The entire concept of encryption once frightened me with flying with all those technical words. But after diving and really trying it myself, I turned out that the encryption is simple to use surprisingly and is incredibly practical to everyday life.
How does encryption works
Encryption keeps your data safe by converting it into a code that only a person with the right password or key can understand. When you encrypse a file or message, you scramble the information so that it appears as a fuck for someone else. Only those with the right key can turn it back to some readable, which protects your personal data, whether you are sending it or simply storing it.
Along with encryption -Hashing, hasing is a more important process that is often used in data protection. Instead of locking and unlocking the information, Hashing creates a unique fingerprint for your data. It takes your information and runs it through an algorithm, giving you a string of numbers and letters that represent the original. You cannot use the hash to recover the original data, but you can use it to verify whether something has changed. For example, if you download a file, you can compare its hash to the original to ensure that nothing has been tampered with.
In short, the encryption keeps your information private and allows you to unlock it with the right key later. Hashing helps to verify that your data has not changed. Both work quietly in the background, and you do not need to understand all the technical details for benefit from them.
Today, there are many tools available for encrypting, decrying, hasing and management of keys to help protect your data. Here are some of my top pics to easily encrypt my files, flash drives and emails.
Encrypt my archives with 7-zip quickly
I raised 7-zip Because it is free, reliable and usually on most Windows computers already on the computer. Encrying files with it was much easier than my expectation, and now I use it at any time, I want to keep files and documents private before storing or sending someone.
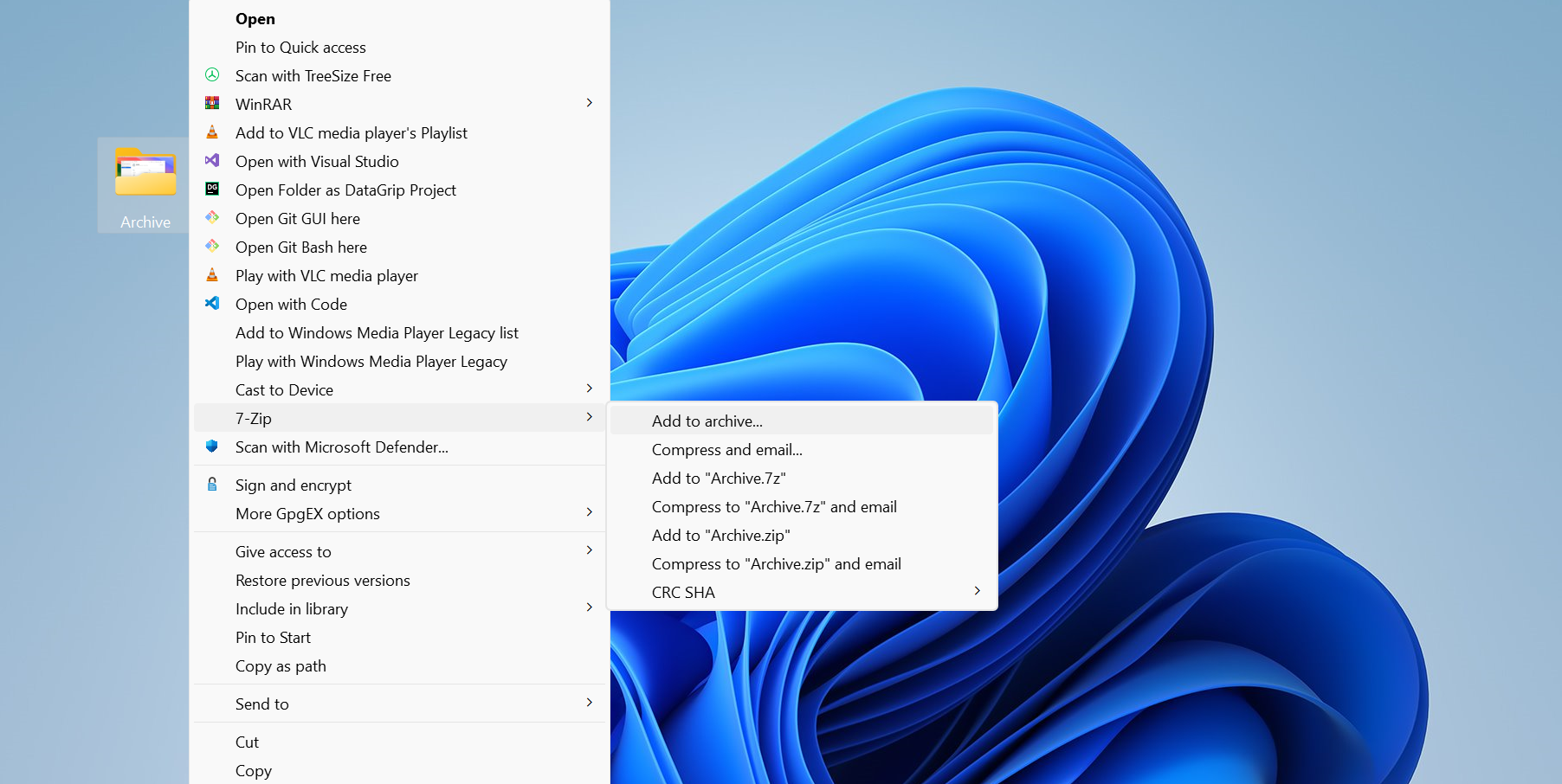
Here’s how I do it. I right-click on the file or folder I want to preserve, then choose 7-zip And pick Addition in collectionThe pop up that is in the window, I always switch the archive format from the zip to 7Z. The 7Z format provides strong security and enhanced encryption features compared to the 7Z format default zip format.
