Cybercriminals are abusing widespread lack of authentication in customer service platforms zendesk The targeted email inbox is flooded with dangerous messages that appear to come from hundreds of ZenDesk corporate customers at once.
Zendesk is an automated help desk service designed to make it easier for people to contact companies for customer support issues. Earlier this week, KrebsOnSecurity began receiving thousands of ticket creation notification messages in rapid succession through Zendesk, each containing the names of different Zendesk customers, such as capcom, CompTIA, discord, GMAC, nordvpn, Washington PostAnd tinder,
Abusive messages sent through Zendesk’s platform can include any subject line chosen by abusers. In my case, the messages variously warned about an alleged law enforcement investigation involving KrebsOnSecurity.com, or otherwise included personal insults.
Furthermore, the automated messages sent by this type of abuse come from customer domain names – not from Zendesk. In the example below, replying to any junk customer support response from The Washington Post’s Zendesk installation shows that the reply address is help@washpost.com.
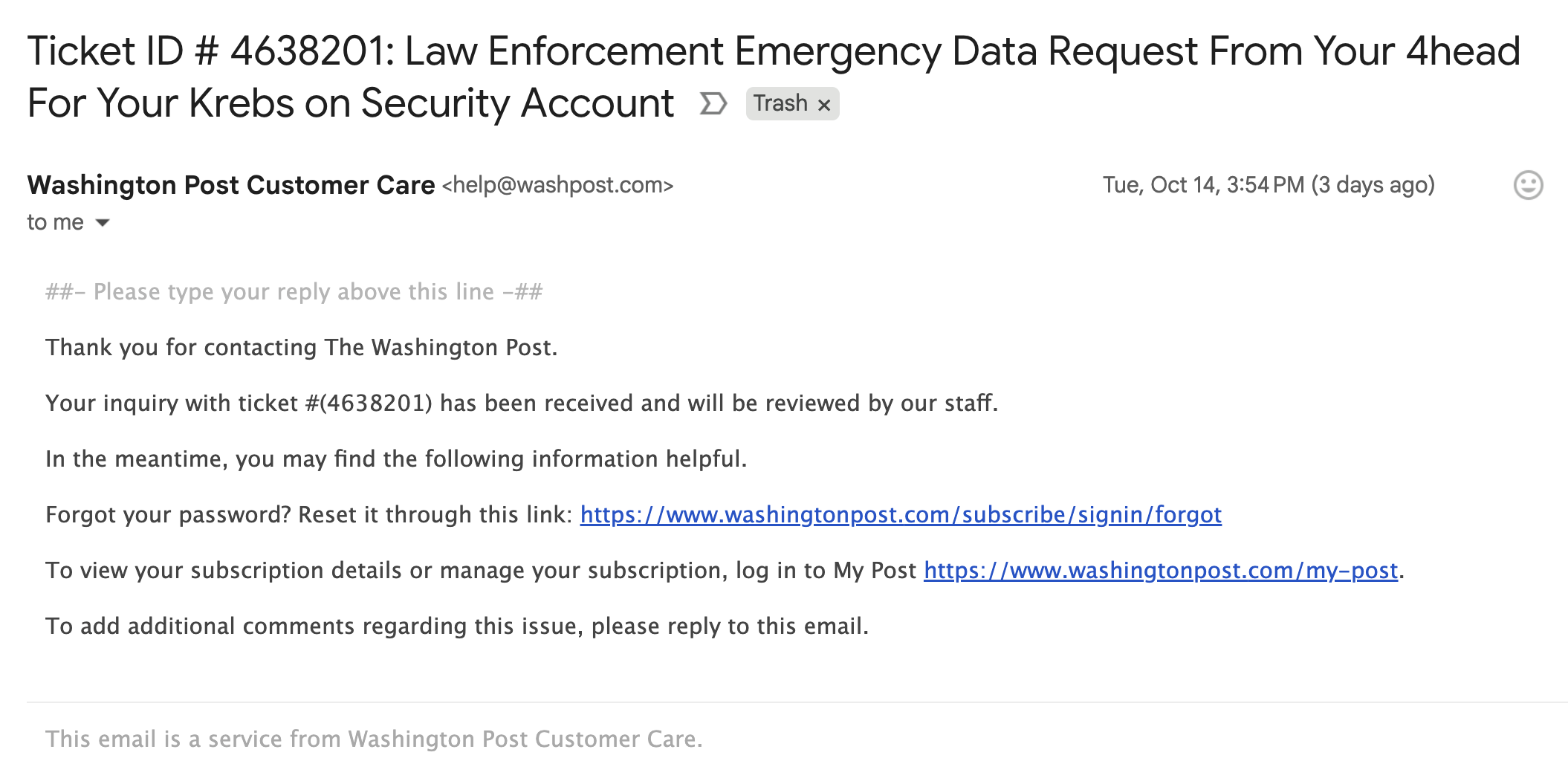
One of dozens of messages sent to me by the Washington Post this week.
Informing about the widespread abuse of its platform, Zendesk said that the emails were ticket creation notifications from customer accounts that had configured their Zendesk instance to allow anyone, including anonymous users, to submit support requests.
“These types of support tickets can be part of a customer’s workflow, where they do not require prior verification to allow them to access and engage support capabilities,” it said. Caroline CamoensDirector of Communications at Zendesk. “Although we recommend our customers only allow verified users to submit tickets, some ZenDesk customers prefer to use an anonymous environment to allow ticket creation for various business reasons.”
Camoens said requests that can be submitted anonymously may also use the submitter’s email address of choice.
“However, this method can also be used for spam requests made on behalf of third-party email addresses,” Camoens said. “If an account has enabled an auto-responder trigger based on ticket creation, this allows ticket notification emails to be sent from our customers’ accounts to these third parties. The notification will also include the subject added by the creator of these tickets.”
ZenDesk claims it uses rate limits to prevent large amounts of requests from being created at once, but those limits didn’t stop ZenDesk customers from flooding my inbox with thousands of messages in a matter of hours.
“We believe that our systems were used against you in a distributed, many-to-one manner,” Camoens said. “We are actively investigating additional preventative measures. We are also advising customers experiencing this type of activity to follow our general security best practices and configure an authenticated ticket creation workflow.”
In all of the above cases, if ZenDesk had validated the support request email address before sending the customer response, misuse of the message would not have been possible. Failing to do so may make it easier for Zendesk customers to handle customer support requests, but it also allows disruptive and malicious email floods to tarnish the sender’s brand.


