
Malware firmness technique Enable the attackers to maintain access to the concluding conclusion points despite system reboots, credential changes, or other disruptions. General methods include changing configurations, injecting the startup code and kidnapping valid processes.
These approaches ensure that malware or attackers are active, allowing malicious activities to continue without the need for re -discovery.
In this article, we will examine malware perseverance techniques, their effects and the nature of strategies to protect against them.
General malware firmness technique
Miter Att & CK framework lists a series of techniques used by danger actors to maintain firmness. Examples of malware perseverance techniques from the framework are given that allow the attackers to maintain long -term access to the concluding conclusion points:
T1053 – Scheduled Work/Job
Reverse misuse work scheduling features for running malicious code at frequent or set intervals. Built-in utilities such as task scheduler (Windows), Chrone (Linux), and Launch (Macos) may execute programs or scripts at specified time or in response to some events.
T1037 – boot or logon insurance script
The attackers configure the script to execute during the system boot or user logon, ensuring firmness or privilege increase. On Linux, like mechanism rc.local, Init.d.Or systemd is usually used to launch malicious codes in startups.
T1543 – Create or modify system process
System-level procedures such as Windows Services, Linux Damons, or McOS London agents run automatically in the background. Danger actors can establish or modify these procedures to execute malicious payloads on startups or during system operations.
T1136 – Create Accounts
Advisors can create new local, domains or cloud user accounts on the system of compromised to maintain access. With adequate privileges, these accounts can be used continuously for ongoing access without the requirement of remote access tools.
T1098 – Account Herfer
The account manipulation enables attackers to amend credentials, change group membership or to maintain access by bypassing security policies. For example, adding a ssh key ~/. SSH/Observed_Kies Remote frequent remote access without password requirement.
Effect of malware perseverance techniques
Malware firmness technique is designed to ensure that the attacker maintains long -term access to the compromised system. Below, we detect some effects of malware firm techniques.
extended time
Malware firmness techniques enable the attackers to stay in a compromise environment for a long time without the need for re -discovery.
This extended appearance, often for weeks or months, gives them time to plan the network, increase privileges and plan their next move before detection.
Reconsideration theft
Even after initial removal, attackers can get access by using scheduled functions, malicious services, or unauthorized user accounts such as firmness mechanisms.
This makes the cleaning efforts ineffective until all perseverance mechanisms are identified and removed.
Data exfigning
Constant access is often used in advanced persistent dangers (APTs), where attackers gradually exfiltrate data in an extended period to maintain prolonged infiltration and exploitation.
This sensitive information, such as credentials or commercial data, allows to be stolen over time.
Additional malware
With continuous access, the attackers can offer additional malicious equipment, including ransomware, backdoor or remote access trojan.
This can compromise the system or expand the surface of the attack throughout the network.
Compromise regulatory compliance
Malware firmness technique enables attackers to maintain unauthorized access to the system in an extended period.
This long -term access may violate regulatory standards such as GDPR, Hipaa and PCI DSS, requiring strict data security, system integrity and violation notification.
Protect your system from hidden hazards. Learn how the attackers use malware perseverance techniques, and how Vazuh helps you find out and stop them.
How to defend against malware firm techniques
Defection against firmness techniques requires a layered approach that combines the detection, prevention and reaction to the event.
Below are some major defense strategies:
1. patch management: Many perseverance techniques exploit the operating systems, applications or drivers known in drivers. By applying patch regularly on these components, you can significantly reduce the surface of the available attack.
2. File integrity monitoring (fim): FIM helps detect unauthorized changes in important files, such as startup scripts, scheduled tasks configuration, registry key or application binergies. By monitoring these sensitive files, you can identify when the attackers try to gain perseverance.
3. User Account Monitoring: Firmness often involves creating new user accounts, modifying existing people, or increasing privileges. Account construction, deletion and continuous monitoring of permission changes may reveal suspicious behavior.
4. Harden System Configuration: Securing the baseline configuration reduces the risk of attackers misusing the system facilities for perseverance. This includes disabling unused services, implementing strong password policies, limiting administrative privileges and using group policies to restrict autorun behavior.