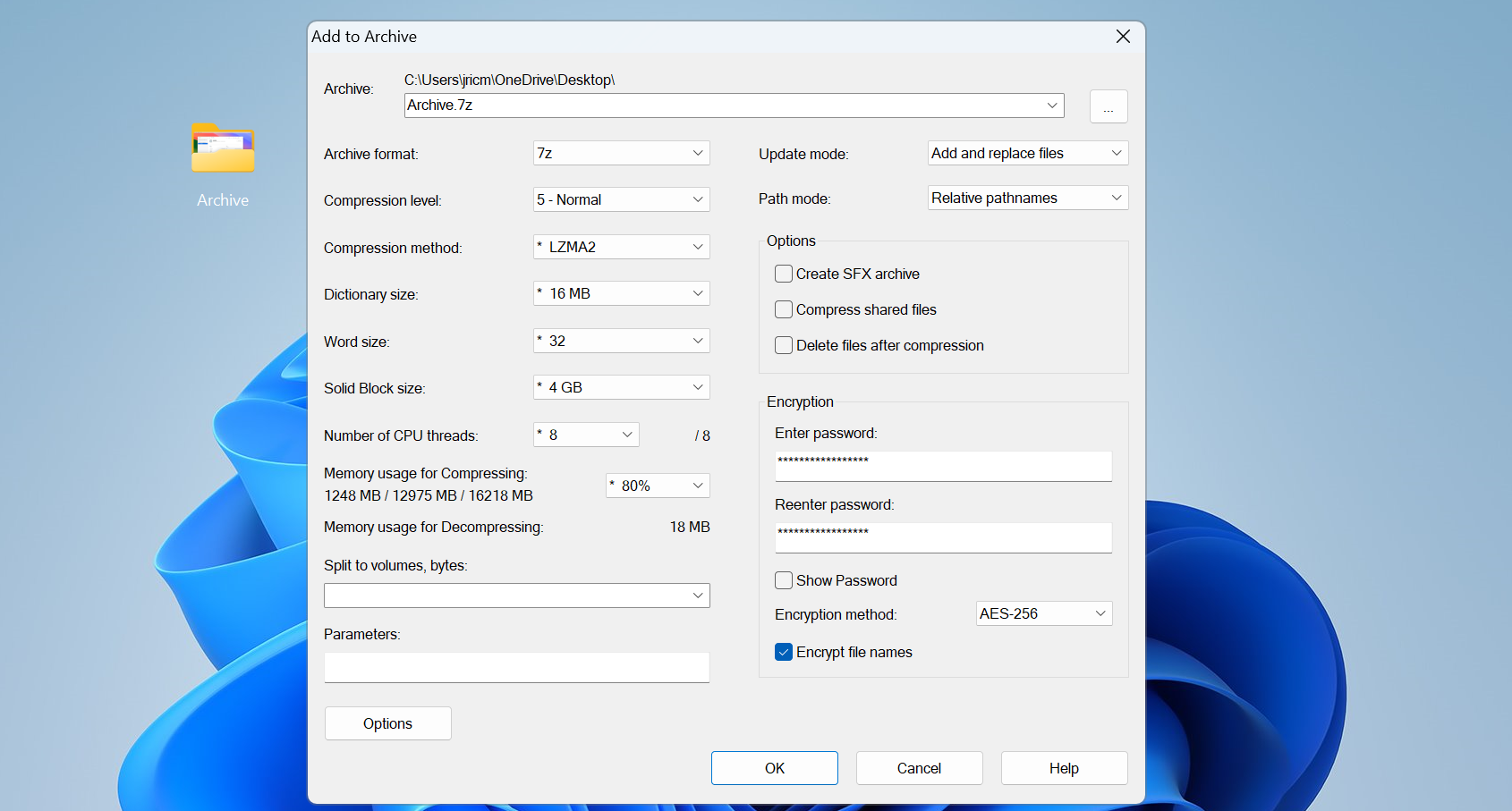
Next, I set a password. I make sure to use one that is at least 12 characters long, mixing the upper and lower letters, numbers and symbols. A strong password is important. Remember, no matter how good the encryption is, a weak password can ruin it.
