If you feel that your safety questions are a solid backup for your password, you may be surprised. Hackers have clever ways to highlight those answers, and this is often easy to think.

Social media is a goldmine for anyone trying to do your personal story together – and hackers know it. Most people carelessly share the events of major life online, such as birthdays, anniversary, pets names and schools. However, someone is trying to crack your safety questions for anyone, it is not apathy. He is Intel.
Say that your safety question is “What is your favorite film?” Through their X account, two scroll lions reveal their love for the king. Or maybe your Instagram Bio says “Dog Mom to Max,” and your answer is “What was your first pet’s name?”

Connected
Here is how scammers can take advantage of your social media profiles
Knowing their ways is the first step!
This type of snuping does not require fancy equipment. All hackers need your name, your profile and a little patience. They will leave the old post, tagged photos and even your friends. If your privacy settings are widespread, you are essentially submitting answers.
Even private accounts are not safe. If a hacker follows you, perhaps through a fake profile, your post becomes accessible. A harmless memory lane post can turn into a breadcrumb trail for your accounts.
7
Using fake “fun” quiz
It is likely, you have seen a version of those playful quizes on social media, such as “What is your royal name?” Or “Can we guess your age based on your favorite foods?” They are usually designed as harmless fun, but they are one of the most common privacy blunders that you can make on social media.
Use these quiz to collect the exact type of personal details associated with safety questions, or least shady data scrapers, safety data. They reduce your guard with humor and privatization so that you forget that you are essentially handing over a map for your digital identity.
