Last week, officials from at least two American states announced the arrest of Chinese citizens independently, using mobile devices to abolish a novel form of tap-to-add fraud. The details released by the authorities so far indicate that mobile wallets being used by scammers were made through online fishing scams, and that the accused were relying on a custom Android app to relay tap-to-pay transactions from mobile equipment located in China.

Picture: WLVT-8.
Officers in Naxville, Tennessee last week Said He arrested 11 Chinese citizens accused of buying thousands of dollars gift cards on local retailers along with mobile wallets made through online fishing scams. The NOM County Sheriff Office said that arrest is considered the first in the nation for a new type of tap-to-pay fraud.
Responding to questions about the scheme, NOX County said that when it seems that fraudsters are buying only gift cards, they are actually using several transactions to buy various gifts cards and carrying their scam from the state to the state.
The chief deputy of the NOX County, “These criminals are traveling nationwide using the stolen credit card information to buy gift cards and launde funds.” Burney Leone wrote. “During Monday’s operation, we recovered gift cards worth more than $ 23,000, all bought without any victim’s information.”
The suspects were asked for nuances about mobile devices seized, Leon said, “Tap-to-Pe Fraud includes a group Using Android phones to operate Apple pay transactions Using the stolen or compromised credit/debit card information, ”(added).
Lyon refused to offer additional nuances about the mechanics of the scam citing the ongoing investigation.
Ford meril Works in safety research SolitudeA CSIS Security Group Company. Meril said that there are no several legitimate use cases for Android phones to broadcast Apple Pay transactions. That is, he said, until he is running a custom Android app, which Krebssnasurity wrote about the last month as a part of a deep dive in the operation of Fishing Cartel in China that is breathing new life in the payment card fraud industry (aka “carding”).
How are these China-based fishing groups getting stolen payment card data and then loading it on Google and Apple phones? All this starts with fishing.
If you own a mobile phone, the possibility is excellent that in the last two years it has received at least a fishing message that makes it spoiled. American Postal Service It is believed to have some outstanding delivery fee, or assembled to collect an SMS that pretends to be a local toll road operator, which warns a criminal toll fee.
These messages are being sent through sophisticated fishing kits sold by several cyber criminals located in the mainland China. And they are not traditional SMS fishing or “sly“Messages, as they completely bypass the mobile network. Rather, missiles are sent Apple IMESSAGE Through service and through RCSFunctionally on equivalent technology Google Phone.
Those who enter their payment card data on one of these sites will be told that their financial institution needs to verify small transactions by sending a passcode on the customer’s mobile device. In fact, that code will be sent to the victim’s financial institution in response to the request of the fraudsters, which is to connect the fish data data to the mobile wallet.
