
The Bumblebee Malware SEO Poisoning Campaign has been exposed earlier this week, using Rvtools, which is using more typoscatting domains, mimicking other popular open -rs projects to infect the equipment used by IT employees.
Bleepingcomputer, Zenmap’s notorious, NMAP network scanning tools, and were able to find two cases for Winmtr Tracerout utility.
Both these devices are usually used by IT employees to diagnose or analyze network traffic, some characteristics require administrative privileges, to do the work users of these tools create users of prime goals for the corporate networks to dissolve the corporate network and later spread in other devices.
The bumbled malware loader is pushed through at least two domains – zenmap (.) Pro and Winmtr (.) Org. While later currently offline, the former is still online and shows a fake blog page about Zenmap when visited directly.
When users are redirected from zenmap (.) Pro from search results, however, it shows a clone of a valid website for NMAP (Network Mapper) utility:
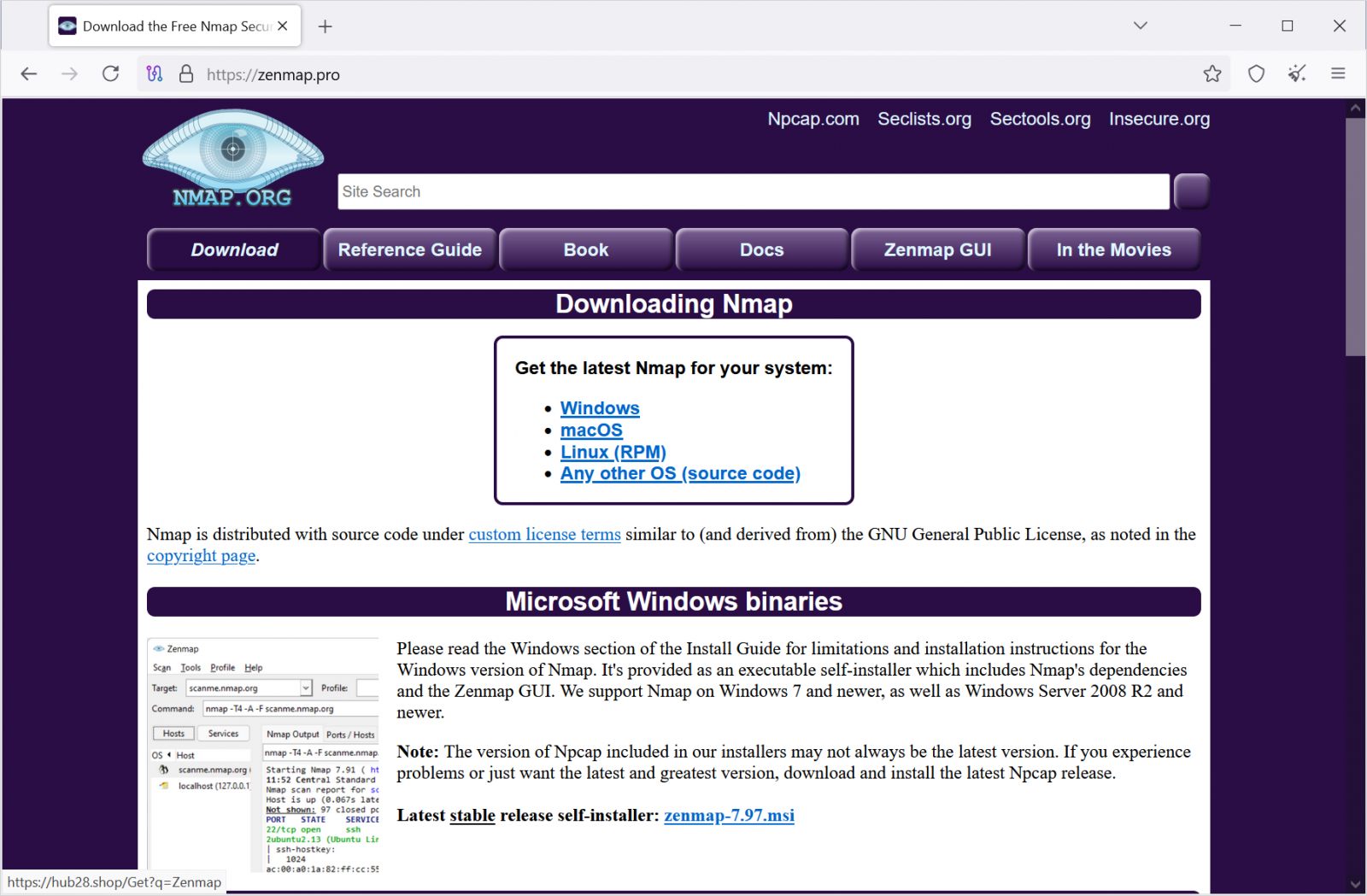
Source: Bleepingcomputer
Two sites obtained traffic through SEO poisoning and Bing Search Results for high rank and related words in Google.
