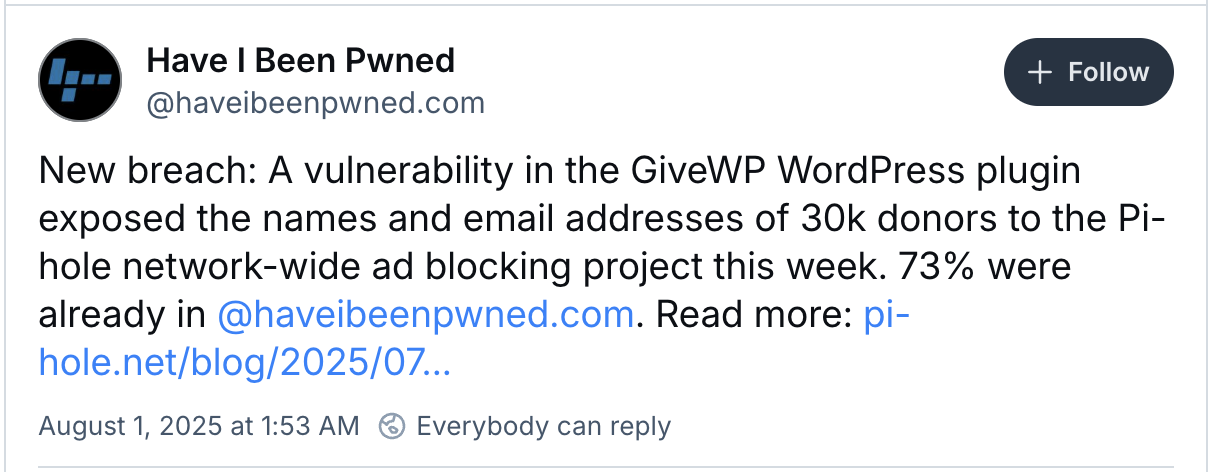
Pie-Hole, a popular network-level advertising-plank, has revealed that the donor name and email address were exposed through a safety vulnerability in the Givep WordPress Donation Plugin.
Pie-Hole acts as a DNS sinkhole, filtering unwanted materials before reaching users’ devices. While the Raspberry Pie was initially designed to run on single-board computers, it now supports various Linux systems on dedicated hardware or virtual machines.
The organization said that they first learned about the incident on Monday 28 July after donors. Started reporting That they were receiving suspicious emails Especially used for donations,
As explained in one Friday post mortemBreach impressed users who donated through the donation form of the P-Hol website to support the development, highlighting personal information that was visible to anyone, which was due to seeing the source code of the webpage for any person.
Vulnerability Stem from Givewp, a WordPress plugin is used to process the donation on a pie-hole website. Plugin inadvertently informed the publicly accessible donor without the need for certification or special access privileges.
While Pai-Hole did not disclose the number of affected customers, ‘Do I pwned’ data breech notification service added Pai-Hol Breech, saying that it affects about 30,000 donors, with already 73% exposed records in its database.
No financial information was revealed
Pai-Hole stated that no donor financial data was compromised, as credit card information and other payment details are directly handled by strip and PayPal. It also clarified that the PI-Hole Software Product itself was not affected by any way.
“We make it clear in donation form that we do not even need a legitimate name or email address, it is purely to see and manage their donations to users,” Pie-Hole said“It is also important to note that pie-hole product is not clearly a matter of this violation. No action is required from PI-Holl users installed on their network.”
Although Githwp released a patch within hours of the vulnerability being reported on Github, Pie-Hole criticized the plugin developer’s response, cited a delay of 17.5 hours before informing the users and described as an inadequate safety of the possible impact of security defects on donor names and email addresses.
Pai-Hole apologized to the affected donors and acknowledged the potential reputation damage arising out of this security incident, saying that while the vulnerability was unpredictable, they accept accountability for resulting data violations.
“The names and email addresses of any person who had ever donated through our donation page were to see the whole world (provided that they were sufficient to the right click-> Visual page source). Within a few hours of this report, he packed the bad code and released 4.6.1,” Pai-Hol added to a blog in a blog post.
“We take full responsibility for the software we deploy. We placed our belief in a widely used plugin, and this belief broke.”