I also check the box Encrypt file nameThis not only hides the content of your files, but also their names. If you leave it, no one can see what files are called, even if they cannot open them.
The encryption method is set on AES -256 by default, the same standard used by government agencies. I cling to it because it proves and does not slow down things.
After clicking on OK, the 7-Zip creates an encrypted collection in the same folder as my original files. It usually takes just a few seconds. I always test my encrypted archives by trying to open them, just to ensure that I remember the password and everything works.
To promote my safety, I never send an encrypted file and password through the same channel. If I store someone, I will share the password by phone or lesson. In this way, even though one intercepted email, they cannot go into files.
Once you hang it, encrypting with 7-zip becomes another nature. This is a simple way to keep your personal files really private.
Encrypt flash drive with Bitlocker
After learning how to encrypted my hard drive with Bitlocker, I realized that I also needed to encryp my flash drive, because I had lost too much in years. It is easy to do these small equipment incorrectly, and I did not want anyone to stumble through the files of my personnel. Bitalocker, which is made in windows, turned out to be the simplest way to keep everything safe on my drive.
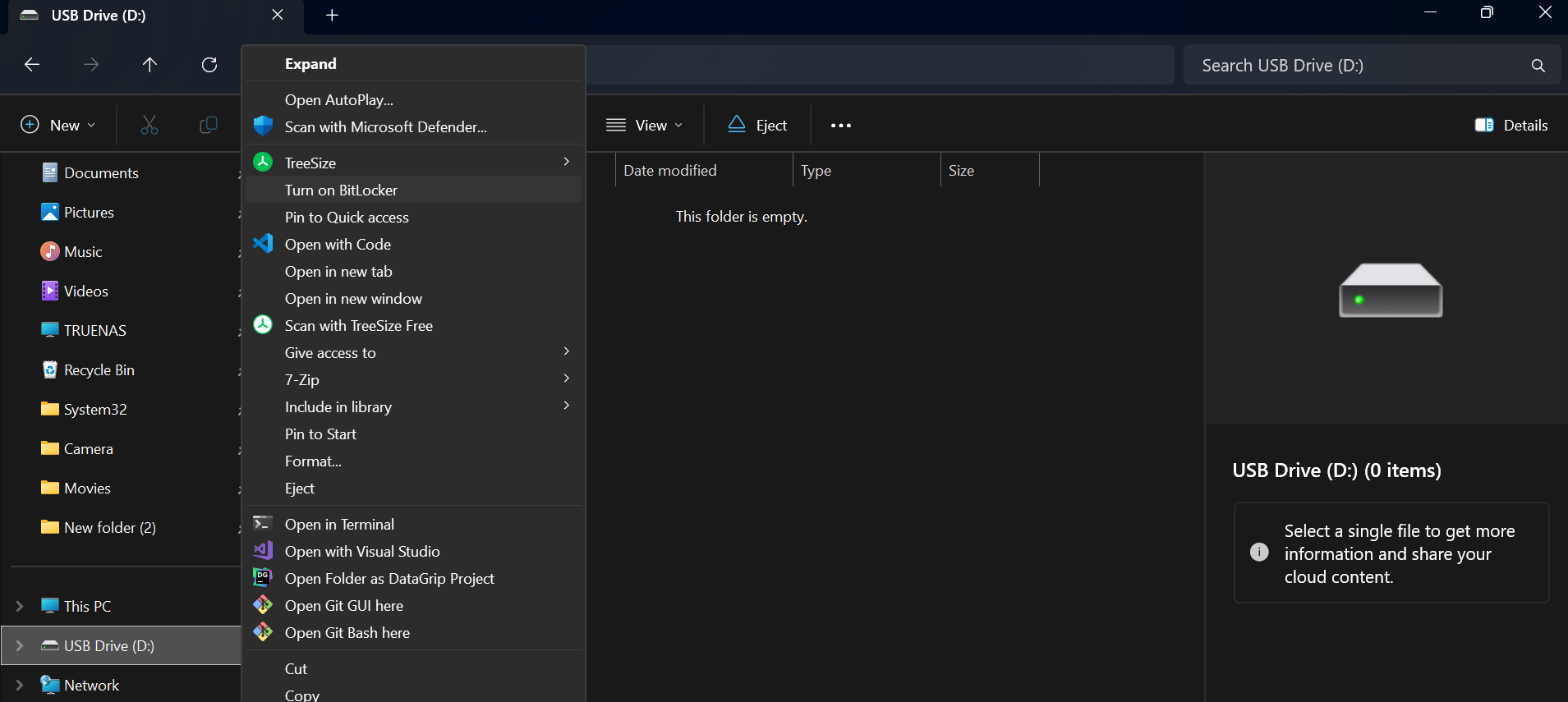
The installation of Bitalocker is very straightforward. I plugged into my flash drive and opened the file explorer. Then I right-click on the drive and turn on Bitalocker. On Windows 11, I have to click sometime Show more options To see this option.
