An important resource that rely to cyber security professionals worldwide to identify, reduce and fix security weaknesses in software and hardware is at risk of breaking. Federally funded, non-profit research and development organization Mitar Today warned that its contract is to maintain General weaknesses and exposure (CVE) Program – which is traditionally funded by the Department of Homeland Security – ends on 16 April – on 16 April.
A letter from the Miter Vice President Yosry Barsoum, warning that the funds for the CVE program will end on April 16, 2025.
Thousands of security flaws are found and reported in the software, and these weaknesses are eventually assigned their own unique CVE tracking numbers (eg). Cve-2024-43573Which is one Microsoft Windows Bug that Redmund was packed last year).
There are hundreds of organizations – as known as CVE numbering officers (CNAS) – Which are authorized by MITER to best these CVE numbers at new reported flaws. Many of these CNAs are country and government-specific, or individual software vendors or vulnerable disclosure are bound by platforms (aka bug bounty programs).
Simply put, miter is a significant, widely used to centralize and standardize information on software weaknesses. This means that this information is plugged into a pipeline supply cyber safety equipment and an array of services that help organizations identify and patch the safety holes – ideally malware or malcontants can take naps through them.
“What exactly the CVE list provides, is a standardized way to describe the severity of that defect, and a centralized repository listing is which products are defective and need to be updated,” Matte tatChief Operating Officer of KorilliumA cyber security firm that sells phone-rituals to find security flaws.
In a letter sent to CVE Board today, MITER Vice President Yosari barsoum Warned that on April 16, 2025, “Current contracting routes for MITER will end to develop, operate and modernize CVE and many other related programs.”
“If there was going to be a break in service, we estimate many effects for CVE, including the national vulnerability database and advice, equipment vendors, event reaction operations and all methods of significant infrastructure,” Barsum wrote.
Miter said that cvesonsecurity Cve website listing weaknesses will increase after the funding ends, but new cves will not be added after 16 April.
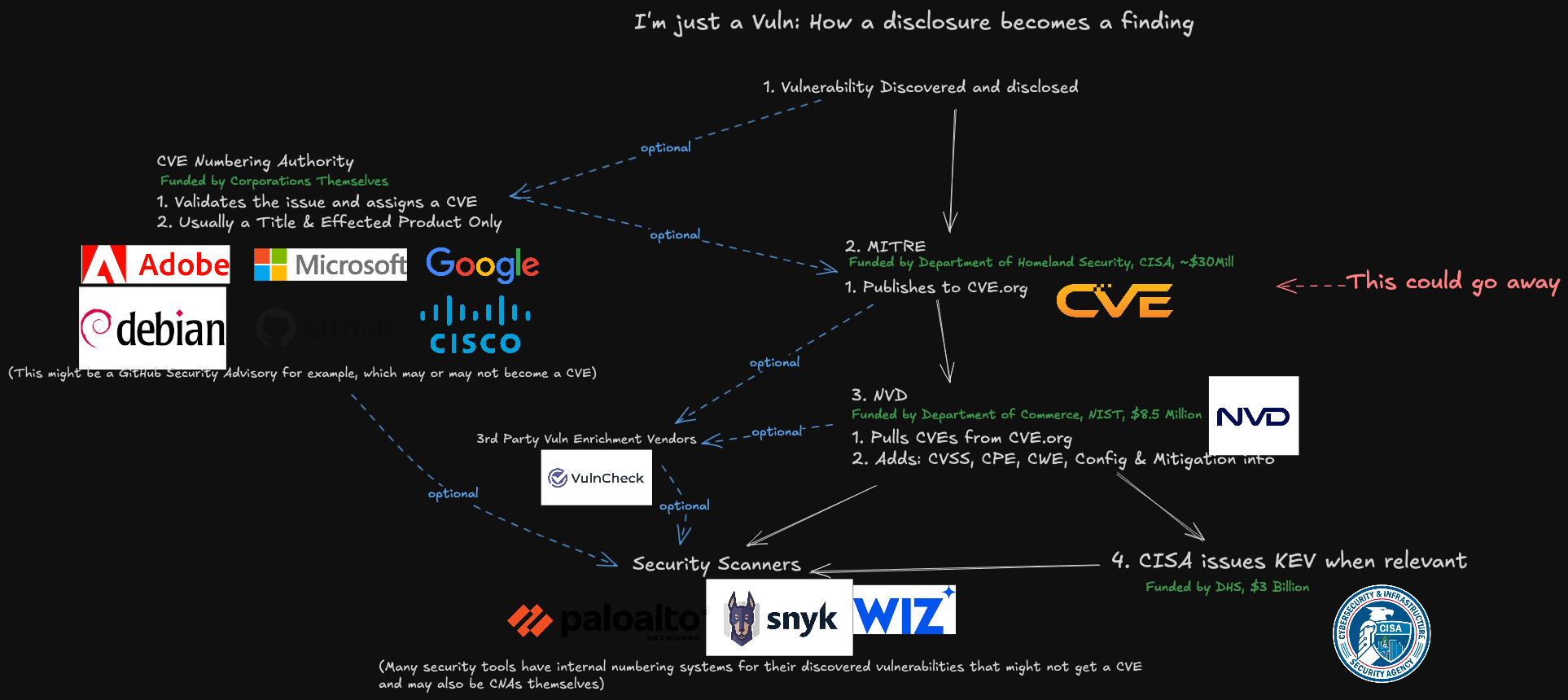
How a vulnerability becomes a CVE, and a representation of how that information is consumed. Image: James Barthoti, Latio Tech, LinkedIn.
DHS officials did not immediately respond to the remarks request. The program is funded through DHS Cyber security and infrastructure security agency (CISA), which is currently facing deep budget and staff cuts by the Trump administration. CV contract Available on usaspending.gov that the project was awarded around $ 40 million last year.