If the victim provides a one -time code, the fishers will link the card data to a new mobile wallet with Apple or Google, which will load the wallet on a mobile phone controlling scammers. These phones are then loaded with several stolen wallets (often between 5–10 per device) and scammers on telegram are sold in bulk.
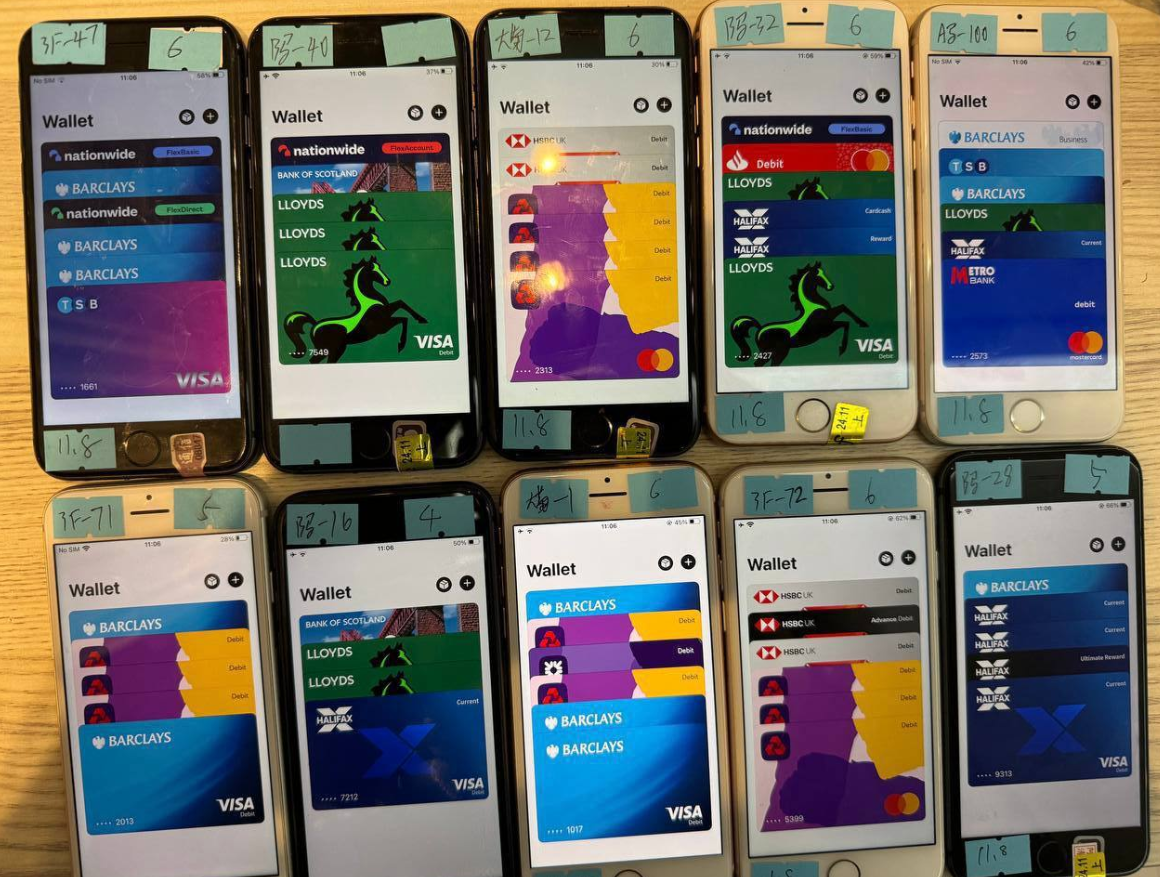
A popular Chinese smishing kit shows 10 mobile phones for the seller to sell an image of the telegram channel, each loaded with 5-7 digital wallets from various financial institutions.
Meril found that one of the minimum Chinese fishing groups sells Android app called “”Z-NFC“It can relay a valid NFC transaction anywhere in the world. The user simply waves its phone on a local payment terminal that accepts Apple or Google Pay, and the app relays the NFC transactions on the Internet with a phone in China.
Regarding the suspects arrested in Tennessi, Meril said, “If it was not the NFC relay app, I would be surprised.”
https://www.youtube.com/watch?v=ekqzjpaxb4c
Meril said that the Z-NFC software can work from anywhere in the world, and that a phishing gang provides software for $ 500 per month.
Meril said, “This NFC can enable both of both in tap-to-pay as well as any digital wallet.” “He also has a 24-hour support.”
On 16 March, ABC affiliation in Sacramento (ABC10), California. A broadcast a broadcast About two Chinese citizens were arrested after using an app to run a stolen credit card at a local target store. The news story quoted the investigators as saying that men were trying to buy gift cards using a mobile app which was cycled through more than 80 stolen payment cards.
ABC10 reported that while most of those transactions were rejected, the suspects still closed with a gift card of $ 1,400. After his arrest, both men allegedly admitted that they were being paid $ 250 per day to conduct fraud transactions.
Meril said that it is not uncommon for fraud groups to advertise such work on social media networks, including Tiktok.
A CBS News Story Sacramento arrests said that one of the suspects tried to use 42 separate bank cards, but 32 was rejected. Nevertheless, the man was still allegedly able to spend $ 855 in transactions.
Similarly, the alleged partner of the suspect tried 48 transactions on different cards, succeeded 11 times and spent $ 633, CBS said.
“It’s interesting that so many cards were rejected,” said Meril. “One reason may be that banks are getting better in detecting such fraud. Second, it may be that the cards were already used and hence these people were already flagged for fraud before they had a chance to use these people. So these people may have some elements to store, to see what it does, and if they are not on their own.”
The investigation by the Meril of Telegram sales channels for these China-based fishing gangs suggests that their fishing sites are actively operated by fraudsters who sit in front of the spacious rack of Apple and Google phones, used to send spams and respond in real time.
In other words, the phishing websites are operated by real human operators until new messages are being sent. Meril said that criminals send only a dozen messages at a time, likely it is likely that completing the scam leads to manual work by human operators in China. Finally, most of the one bar code used for mobile wallet provisioning is usually good for a few minutes before ending.
For more information about how China-based mobile fish groups operate, see how fish data turns into Apple and Google Wallet.

Ashtray says: You are fishing all night.


