
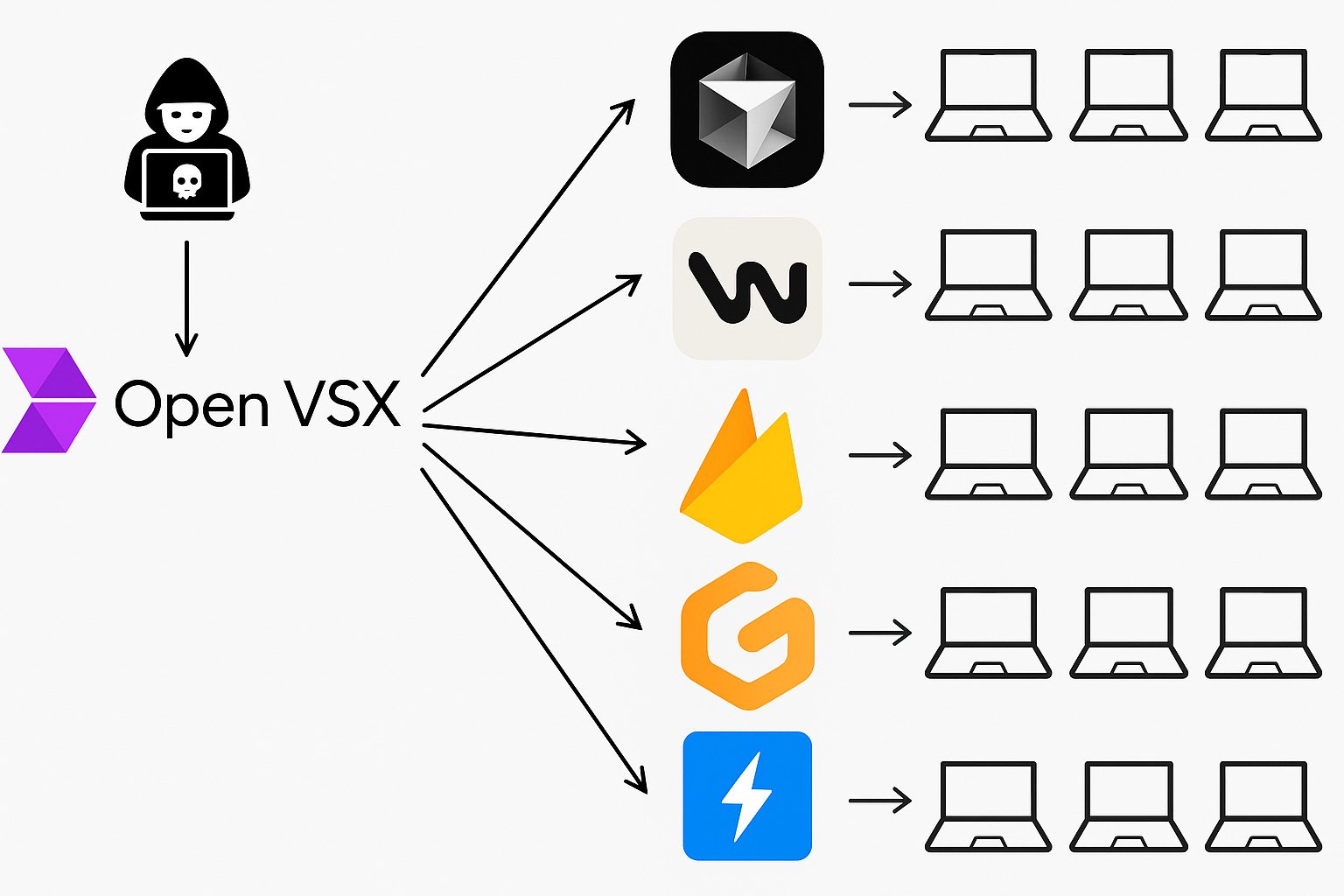
A security researcher from Any security Today’s AI stumbled an important zero-day in the infrastructure that power power tools. Had it been exploited, a non-convertible attacker could kidnap more than 10 million machines with a single stroke.
AI coding assistants such as Cursor and Windsurf have exploded popularity for developers around the world, promising supercharged productivity. There is a shared foundation behind their smooth interface: community-made vs. code forks and an open market of extensions that gives strength to magic. However, this new wave of developer tooling has a dangerous blind place.
Dubbed vsxplit: A single unseen defects in Openvsx – a significant component in the developer supply chain – allowed silence on any machine running a VS code fork, perfect -procedural agreement. A bug. Total control.
Let’s dive.
Today’s AI-managed editors rely very much on the extension to give their most basic functionality. Facilities such as syntax highlighting, linting and debugging are not hardcoded in the editor – they are provided by extensions.
Each of these extensions runs on the developer’s machine with complete privileges. In return, this means that a single agreement extension can acquire the entire machine of anyone who establishes anyone.
This is an accurate nightmare landscape from the security researcher Oren Yomtov Any securityThe company that provides a platform to achieve software provisioning and extension, stumbled.
Recently in a post Yomtov suggests that when examining the construction process behind Openvsx, open-source marketplace powering extensions for devices such as cursor, windsurf, vscodium and others discovered an important defect.
