Still getting login code through text or authentic apps? You are not alone – and this is a big problem. Feeling like a smart security layer that is now one of the easiest ways for the attackers to get access to your accounts.
Earlier we were asked to use SMS for MFA. Then we were told: “Do not use SMS for MFA, instead use an authentic app.”
And while it may look like a step ahead, it is still fundamentally flawed. Authenticator apps reform the message blocking on SMS, but they easily become fish (now) fish and often rely on time-based codes, which are compromised on the device, or even intercepted.
The main issue remains: The system does not know whether it is being used on a valid site or an ideal fake. So when it is a separate system, it is not a safe – just a broken version of the same problem.
Want evidence? Recently, high-profile breech (AFLAC, Erie Insurance and Philadelphia Insurance Companies) showed how easy it is.
Some calls were called to help the desk to help or reset the MFA bypass or reset. But the favorite is quickly becoming a fishing/spuff trick.
A fishing email land. The user clicks. The Spufed website is Pixel Perfect. They enter their user name, password, and they confirm that it is on their authentic app. Done. The attacker is inside.
Because the authentic app does not verify who is asking or where the request comes from – you become an attack vector.
Download to find out how ransomware attacks are developing and inheritance MFA cannot be kept.
This guide reveals the influence of the real world of fishing-resistant MFA, how it prevents ransomware before it is damaged, and why CISOs are switching to the next generation certification.
This is what no one wants to say loudly: authentic apps and SMS codes can be fish in real time. They give users a false sense of security while not giving any real security against today’s most common threat – websites added with social engineering.
Even major platforms like Amazon and Google, according to recent investigation, use third-party SMS delivery firms-with some monitoring operations. These mediators have already been linked to security violations. Even the US Cyber Security and Infrastructure Security Agency (CISA) issued a blunt warning: “Do not use SMS as another factor.”
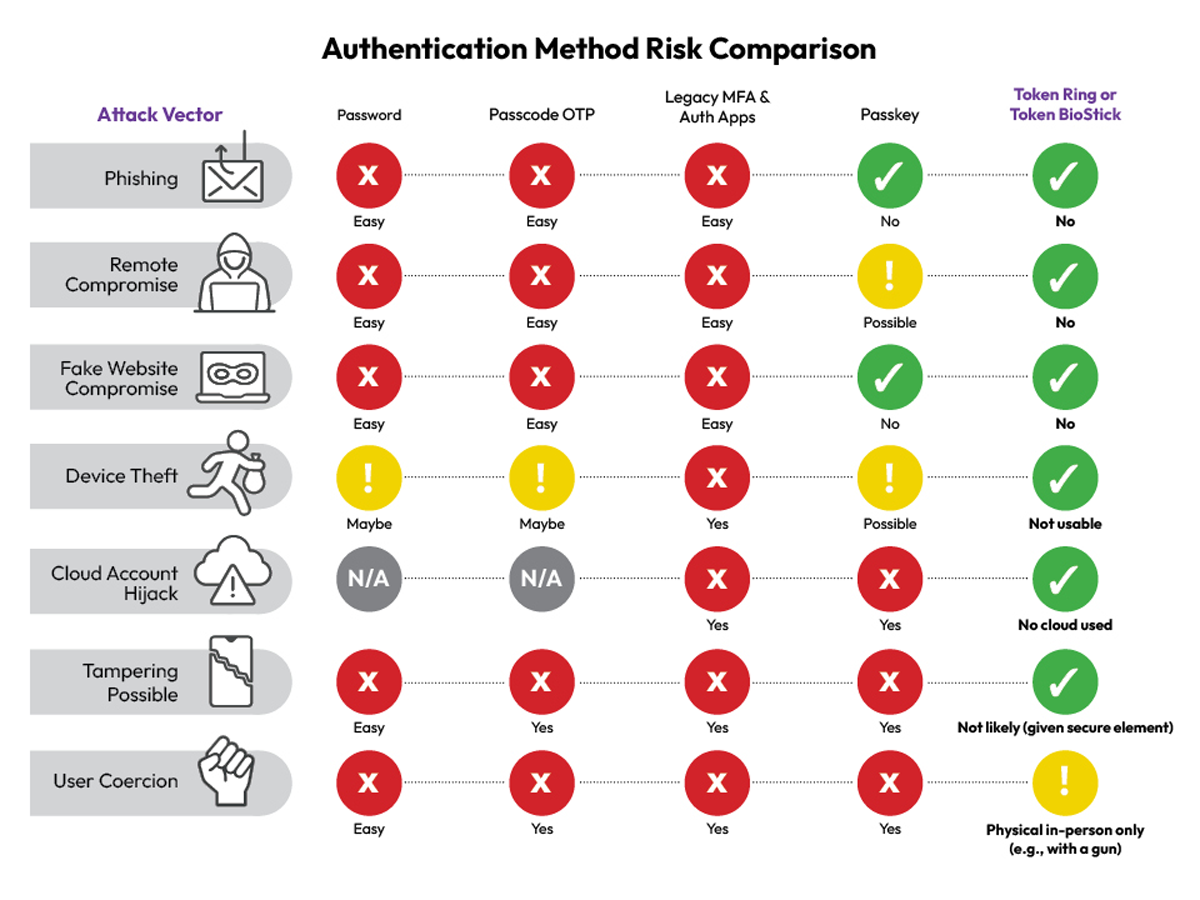
So you may imagine that Pacches are an answer – and they are a small step ahead, but now they are also easily compromised. They cry cryptographically to websites login credentials and reduce human error. But they are not fools. Passkeys are often stored and sync through cloud accounts.
If someone kidnaps your Apple or Google account, they can get access to every pass that you saved. A theft or compromise phone? The same risk. And malware or users can still forcibly result in approval that provide complete access to the attackers.
So what Is Solution? This is the time to carry forward the confusion of the code and the cloud-link. enter token Ring And Token biosti-Momi-made, biometric hardware authenticator that removes a completely weak link.
Why do they work here:
- no clouds.
- No shared mystery.
- No dependence on user decision.
- No code entry.
Token ring and token biostik stores their credentials inside safe elements tampering. They only certify when your fingerprint coincides, you are physically present, and the domain requesting access is cryptographically verified.
Even if an attacker steals the device, it is useless without your fingerprint. Even if you are tricked to go to a fake site, it will not be alive, certify alone – because the device should be in closeness to the device logging in, and even if one finds out that the cryptographic handshake fails automatically.
They cannot be fishing. They cannot be kidnapped from a distance. They eliminate confidence from the equation. It is the power of biometric fido2, which is correct in safe hardware, which has no shortcuts.
Low Line: If your MFA can be cheated by a fake website, it is already obsolete.
SMS is dead. Authentic apps are heritage. Passkeys are progressing – but flawed.
token Ring And Token biosti Gold standards are. Fishing-proof. Molestation-resistant. Biometric bound. Need proximity.
The attackers are coming for your MFA and Aath apps – that’s nothing IfBut When?And today every other method? They fail.
It is time to upgrade. Before you are the next headline.
Sponsored and written by Token,



