
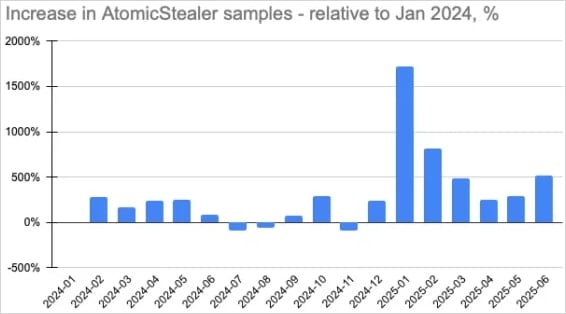
The malware analyst discovered a new version of the atomic McOS information-star (also known as ‘AMOS’), which comes with a back door, continuously accessing the system of compromised for the attackers.
The new component allows arbitrary remote orders to execute, it avoids the reboot, and allows to maintain control indefinitely on the infected hosts.
McPo’s Cyber Safety Division Munlock analyzed the back door in nuclear malware following a tip from independent researcher g0njxaA close supervisor of infostealer activity.
Researchers say, “The Amos Malware Campaign has already reached more than 120 countries with the United States, France, Italy, United Kingdom and Canada.”
“The backdoor version of the nuclear Macos Steler now has the ability to achieve full access to thousands of MAC equipment worldwide.”
Source: Moonlock
Atom stealing
The atomic theft, which was first documented in April 2023, is a Malware-A-Sarvis (MAAS) operation that has been promoted for a huge membership of $ 1,000 per month on telegram channels. It targets the user password stored on MACOS files, cryptocurrency extensions and web browsers.
In November 2023, it supported the first expansion of the ‘Clearfec’ campaigns on McOS, while in September 2024, it was seen in a massive campaign by Cybercrime Group ‘Marco Polo’, who deployed it on Apple Computer.
The moonlock reports that atoms have been transferred from comprehensive distribution channels such as cryptore sites, for targeted fishing for freelancers, along with targeted phishing aimed at atoms aimed at the purpose of cryptocurrency owners.
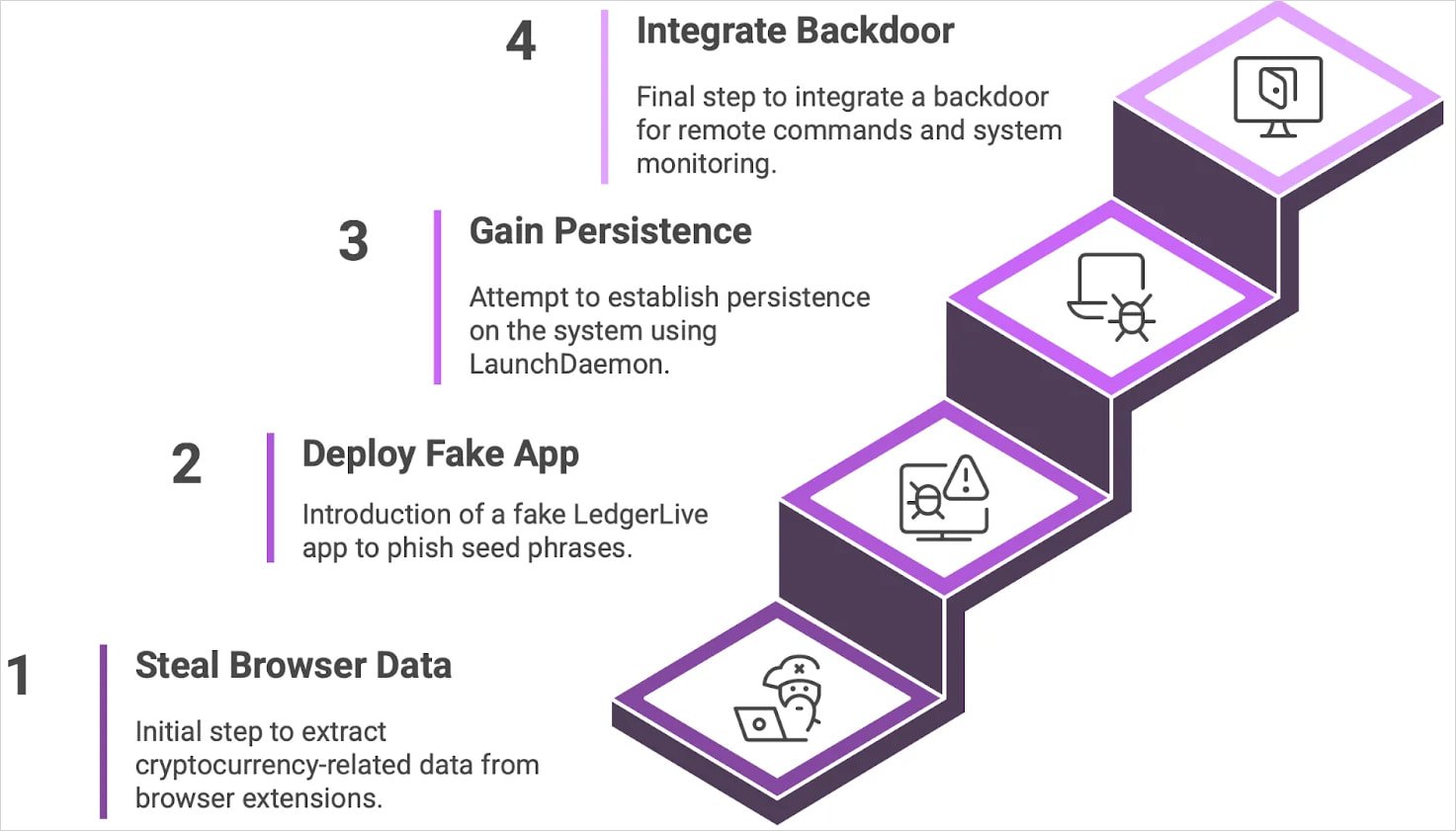
Malware analyzed version comes with an embedded backdoor, using launchdamone to avoid reboots on Macos, ID-based victim tracking and new command-and-control infrastructure.
Source: Moonlock
A previous door in your Mac
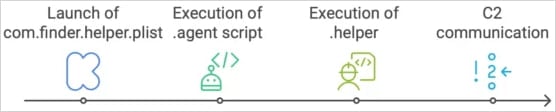
The core backdoor is a binary executable named ‘.helper’, ‘Downloaded and saved as a hidden file in the victim’s home directory, as post-transmission, Researchers say,
‘.Gent’ (hidden) (hidden) name ‘in a loop as a log-in user.
This action is taken with high privilements using a user password stolen during the initial transition phase under a false excuse. Malware can then execute the command and convert the ownership of the launchdmon plastist to the ‘root: wheel’ (superuser level on MACOS).
Source: Moonlock
The backdor is allowed to perform the danger actors to execute the command from a distance, log, introduce additional payloads, or to detect lateral movement capacity.
To avoid detection, using ‘System_Profiler’ checks the backdoor for a sandbox or virtual machine environment and also includes string obfusation.
The development of atomic malware shows that Macos users are becoming more attractive goals and malicious campaigns are rapidly sophisticated for them.