5. Danger hunting: Conducting active danger allows security teams to detect hidden perseverance mechanisms that come out of automated equipment. This involves discovering suspicious behavior, such as abnormal process execution, scheduled functions, or long -dormant malware.
6. Closing point security: Deploying strong and popiate protection tools such as XDR enables the real -time monitoring of the activity and the known perseverance to block behavior. Modern closing point equipment can detect indicators such as registry change, service establishments and unauthorized script execution and react automatically.
How Vazuh Malware defends against perseverance techniques
Wazuh An independent and open source is the enterprise–safety solution that provides integrated Siem and XDR protection in several workloads.
It provides a centralized view for the danger detection and safety monitoring in the virtual, on-primeses, cloud-based and contained environments.
Wazuh offers many Capabilities To defend against malware perseverance techniques. These capabilities include, but not limited to:
- Active response
- File integrity monitoring
- Safety and configuration assessment (SCA)
- Log data analysis
- Vulnerable
Active response
The Wazuh active response modules enable the security teams to automate the response tasks based on the predetermined trigger, which helps them manage safety events efficiently. Automation ensures that high-primary events are immediately and constantly addressed.
Vazuh offers several underlying response scripts that can perform actions such as blocking malicious network traffic or removing infected files from the closing points monitored.
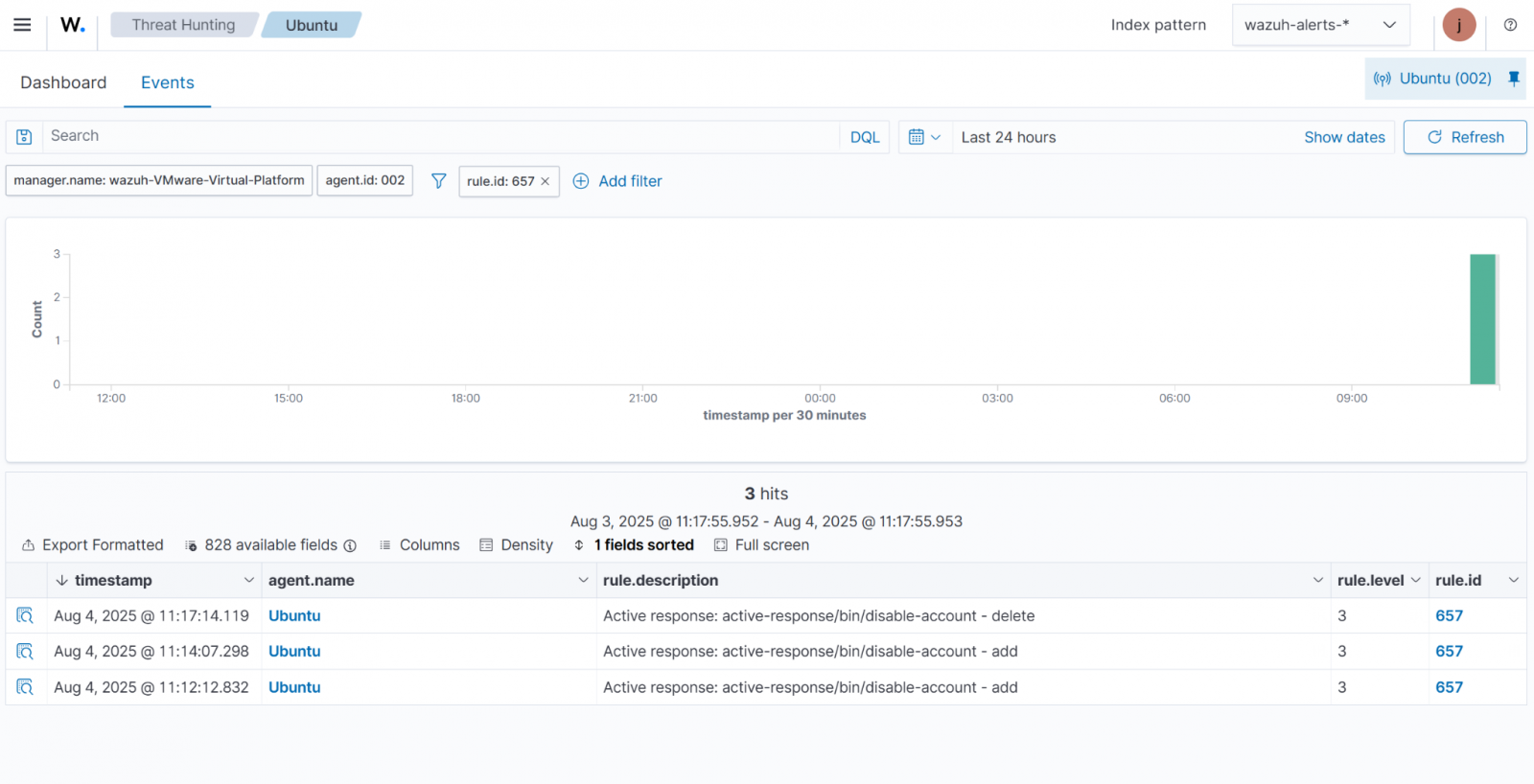