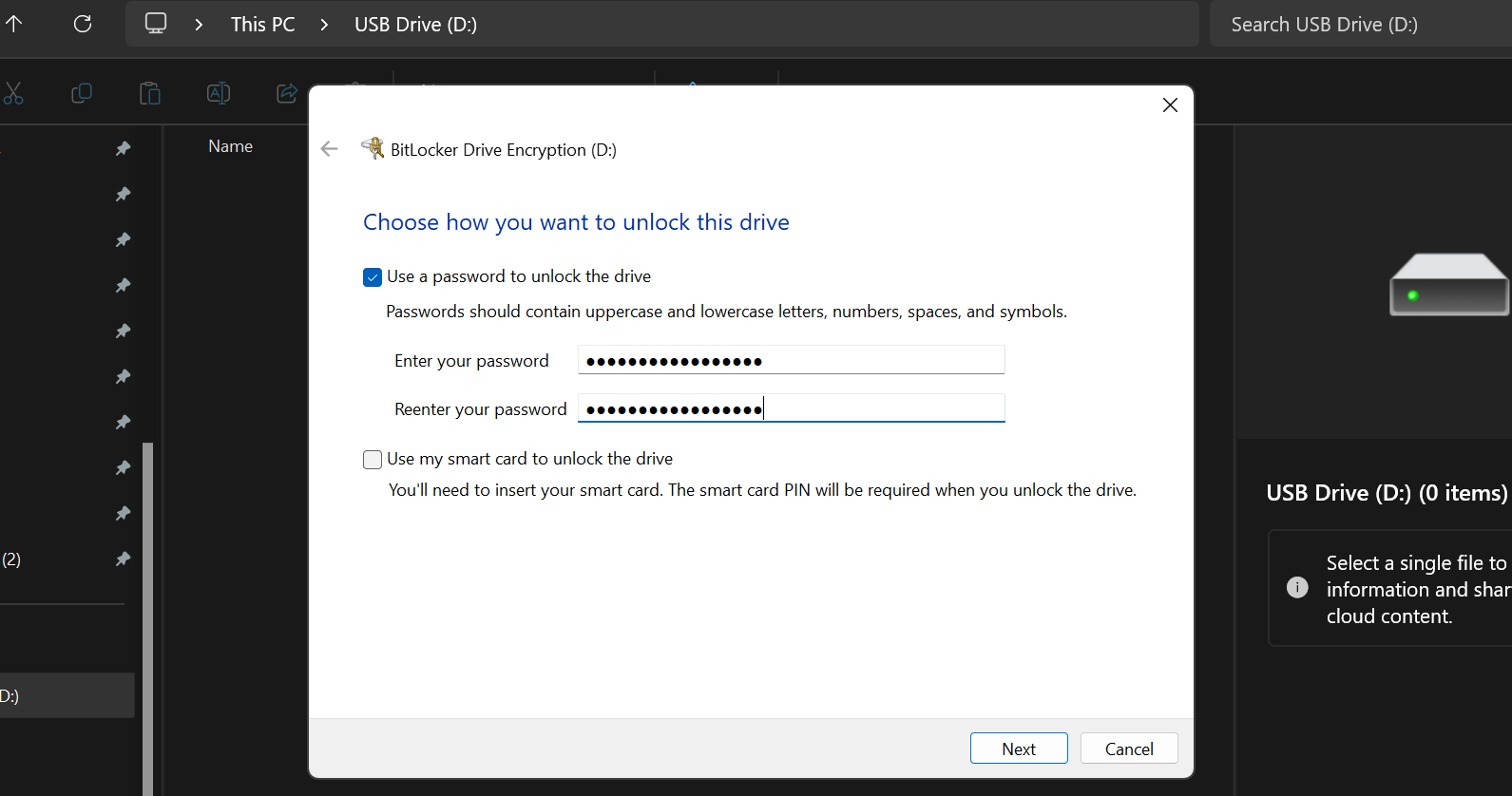
Bitlocker prepares a drive for encryption, which usually takes just one or two minutes. After that, it tells me to set a password. I always use a strong, unique password that is different from the people used for my accounts. Since I would need to type this password every time I unlock the drive, I am sure this is something that I can remember but still difficult to guess.
