
A DDOS mitigation service provider in Europe was targeted in a large -scale denial attack that reached 1.5 billion packets per second.
The attack occurred from thousands of IOTS and Mikrotic router, and was reduced by Fastnetmon, a company, which provides protection against the disruption of the service.
“The attack reached 1.5 billion packets per second (1.5 GPPS)-one of the largest packet-by floods was publicly revealed,” Fastnetmon says In a press release.
“Malicious traffic was mainly a UDP flood started with the IOT device and the IOT device and the router in the more than 11,000 unique networks worldwide,” the company explains.
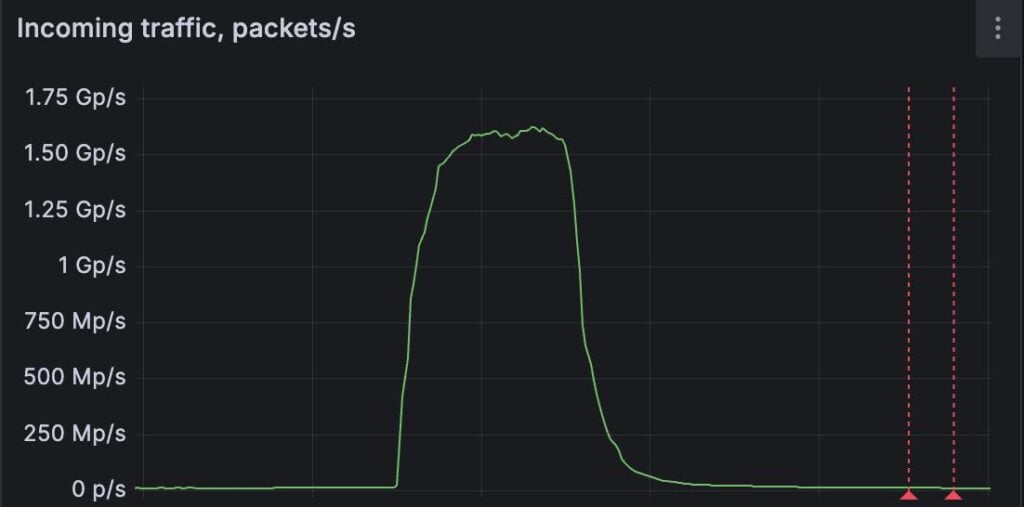
Source: Fastnetmon
Fastnetmon did not name the targeted customer, but described it as a DDOS scrubbing provider. These services specialize in filtering malicious traffic during DDOS attacks through packet inspection, rate limited, captcha and discrepancy detection.
The attack was detected in real time, and mitigation action was taken using the customer’s DDOS scrubbing facility. Measures included deploying the Access Control List (ACLS) on the edge router known for amplification capabilities.
The attack was reported by Internet Infrastructure Giant Claudflair announced that it came only a few days after blocking the Volumetric DDOS attack in history, which reached the second (TBPS) and 5.1 billion packets per second (BPPS) per second.
In both attacks, the target -achieved end was to eliminate processing capabilities and the cause of service outage.
Fastnetmon’s founder, Pavel Odintsov, commented that the trend of these massive attacks had become very dangerous, and the Internet Services Provider (ISP) level intervention at the Internet service provider (ISP) level needs to prevent this mass weapons of consumer hardware.
“What makes the matter notable is remarkable is the abuse of the oblique number of distributed sources and everyday networking devices. Without active ISP -level filtering, consumer hardware can be armed on a large scale” – – – – – – – – – – Fastnetmon
“The industry should work to implement detection logic at the ISP level,” says Odintsov so that they can stop outgoing attacks. “