6
See details in public records
Sometimes hackers do not need tricks. They only use public records.
Marriage certificate, property records, voter registration, and even old year books can be a rich source of answers to safety questions. Information like your mother’s first name, childhood address, or birthplace is often away from a few discoveries.
Connected
How to remove your personal data from public record websites
Do not want your information to fall into the wrong hands? Learn how to remove your personal information from the web!
For example, if your safety question is “in which city you were born?”, An old birth declaration can easily reveal it. Similarly, a marriage license can highlight the name of the father.
A determined hacker does not even need to know you personally. They just need your name and a little firmness. Public records can be filled in the rest.
5
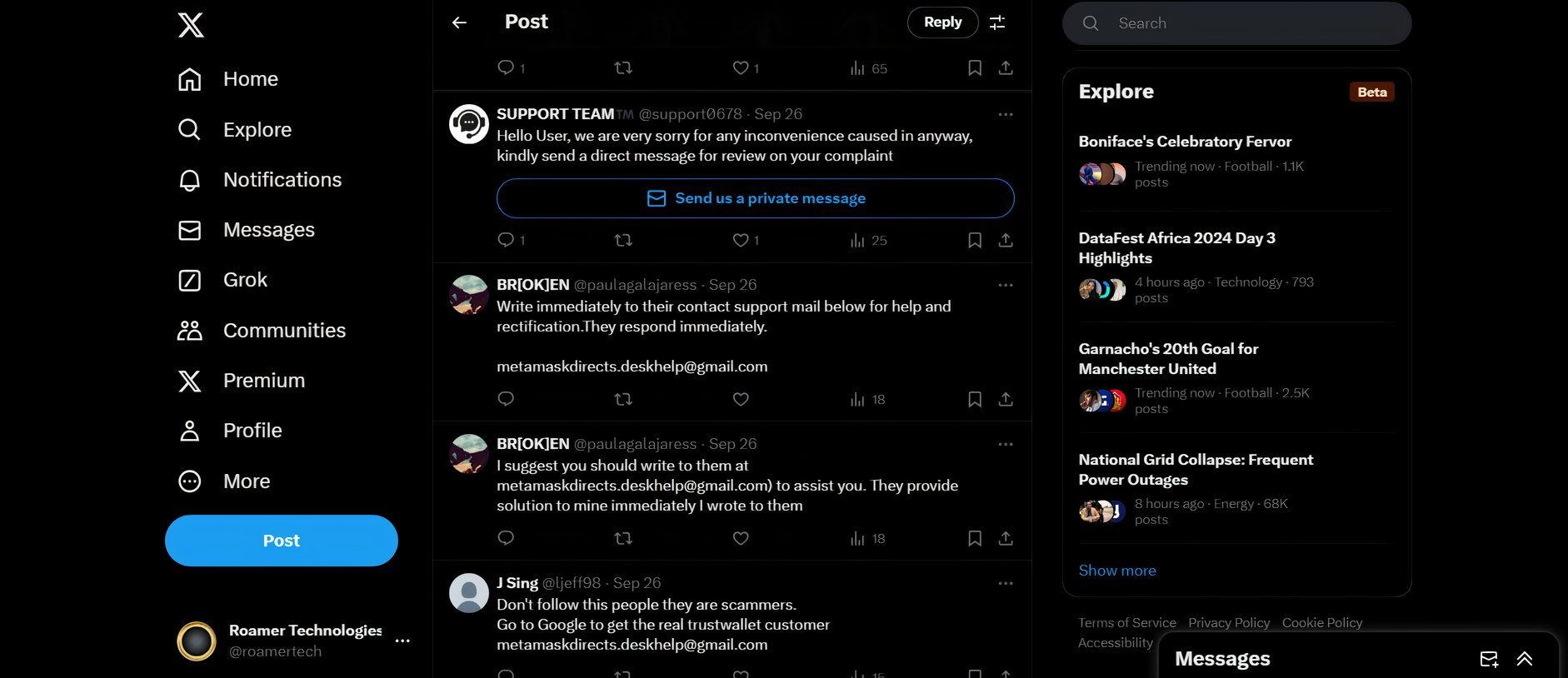
Search through old forum post
You may think that the old forum posts are safe because most of the platforms were anonymous. But hackers know that oblivion is not bulletproof – especially when people accidentally leave a mark.
You may use a forum handle that matches the part of your email address. Maybe you have posted about your hometown, your first pet or your high school mascot. Even small details like you graduate or your favorite sports team can start connecting dots to you.
It does not take hacking skills, either. A hacker with patience may find some keywords with old forums, cross-reference user names, or Google with your name. The forums can barely remember that you can still swim around the public archives to join, quietly leaked bits of your personal history.
Anonymity helps, but if you leave enough breadcrumbs, the old posts can still cheat you. And when hackers are hunted to answer your safety questions, even the smallest clue may be sufficient.
4