Next, Bitalocker asks where I want to save my recovery key. This key is important. If I ever forget my password, the recovery key is the only way to recover my files. I save it to a safe place, such as my cloud storage or a printed copy stored at home.
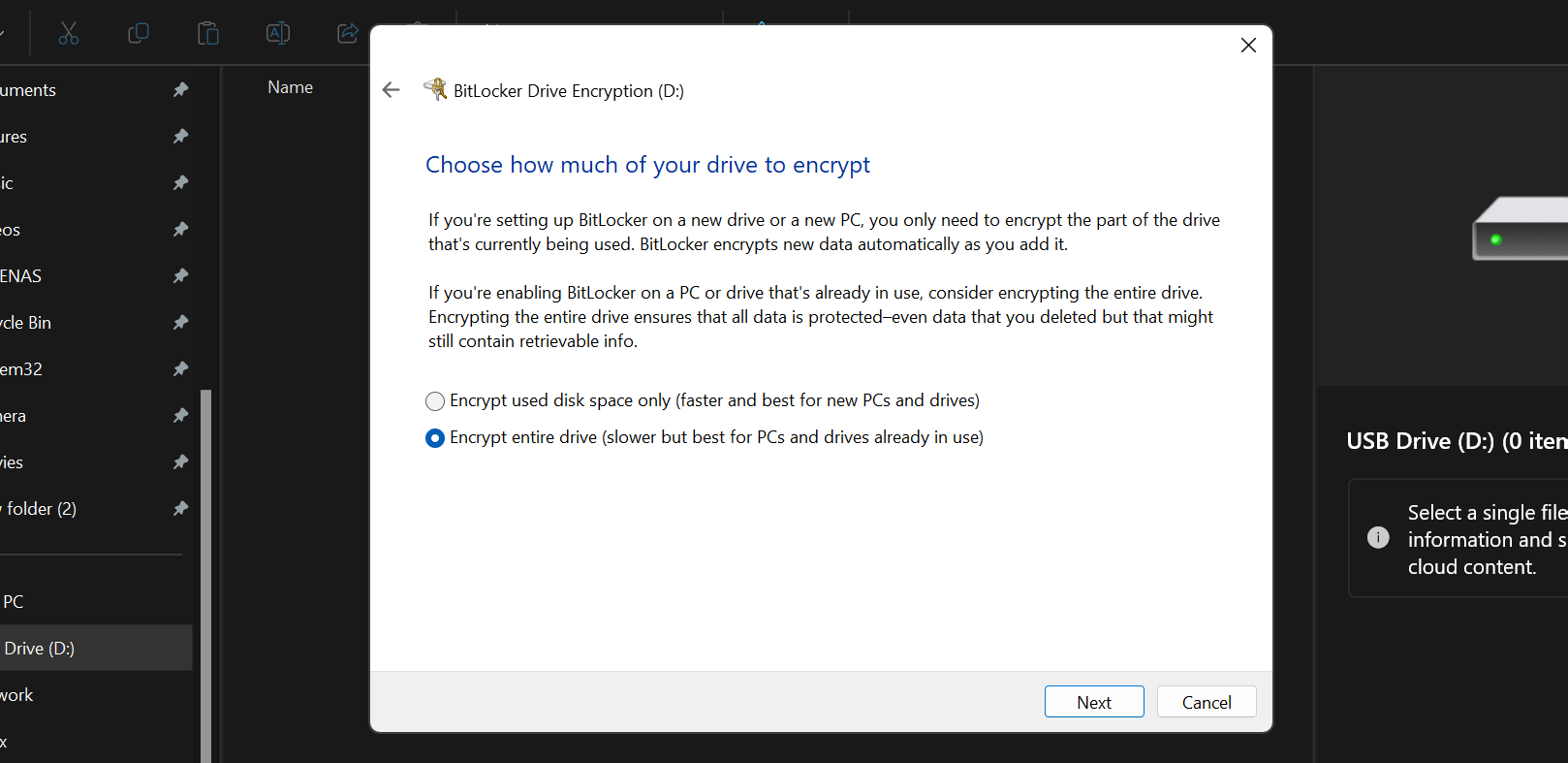
Bitalocker then lets me take how much part of the drive has to be encrypted. For a new drive, I only choose to encrypt the used space, as it is sharp. If the drive already has files, I choose to encrypted the entire drive to ensure that nothing is unsafe.
There is also an option for encryption compatibility. I always choose compatible mode, so drive works on any Windows computer, not only the latest people. If I need to use a drive on an old machine, it protects me from headache.
Once I confirm everything, Bitalocker starts to encryp. For large drives, it may take some time, but I can use my computer during the process. When this happens, I will see a lock icon on the drive in the file explorer, showing that it is preserved.