In the example below, the active response module neutralizes a Linux account that is targeted by the Brut-Force Login efforts.
File integrity monitoring
Wazuh fim monitors the module files and directors, when a user or procedure generates, modifies, or removes the monitoring files, produces alerts. This makes a base line by scanning and storing the check form and file characteristics.
When a user or procedure changes a file, the module compares its checks and compare the characteristics with baseline and trigger an alert when a mismatch is detected.
blog post Iconic How highlights wazuh fim modules detect malware firmness on Linux & Points.
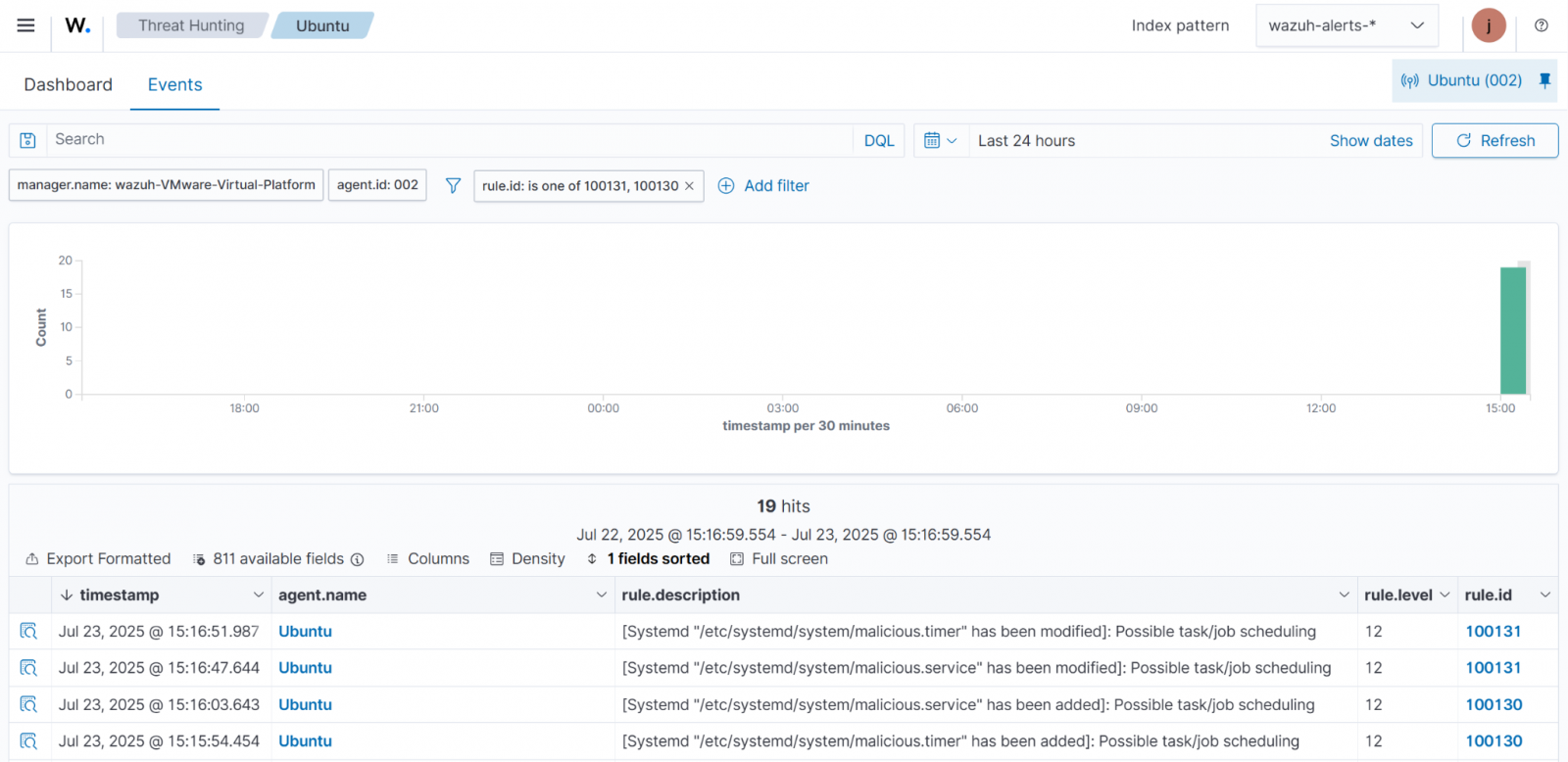
We use fim modules to monitor changes systemd Services and timer at a monitored closing point. since systemd Manage services and startup functions, monitoring its configuration files is important to detect unauthorized changes.
