
Even with the best run exposure management programs, violations still occur. But working within more mature safety programs, you realize A violation does not always mean compromise,
Take the example of an exposed property. It can be dissolved in technical sense-maybe even with a danger actor, it is setting a leg on it .. But if this property is not bound by sensitive data, production systems, or important services, the real world influence is negligible.
Not all violations are equalThis basic mindset brings shift exposure management.
Unlike traditional vulnerability management, where teams are pursuing cves based on seriousness score or ticket age, the exposure management is strategic. It considers both Exploitation And Effect To determine what the weaknesses really matters. This allows dual lens teams to bypass noise and zero-in that can make disastrous agreement.
The status of the painting report confirms this truth. Despite reporting a violation of about 67% of enterprises in the last two years, only 36% faced downtime, 30% faced data exposure, and 28% financial loss. This means that a significant part of “violations” was very low or no operating result. The goal is not to eliminate every violation – but only those who will hurt you.
Web -Fesing Assets – still the weakest link
If the exposure management is about to align therapy with risk, the web-honor property is a prime example of a precautionary story.
According to the data, web-fasting assets top all three matrix: they are considered as the weakest (45%), the most (57%) tested (57%), and most often violated (30%).
In some ways it is encouraging. This indicates that security teams accurately prioritize external assets, identifying them as both accessible and attractive targets, and directing efforts accordingly.
But despite paying attention to all that, the attackers are still going inside.
Why? Because only on the basis of exposure, web-festing assets are risky. These systems – DNS, web portal and login pages are available. Their openness makes them “low-cut fruits”, especially when misunderstandings, exposed services, or open ports are left uncontrolled and without compensation for controls such as MFA.
Still it does not mean failure.
If the attackers violate a public -supporting property and reach a dead end – no access to sensitive systems, no valuable data, no lateral movement – so, then what? There was no effect of violation. In exposure management, it is not only about reducing brech rates – it is about reducing the effects of violations.
Internal Network, Establishment Points and Applications – A vested Front
When it comes to the closest system of Crown Jewels, the organizations are getting this correct. They are widely considered testing (48%) as weak (32%), and looking at low violation rates (16%).
Internal networks, endpoints, and applications show the top level for top level activity in each rank and comparatively low violation rates, 16% for interior networks, 13% for closing points and 15% for applications. All focused attempts are suggesting a payment.
These are systems that operate home sensitive data, power, and represent a clear path for lateral movement or privilege. Their alleged criticism earns them a large level of attention and attention, with layered safety control and tooling more mature. It also indicates something deep: exposure management maturity. Organizations are not scanning these systems only for weaknesses, they are painting them in context, giving priority on the basis of possible impact, and that is valid to confirm that rescue pressure is under pressure.
API Risk – Shows the difference between perception and reality
APIs sit at the crossroads of trade logic and backnd systems. They are essential, deeply integrated, and often ignored, showing the API with the data of the survey reports that the security teams may be more weak than the realization.
While the API is tested at the same rate of the internal network (48%), they show a high violation rate, 21%than 16%for the internal network. This difference suggests a disconnect: either the alleged risk of API is very low, or the current test approaches are not revealing the entire photo.
The challenge is complexity. APIs are dynamic, hard for inventory, and it is very difficult to test well. Their attack surface is not only about ports or closing points, this argument is about defects, broken certification and misunderstanding integration, all leading to the attacking paths that do not appear in a standard scan.
APIs often do bridge systems, whether among cloud services, third-party equipment, mobile app and internal database. This makes them a major goal for lateral movement or data exfoliation. And their visibility difference makes them particularly attractive to the attackers who understand how to walk under the radar.
Closing the difference means that in terms of frequency and depth, leveling the test. Continuous, adverse testing of API is necessary to highlight integration defects that traditional methods appear missing.
Exposure shows encouraging signs of management alignment
2025 State Status Penting Report confirms what we have known for years – close proximity to business risk drive.
Alignment between alleged risk, painting activity and violations is increasing. A strong signal that is maturing the exposure management practice, as teams are reducing the difference between eclipse and real risk.
The goal of exposure management is not to prevent every violation. This is to stop those people. By combining data-operated priority with continuous verification, the security team can focus on real exposure, not theoretical threats. To ensure that when the attacker knocks, nothing is valuable behind that door.
To learn more about how major enterprises are implementing their exposure management programs, participate XposureNational Exposure Management Vsummit.
Sponsored and written by Pentera,