After the setup, it is easy to use an encrypted drive. When I plug it to Windows Computer, Bitalocker asks for my password. I can also set it to unlock it automatically on my main PC, but I am careful because it reduces safety.
Easily use is probably one of the biggest reasons I use Bitalocker. It is so easy that I really have no reason that I do not encrypt my personal flash drive. Now, even though I lose a drive, I know that my files are preserved and my personal data cannot be easily accessed outside my Windows machine.
How do I encryp my email with PGP
When I want my messages to be completely private, even from email providers, I use PGP encryption KleopatraThere are other ways to send PGP-encrypted email to Linux, but since I am using Windows, I choose Cleptra. There is a little more effort to install it, but once you hang it, the process is straight and gives you the right end-to-end secrecy.
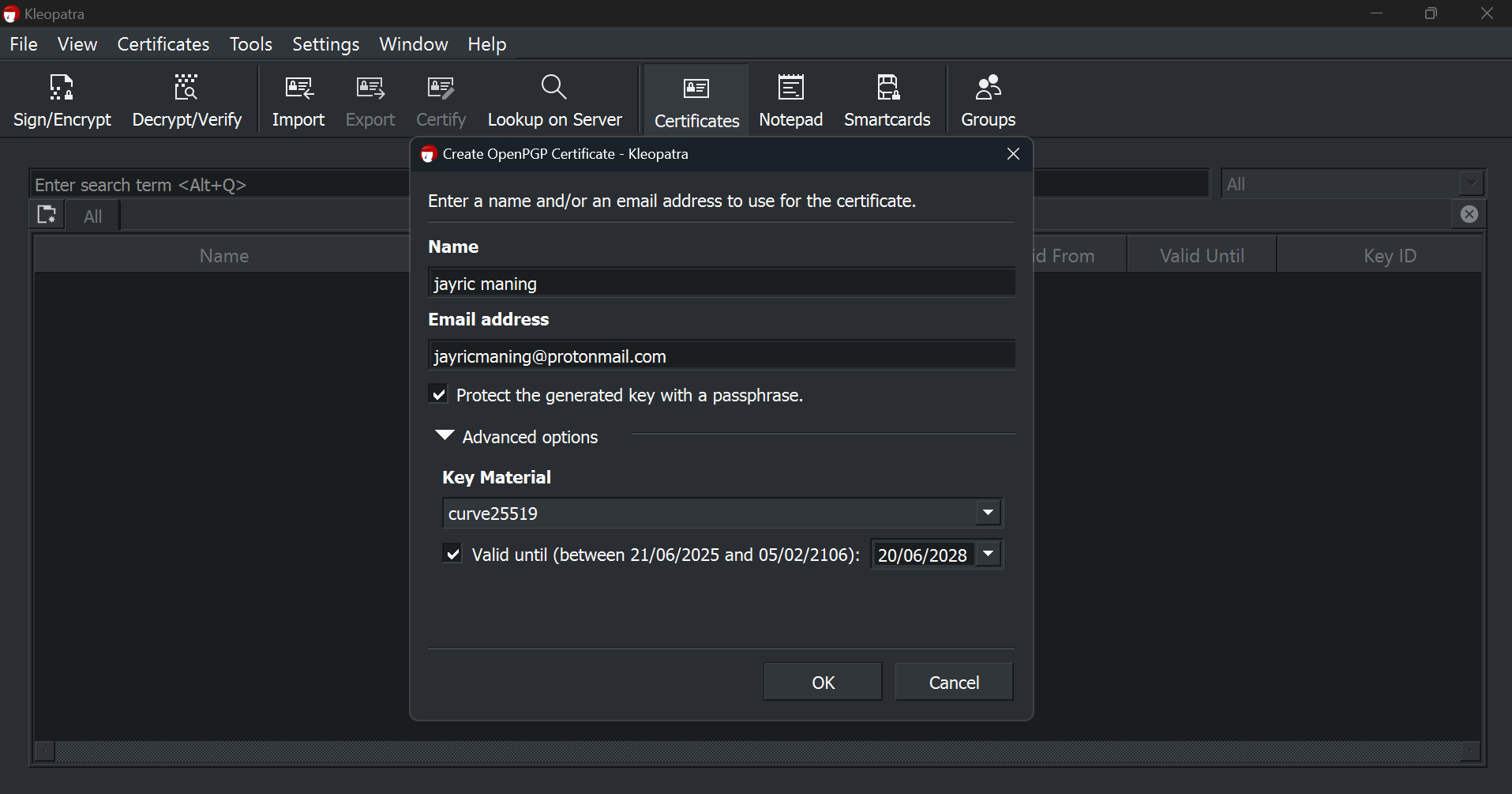
First, I download and install the GPG4WIN package, including Cleopra. After opening the ClaoParata, I make my own key pair by entering my name, email and a strong passfrass. Claoapatra generates two keys for me: a public key that I can share to anyone who wants to send me an encrypted message, and a private key that I keep on my computer.