Safety and configuration assessment (SCA)
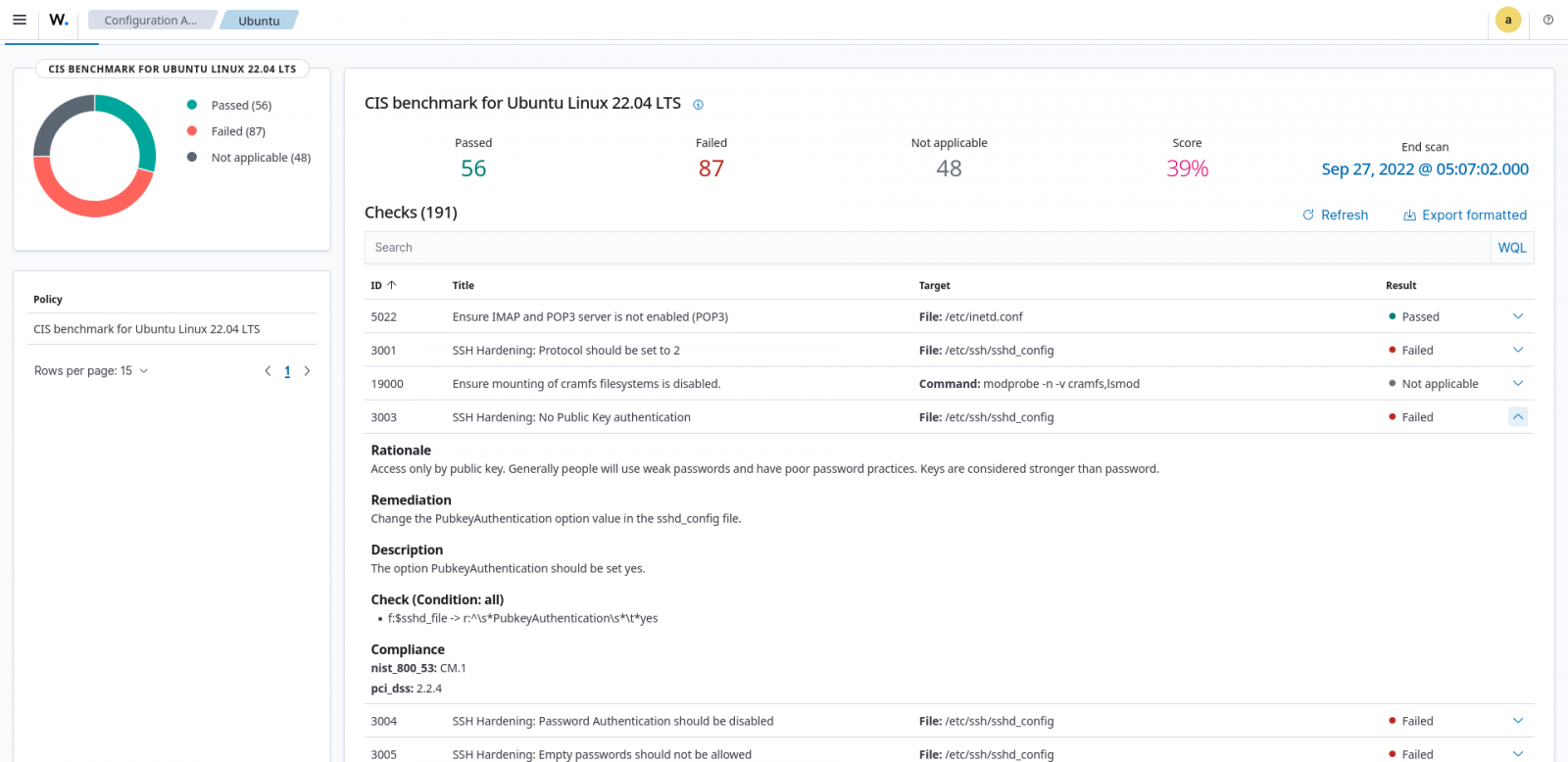
The system reduces the surface of the attack by eliminating hardening misunderstandings and unnecessary components. Wazuh SCA module helps to strict the system by scanning the closing points monitored to detect misconsiations and recommend therapeutic functions. It uses policy files to check the system settings, files, processes and registry entries.
For example, Wazuh SCA can assess whether it is necessary to change password policies, remove unnecessary software, disable unnecessary services, or audit network configuration.
Below in Figure 3, Vazuh SCA shows scan results fail Because public key authentication is not enabled for SSH.
Log data analysis