The vulnerability allowed any attacker to gain control not only on the same extension, but also gained complete control over a supply chain Armagadon, the entire market.
Given this defect, any attacker can carry forward malicious updates under reliable @Open-VSX account. First, Yomtov admitted that it was a mistake, this code was going on for years, which was used by millions of people. But when he rebuilt the attack in his laboratory, simulation worked innocent.
What seemed unimaginable was suddenly very real: a silent, full -scale security disaster was sitting in a plain vision.
Learn how Koi VSCODE, Openvsx, Chrome and other marketplace helps in discovery, assessment and governance of risky extensions.
Get complete visibility and protect your development supply chain.
Religion: A variation on classic “pwn request”
To understand how vulnerability worked, you first need to understand how extensions make your way in Openvsx in the first place.
If you want to publish an extension to open VSX, you have two options:
-
Upload it to open VSX yourself
-
For a bridge request to be auto-published, request an extension that adds extension to the list in the extension.
“Night construction is where the problem lies,” says Yomtov.
Every night, Openvsx runs an automated process that attains the latest versions of community-product extensions, creates them, and publishes them in the market. This is to make life easier for developers, but in this case, it offered an important defect.
To get an extension auto-published, all developers have to do it to add a simple bridge request to a public list. From there, Openvsx takes: it pulls the code, establishes dependence, creates extensions, and publishes it using a powerful secret token that belongs to the reliable @Open-VSX account.

This token was to stay hidden, only a reliable infrastructure. Unfortunately, how the build process runs an arbitrary code from public repository, any extension writer can craft a malicious update Catchs the token quietly,
Even more worrying is that they will not need to present a malicious extension directly. They could hide their code within a dependence, or even a dependency-e-dependence, and the system would have automatically executed during the night construction. From there, stealing tokens was trivial.
And with that token in hand, an attacker will not just control his own expansion. They could publish updates, overcrowd the existing people, and quietly hijack the entire market.
Effect: A supply-chain nightmare that exposes millions of developers
@Open-VSX with access to the token of the account, an attacker could create a world-wide supply chain nightmare. “That token is a super-admin credential,” says Yomtov. “It can publish new extensions, caning existing people, and replicate any publisher in the ecosystem.”
From that point, the damage becomes almost comfortable. Each time a developer installs an extension or their editor auto-updates in the background, which is frequent, the attacker’s payload will be quietly transported to their machine. No alert. No signal. No doubt. Complete acquisition.
And what can that payload do? “Enough,” says Yomtov. The VS code and its forks run as an extension node. JS processes, which means they can reach files, launch other programs, network requests and execute arbitrary codes.
A malicious update for a popular extension, says, pythan plugins, quietly a kelogger, stolen browser cookies, swipe source code, infectious build, or backdor can install complete growth pipelines.
There are separate cases of evil vs code extensions that steal SSH Keys or Crypto wallet. But it will not be a bad actor slipping through the crack. This will be a complete scale acquisition, supply-chain agreement on the scale of the ecosystem. Like solarwind, but for developer tools.
While the effects will be the most serious for desktop editors such as cursor, windsurf, and vscodium, even the browser-based environment such as gitpod or stackblitz may be affected, it depends on how deeply the compromised extensions are integrated.
So what can you do about it?
We asked Yomtov what users and organizations should go away from this phenomenon. Their answer was blunt: “Suppose every extension is incredible until it is proven otherwise.”
Extenses may feel like harmless ad-ons, but under hood, they are powerful software components, often written by individuals, running with full permissions, and are automatically updated without an oversight.
“It is no different from pulling a package from NPM or PPI, and usually worse is called” Yomtov “. “If you do not trust a github repo with root access for your machine, you should not rely on an extension.”
To protect themselves, Yomtov recommends organizations to treat extensions as part of their attack surface and apply the same discipline that they use for any other dependence. That means:
-
Maintain a real inventory What has been installed, in which machines, and by whom
-
Exposure It is based on who created the extension, how it is maintained, and what it really does
-
Implementation of clear policies What is allowed, and when something comes out of the limit, is taking action
-
Constant monitoringSince the extensions can update quietly and introduce new risks overnight
The KOI’s research team continues to find both both weak and active malicious extensions – not only in Openvsx, or in the marketplace of Microsoft, even in other extension marketplaces such as Chrome web stores.
“The ecosystem has increased rapidly than the railing,” says yomtov. “The safest perception is zero trust until he changes. Each extension is a possible back door until you have reviewed and watching it.”
Yomtov and in team Any security Responsibilities revealed vulnerability to the eclipse Foundation, which maintains the Openvsx project. In the next weeks, he worked with maintenance to validate the issue, designing a strong fix, and ensured that the patch was properly implemented and deployed.
Thanks to this cooperation, the vulnerability has stopped and the market is once again safe for millions of developers who rely on it.
But this phenomenon acts as a wake -up call – even reliable infrastructure requires continuous investigation, especially when it holds the key to the entire development ecosystem.
Learn how KOI helps organizations to discover, assess and operate risky extensions in VSCODE, Openvsx, Chrome and other marketplace
Chat with us.
Sponsored and written by Any security,


