
A poison phishing campaign Fido2 Security is by misusing the security of security to the security of the fake company portals by misusing the Cross-device sign-in facility to the security.
Poison danger actors are known to appoint large amounts of fishing attacks for financial fraud. In the past, distributing emails with crypto seed phrases is used to dry the cryptocurrency wallet.
In recent fishing attack ExpelledActor with poison-threatened actor does not take advantage of a defect in the protection of Fido2, but misuse a valid cross-device authentication facility.
Cross-device authentication is a webauthn feature that allows users to sign on a device using the safety key or authentication app on another device. Instead of the need for a physical connection, such as plugged into the safety key, the authentication request is transmitted between the equipment via Bluetooth or QR code scan.
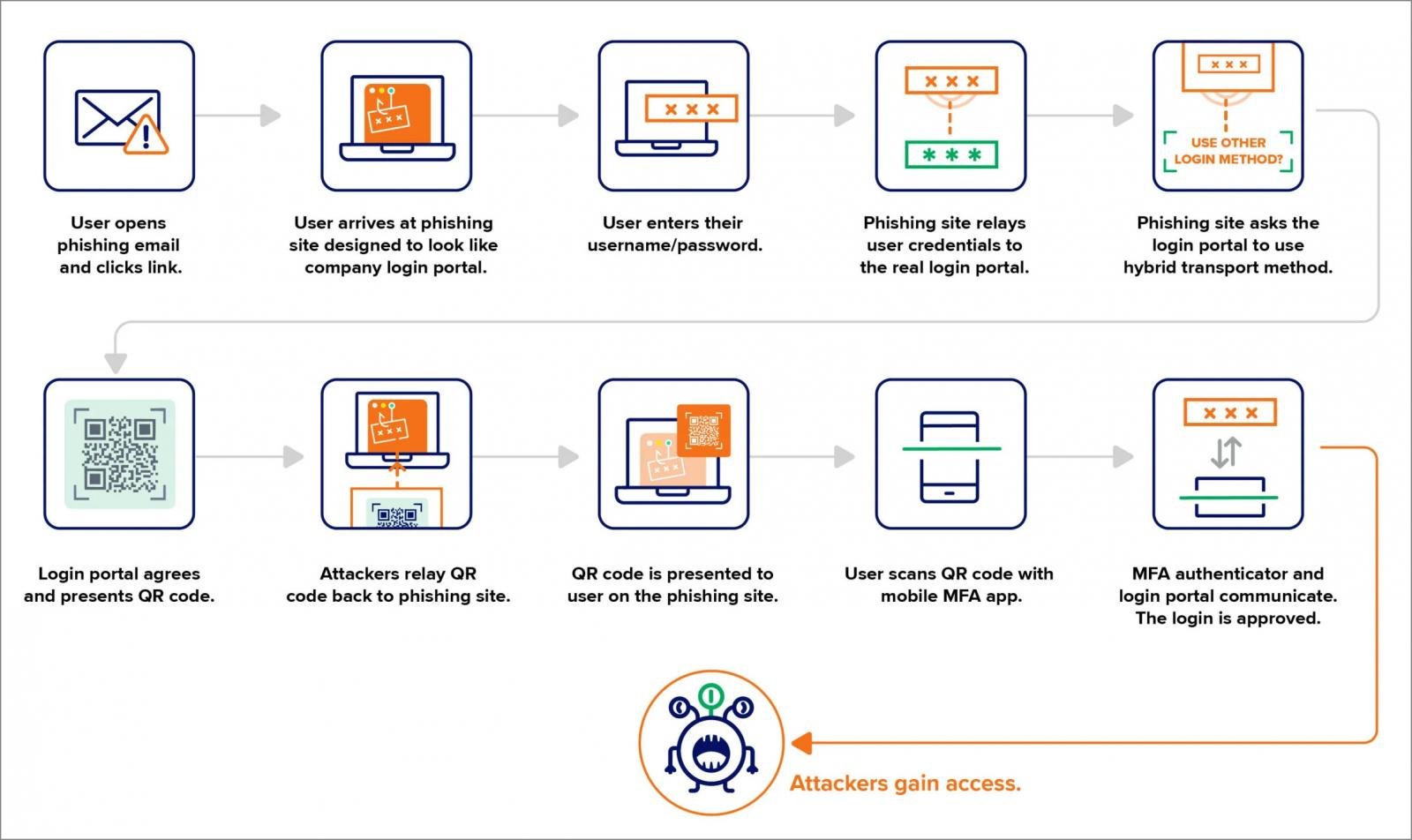
The attack begins by directing users on a fishing site that applies the corporate login portal, such as OCTA or Microsoft 365.
When the user enters its credentials in the portal, the campaign uses an adverse-in-media (AITM) backnd to quietly log in with credentials presented on a valid login portal in real time.
The targeted user in the attack will normally use its Fido2 security key to verify multi-factor authentication requests. However, Fishing Backand explains the valid login portal to certify using cross-device authentication instead.
It causes a valid portal to generate a QR code, which is sent back to the fishing page and displayed to the user.
When the user scans this QR code using its smartphone or certification app, it approves the login effort launched by the attacker.
Source: Expeling
This method effectively bypasses the fido2 security security by allowing attackers to initiate a login flow which depends on cross-device authentication rather than the user’s physical fido2 key.
The expulsion warns that the attack does not take advantage of a defect in the Fido2 implementation, but rather misuses a valid feat that downgrade the Fido major authentication process.
To reduce the risk, the expulsion recommends the following rescue:
- Limiting geographical locations, allowing users to log in and establish a registration process for traveling individuals.
- Regularly check for registration of unknown Fido key from unknown locations and unusual safety major brands.
- Organizations can consider applying Bluetooth-based certification as a requirement for cross-device authentication, which significantly reduces the effectiveness of distant fishing attacks.
The expulsion also saw a separate incident, where a danger actor recorded his Fido key after compromising an account through an account to reset fishing and password. However, this attack did not require any method to trick the user like the QR code.
This attack highlights how the danger actor users are looking for ways to bypass the phishing-resistant authentication in completing the login flow to bypass the need for physical interaction with the safety key.