The Wazuh endens, providing visibility in your IT infrastructure by collecting, analyzing and storing logs from network devices and applications.
Wazuh agent, running at a monitored closing point, logs on the WAZUH server for analysis and logs on the system and application system and application. Log data analysis enables the identification of danger detecting, performing performance, troubleshooting, compliance, and discrepant activities.
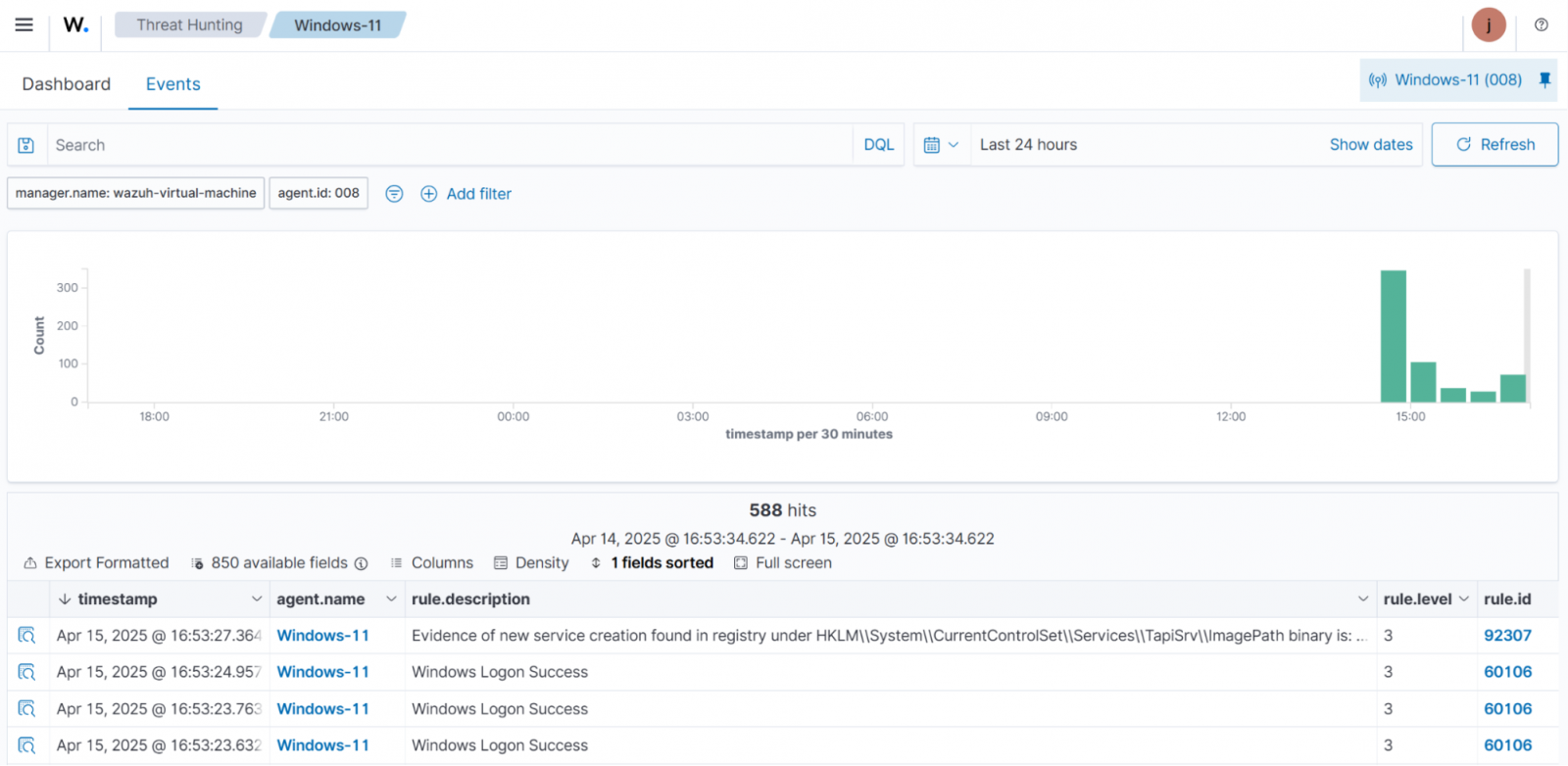
In Windows firmness techniques with vazuhThe Wazuh agent collects logs from a Windows andpoint and forwards them on the Wazuh server for analysis. It helps identify malware persistence signs of perseverance, such as unauthorized account construction, startup folders or registry changes in keys, and amendment in services.
Figure 4 below is detected to detect an amendment in a Windows service.