Former CISA Director Gane easterly The CVE program is a bit like the Devi decimal system, but for cyber security.
“It is a global catalog that helps everyone – using a uniform reference system helps to organize and organize and organize and organize the weaknesses, software vendors, researchers, governments and talk about the weaknesses,” Easter said. A post on LinkedIn“Without this, not everyone is using a separate catalog or any catalog, no one knows whether they are talking about the same problem, the defenders ruined the precious time what is wrong, and the worst, the danger actor takes advantage of the confusion.”
John hamondMajor security researchers in managed security firm Hunt, Told Reuters When he listened to the news, he took a loud oath that the funding of CVE was in danger, and losing the CVE program “would be like losing language and lingo, which we used to solve problems in cyber security.”
“I can’t really help, but think it’s just an injury,” Hammond said, who posted A YouTube video To vent about the situation and alert others.
Many people close to the case said that Krebssnasurity is not the first time the budget of the CVE program has been left in the funding limbo till the last time. Barsaum’s letter, which was clearly leaked, as an expectation, is making a lot of effort to the government to continue the role of Matter in support of the program. “
TAT said that without CVE program, risk managers inside companies would need to continuously monitor at several other places for information about new weaknesses that may endanger their IT network safety. Meaning, it can be more common that software updates are incorrect-primarily, companies have long deployed with hacked software.
“Hopefully they will solve it, but otherwise the list will be rapidly out and stops being useful,” he said.
Update, April 16, 11:00 am ET: CVE Board today announced the construction of a non-profit unit CVE Foundation This will continue the program work under a new, unspecified money mechanism and organizational structure.
Since its inception, the CVE program has operated as an initiative funded by the US government, providing oversight and management under the contract, “written in a press release. “While this structure has supported the development of the program, it has also raised long -term concerns about the stability and neutrality of a globally reliable resource among the members of the CVE board.
Organization website, Thecvefoundation.orgIs under the age of one day and currently there is no material other than press release, which is herald to its construction. The announcement states that the Foundation will issue more information about its structure and transition plan in the coming days.
Update, April 16, 4:26 pm ET: Miter released a statement today, stating that “identified old funds to keep the programs running.


