
A China-focused APT danger actor named “Thewizards”, has attacked the Adv6 networking facility to launch Adversary-In-Middle (AITM) that updates kidnapping software to install Windows Malware.
According to the ESET, the group has been active since at least 2022, targeting institutions in the Philippines, Cambodia, the United Arab Emirates, China and Hong Kong. The victims include individuals, gambling companies and other organizations.
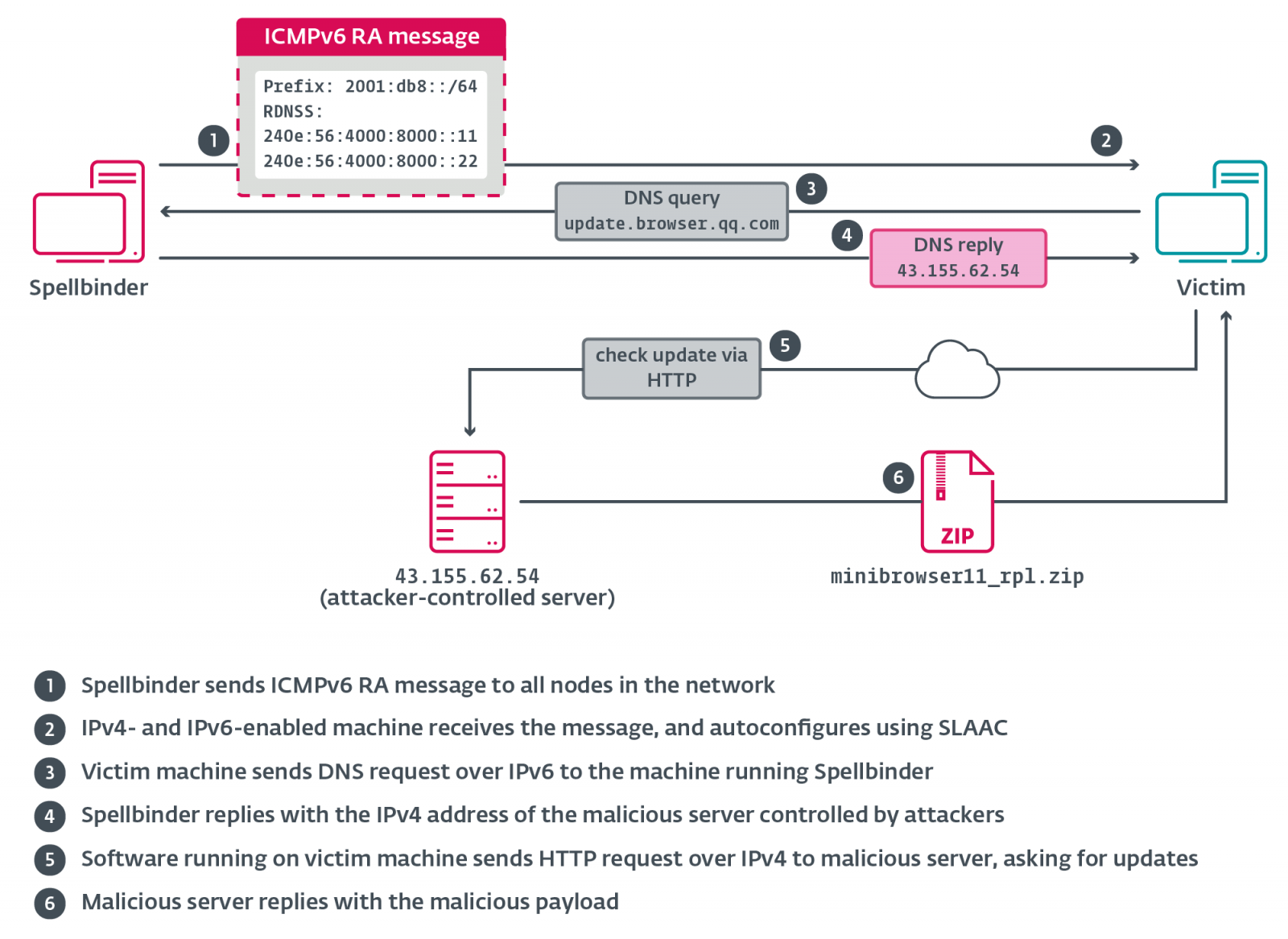
Attacks use a custom tool dubbed by ESET that misuses the IPV6 Stateless Address Autochonfigation (SLAAC) feature Slack attack,
The Slaac IPV6 is a feature of the networking protocol that allows devices to automatically configure its own IP address and default gateway without the need for the DHCP server. Instead, it uses router advertising (RA) messages to get IP from the IPV6-supported router.
The Spelbinder Tool of the hacker misused this feature by sending Spbed RA messages on the network, making the nearby systems automatically receive a new IPV6 IP address, new DNS server and a new, favorite IPV6 gateway.
This default gateway, however, is the IP address of the spellbinder tool, which allows it to disrupt communication and reunion traffic through an attacker-controlled server.
“Spelbinder a multicast RA packet sends every 200 MS to FF02 :: 1 (” all nodes “); Windows machines in the network with IPV6 competent through Autoconphiger Stateless address autoconfiguration (Slaac) using the information provided in the RA message, and start sending IPV6 traffic to the spellbinder running machine, where the packet will be intercepted, analyzed, and where applicable, will be replied, “ESET tells.
Source: ESET
ESET stated that deployment of spellbinder using a collection called avgapplicationframehosts.zip, which comes out in a directory mimicing valid software: “%programfiles%\ AVG technologies.”
There are a valid copy of avgapplicationframehost.exe, wsc.dll, log.dat, and winpcap.exe within this directory. Winpcap executable is used to side-load the malicious wsc.dll, which loads the spellbinder into memory.
Once a device becomes infected, the spellbinder begins to capture and analyze the network traffic to add specific domains, such as related to the Chinese software update server.
ESET says that malware monitors for domains related to the following companies: Tencent, Baidu, Xunlei, Youku, Iqiyi, Kingsoft, Mango TV, Funshion, Yuodao, Xiaomi, Xiaomi Miui, PPLIVE, Meitu, Quihu 360, and Baofeng.
The tool then redirect the requests that download and install malicious updates, which deploy a back door called “Vizardate”.
The Vizardont Backdor continues to reach the infected device to the attackers and allows them to install additional malware as required.
To protect against this type of attacks, organizations can monitor the IPV6 traffic or close the protocol if it is not necessary in their environment.
In January, ESET also reported on another hacking group called “Blackwood”, kidnapping the WPS office software update facility to install malware.