Vulnerable
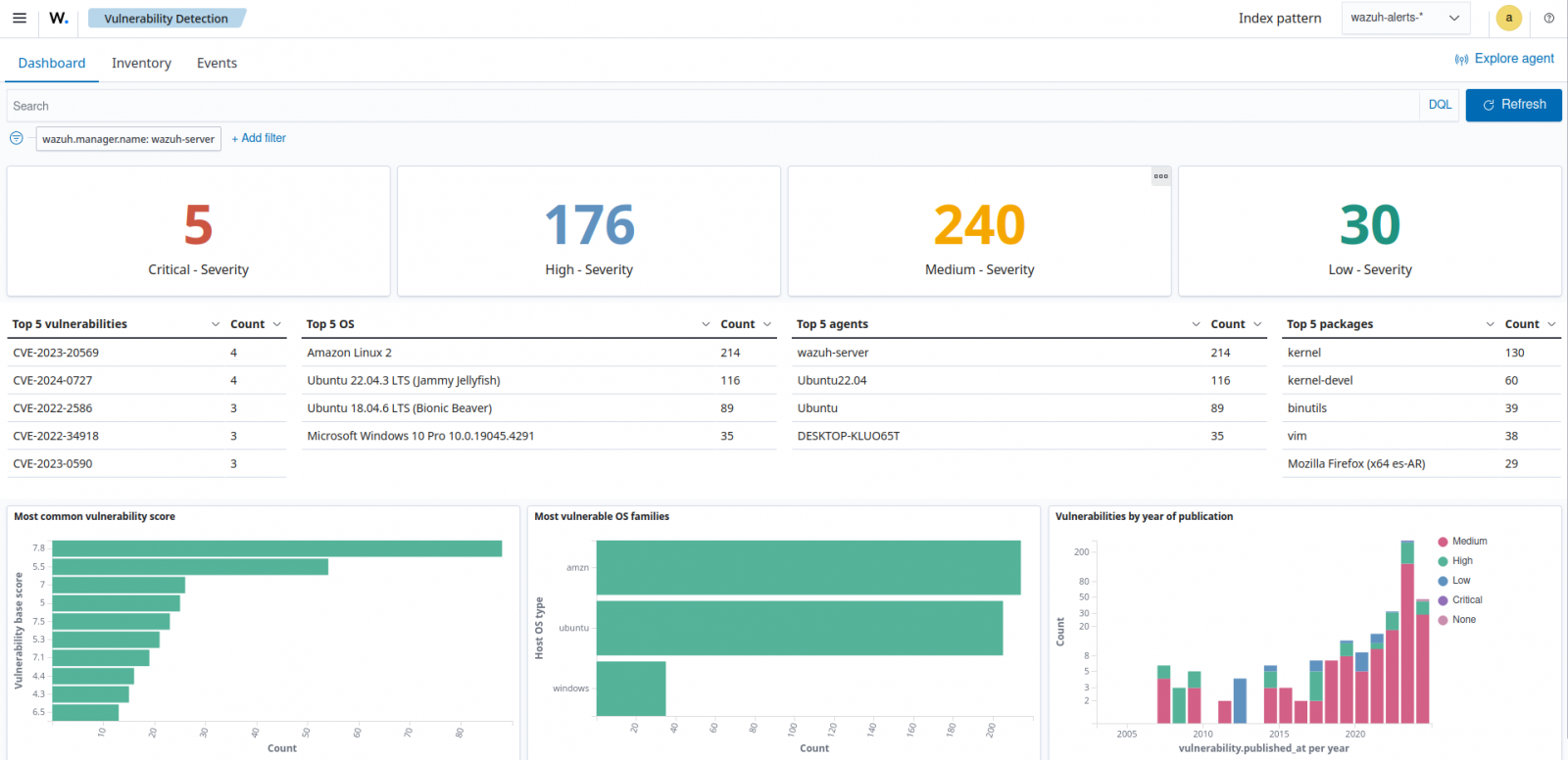
Wazuh Valnarability Detection Module identifies weaknesses in the operating system and establishes applications by corresponding software inventory with known vulnerability data Wazuh CTI platform. It generates an alert displayed on the Wazuh dashboard, giving a clear view of weaknesses at all monitored closing points.
This helps the security teams to take active measures to strengthen the system defense before reducing risk and exploitation.
The dashboard, which detects vulnerability in Figure 5 below, highlighted the severity of the package name, OS, agent, vulnerability ID, and the severity of detected weaknesses.
conclusion
Malware perseverance techniques enable attackers to maintain long -term access to the compromised systems, offering significant risks to organizational security.
These techniques require a multi -level approach to prevent that combine active measures, such as strict, fim, regular patching, danger hunting and user monitoring.
Wazuh increases the protecting the danger by providing several abilities to detect and respond to suspicious activity at the concluding concluding points, including firmness techniques. This enables security teams to monitor unauthorized changes, scheduled functions, abnormal procedures, account modifications and other indicators of compromise.
Start using Wazuh Today to strengthen your organization’s defense strategy. You can also connect with them community For professional support.
Sponsored and written by Wazuh,