Using leaked data from other sites
Data violations are like a jackpot for hackers. When a site is hacked, it is not only a user name and password that is leaked. Sometimes your safety questions are leaked, too.
For example, it says that you establish an account a year ago on a platform. Do you use “Arsenal” “What is your favorite sports team?” And forgot about it. If that site is violated and your answer is not encrypted, hackers can use it today to reach your important accounts.
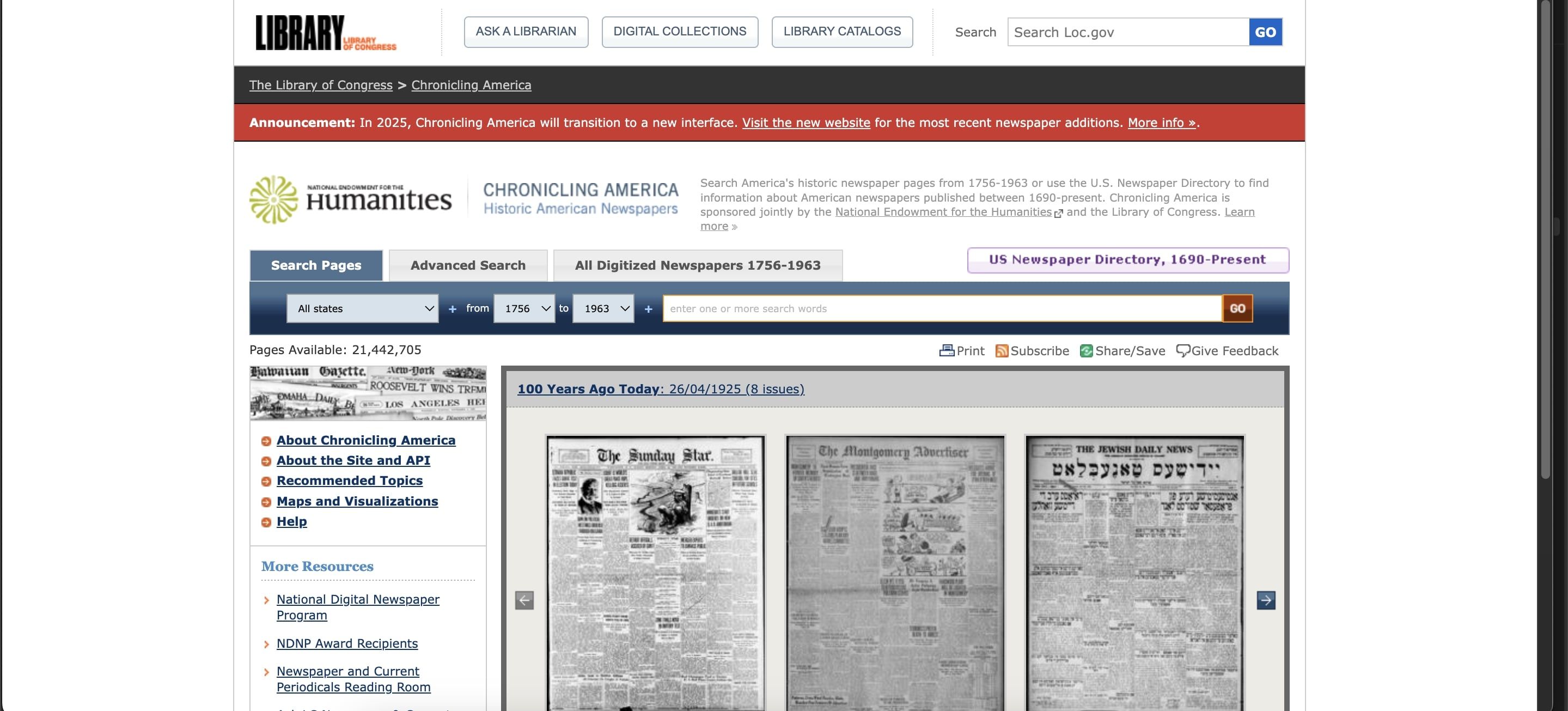
Reusing security answers on sites is as dangerous as reusing the password. Once your information goes out, hackers use special equipment to cross-refer it. Like using equipment Have i been pwned To see if your data has been revealed. And always treat safety answers like passwords of one-time use: unique to every account.
3
Fake support chat making
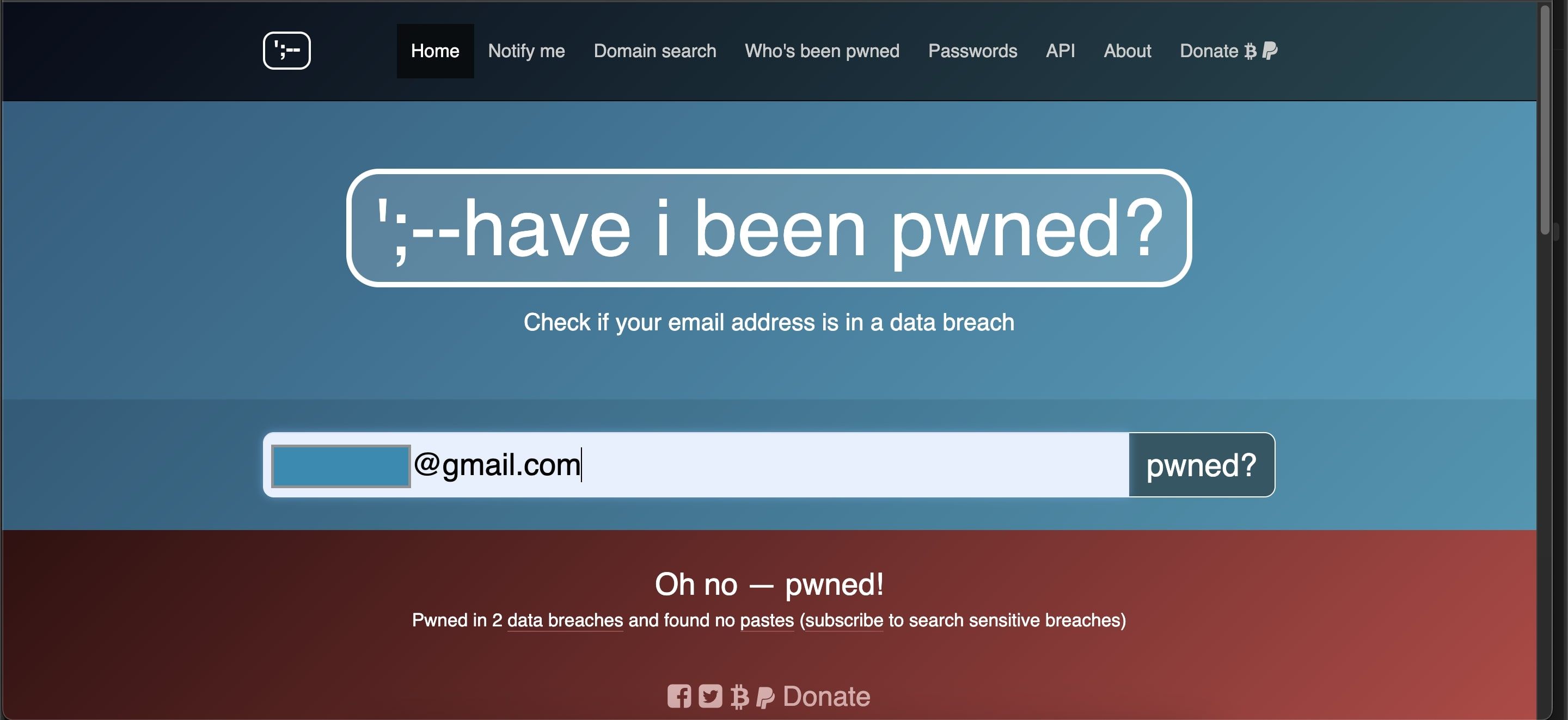
It is a more sophisticated but disastrous effective: fake customer aid chat.
It usually begins with an email, DM, or pop-up that mimics your bank, email provider or favorite store. The fake support agent will ask you to confirm your identity by answering safety questions.
These fake chats often imitate branding, language and even time, for example, during a real site outage. And because they feel individual, you are more likely to follow without thinking. Once you hand over those answers, hackers can get access to your account by resetting your login credentials.

Connected
Before they fool me
I can see through some tricks through their plans.
The golden rule here is simple. Valid support representatives will never ask for your safety questions through chat, email or direct message. If you receive that kind of request, close the chat and verify directly through the official site.
2
Cheat your friends in sharing details
Hackers know that even if you are alert, you cannot be friends. Getting personal details by cheating on people is surprisingly easy to trust you.