.jpg)
Source: Bleepingcomputer
BleepingColputer’s tests suggest that if you go directly to the fake zenmap site, it shows many AI-related articles, as seen in the image below:
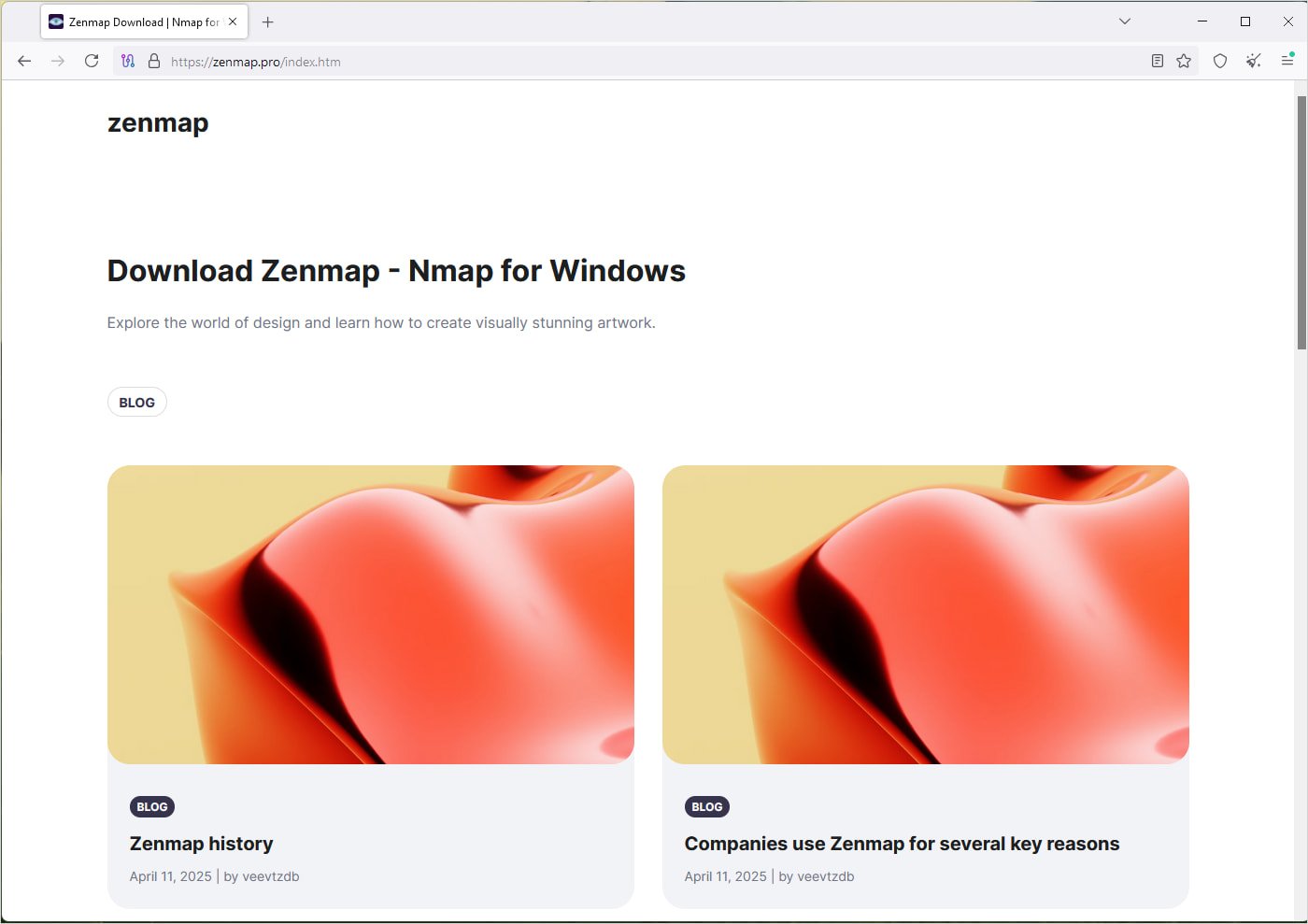
Source: Bleepingcomputer
The payload download section was distributed through ‘zenmap-7.97.msi’ and ‘Winmtr.msi’, and they avoid detection of most antivirus engines on both virustotals (1, 2,
Installers distribute a promised application with a malicious DLL, as in the case of Rvtools, which falls a fall Bumbled loader On users’ equipment.
From there, the back door can be used to profile the victim and introduce additional payloads, which may include infostellers, ransomware and other types of malware.
In addition to the open-source tools described above, BlappingComper has also seen the same campaign that targets users in search of Hanva Safety Camera Management Software WisnetViewer.
Size Which Vreden also saw A trojan of video management software milestone xprotect is part of the same campaign, the malicious installer is being given ‘Mestonis (.) Org’ (online).
Official rvtools still offline
Both official rvtools domain – Robware.net and rvtools.com – are currently showing a warning to users not to download software from informal sites, but do not provide the download link themselves.
Following the allegations that the official RVTOOLS site pushed a malware-tested installer, Dell Technologies denied the allegation, saying that its sites had not distributed a trojan version of the product.
Dell said the official RVTOOLS sites were taken offline as they were the goals of the distributed refusal-service-service attacks.
An explanation for the attacks would be that the actor with danger behind Bumblebee decided to take the official download portals down to drive malicious sites searching for alternative sources for equipment.
To reduce the risk of installing tragged versions of valid software, the best recommendation is to ensure that it is to be obtained from official sources and package managers.
It is also worth checking the downloaded Installer hash With a known, clean version before running it.