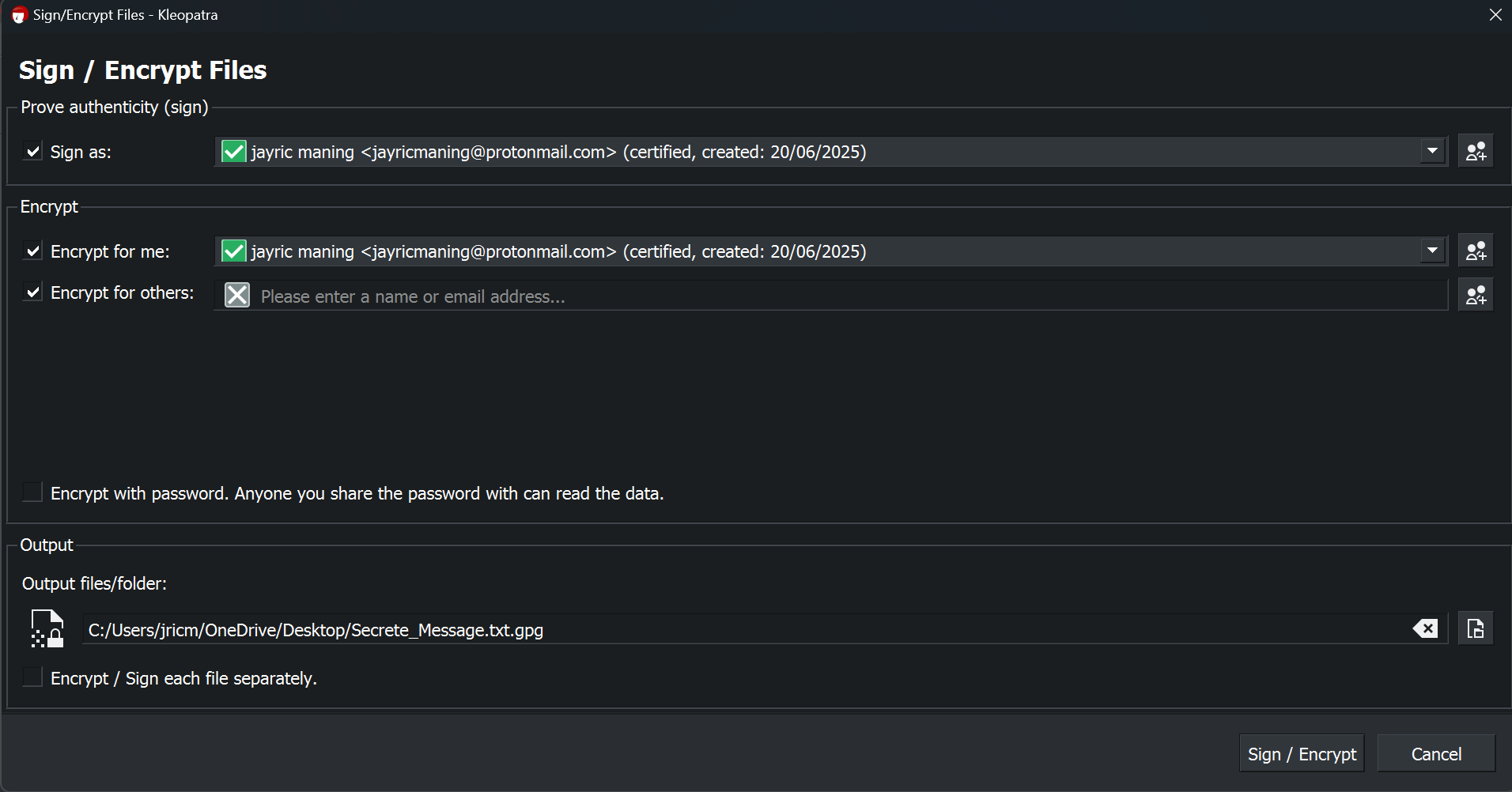
When I want to send an encrypted message, I usually write it in the notepad. Then, in ClaoPara, I click Sign/encrypt Select the text file with the button and my message. I check the box Encrypt with password And enter a password that I will share with my recipient. After clicking on the encrypt, Claopra creates a new PGP-encrypted file.