Sometimes it begins with a fake profile that pretends to be an old classmate or mutual friend. They slide in conversation, ask about “good old days”, or start a game that feels harmless. Before your friend knows this, he carelessly mentioned where you have grown up, your childhood pet name, or even your favorite teacher.
Even simple as an indifferent Facebook post can be very high. A friend tags you in the picture of an old year book or joking about your first car, can give hackers in the same way you can type a word at any time.
This is a timid strategy because it looks very natural. Friends trust each other. Hackers exploited that belief to dig for them. If you are serious about safety, remind your internal circle to be cautious.
1
Obstruct normal answers
Sometimes, hackers also do not have to snoop. They just guess, and unfortunately, they are often correct.
“What is your favorite color?” Lead to forecasted answers like blue. The names of pets often include Max, Bella or Lucky. Even something like “Mother’s Medane Naam” often leads to common last names such as Smith, Johnson or Garcia. Other answers are equally approximate: for example a lot of people respond to “Dream Vacation” with “Paris”.
Hackers sometimes automate this estimate, cycling through the most popular answers until they become lucky. Without wrong efforts, without strong site safety, they may require some efforts.
Tech uve is simple. Treat safety questions answers like password. Do not go with truth if it is very easy to guess the truth. Make it a passfreese, some fruitless, or better yet, use a password manager to store random answers.
Safety questions may feel like harmless backups, but for a hacker, they are an unlocked side door. Hackers do not always need to break with cruel force. Sometimes they just go on using the details that you laid around.