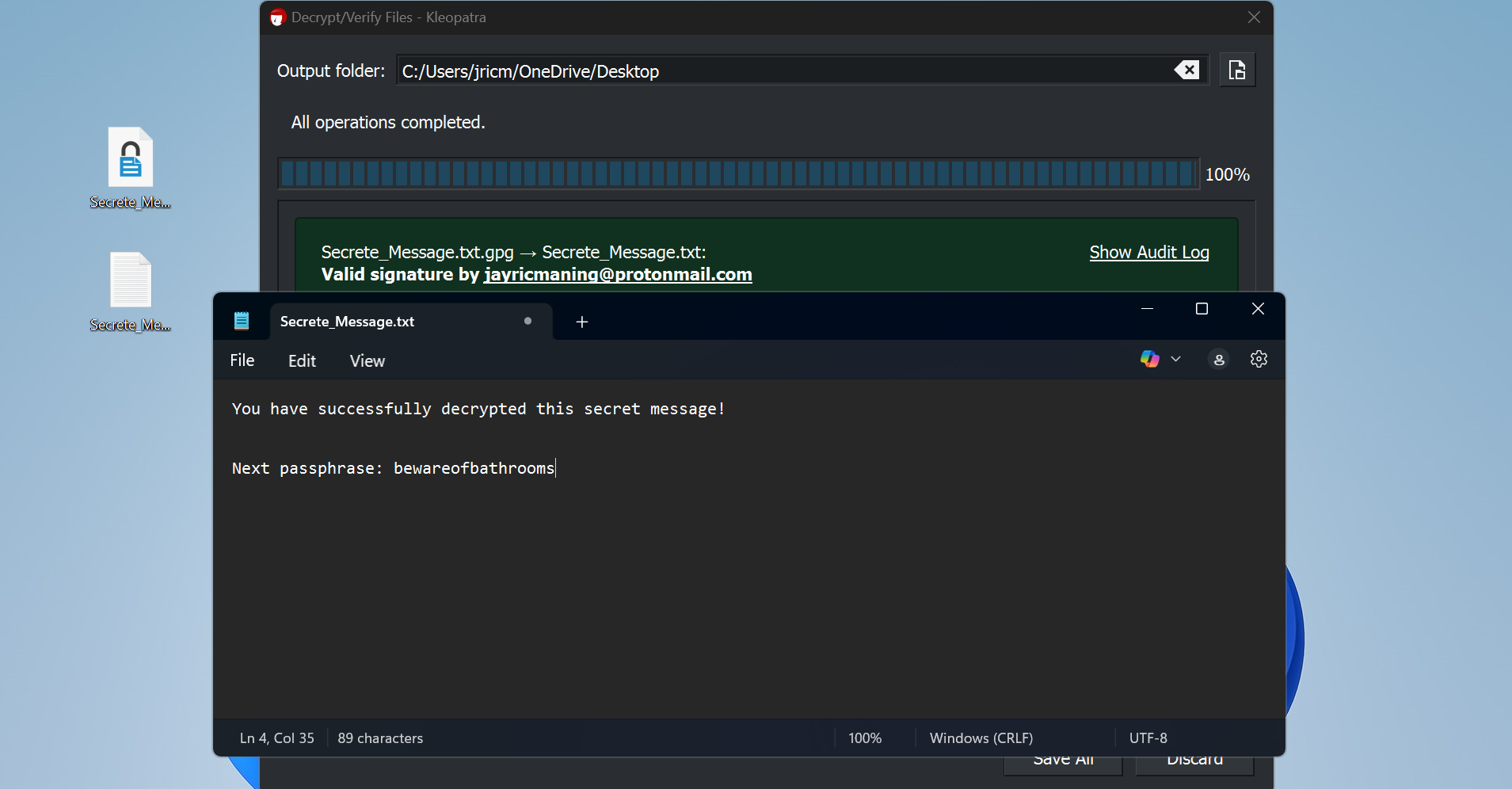
I can send this encrypted file via email. To open it, the recipient simply requires cleopra and password set by me. They right-click the PGP file, choose open with Clepatra, and enter the password. Cleopra then decipses the file and shows the original message.
Both people need to have a clopra or a uniform PGP tool, and they have to know the password or passfreese. To safely share the passfrass, I can inform my recipient through meatup or a safe call (using a signal or WhatsApp), and then attach a new passfrass to each PGP file sent by me.
In addition to simple messages, PGP can also be used to encrypted all types of files such as PDF, audio recording, video and software. Therefore, things like legal papers, financial records, or your next million-dollar ideas are definitely worth encrypting with PGP when sending them via email.
Once I started using these devices in my daily routine, I realized how easy it is to protect my personal files and messages. Whether I am shutting down my archives, protecting flash drives, or sending sensitive emails, encryption now looks like just another simple step to protect my digital life. If you are hesitant to try it, I can say that it is worth a few minutes to learn. Your future will thank yourself for making privacy a habit.