
Chlorox is sueing it in giant cognizance for gross negligence, alleging that it enabs the August 2023 cyber attack to reset an employee’s password for a hacker without verifying his identity first.
The incident was first made public in September 2023, allegedly performed by hackers associated with scattered spider who used a social engineering attack to dissolve the company.
The lawsuit states that Cognizant provided IT services to Chlorox, including service desk support and identity management, which was the point of compromise, which led to a disastrous and expensive cyber attack for the company.
Chlorox is a major consumer commodity company known for domestic cleaning products, bleach, disinfectant and personal care items. Cognizant is a global IT services and counseling company, providing cloud services, software development and cyber security.
According to the complaint, from 2013 to 2023, Cognizant was contracted by Chlorox to handle its IT operation.
“Cognizant provides service desk (” service desk “), which can contact chlorox employees when they require password recovery or reset assistance,” reads the complaint shared with BlappingCopper.
“The operation of the service desk of the cognizant came up with a simple, general knowledge requirement: Never reset someone’s credentials without certifying them properly. Chlorox made it easier for the cognizant that whenever a credential recovery or reset assistance is provided to them, provide them direct procedures.”
However, the complaint alleged that on August 11, 2023, recording suggests that a cyber criminal nomine the service desk of cognizant several times, pretending to be a chlorox representative that requests password and multi-factor authentication reset.
“At any point during any call, the agent verified that the collar was actually the employee was 1. At any point the agent did not follow the credential support procedures of the chlorox-or if before the 201023 procedure or January 2023 update-cyber criminal changing the password, to send them several times for any identity. Do
This type of social engineering attack has become the hallmark of scattered spider attacks, recently used in UK retail attacks on Marx and Spencer and Co-op.
After failing to verify the actual identity of the collar, the cognizant resumes credentials and multi-factor authentication (MFA) for the cognizant hacker, giving them access to the IT network of Chlorox.
To make cases worse, Chlorox alleged that danger actors have used the same playbook to reset the password and MFA for another employee, which worked in IT security, which was once again done without verification. This allegedly provided access to the network to the attackers, which they spread to further equipment.
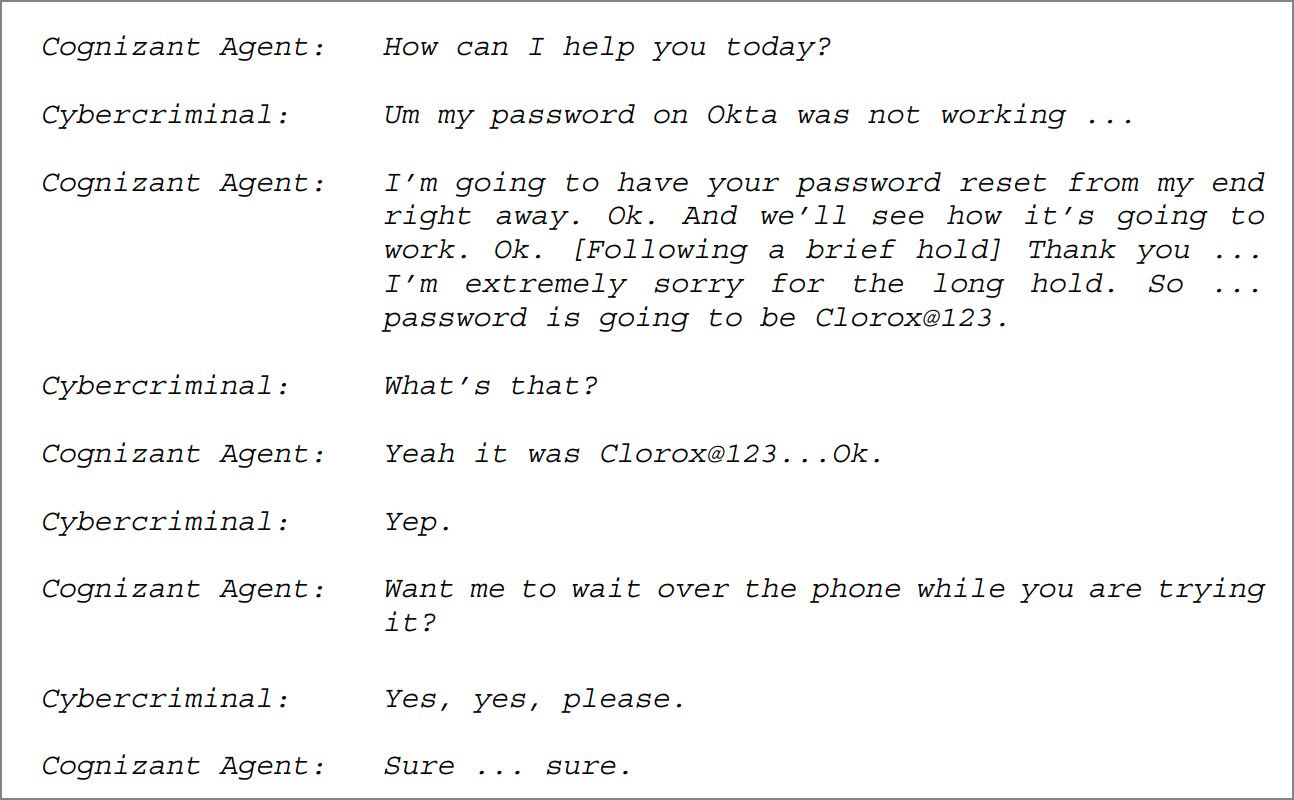
Source: Chlorox Complaint against Congizant
The chlorox states that the works of the cognizant crippled their corporate networks, stopped manufacturing, and caused extensive product lack and business obstruction.
In addition, chlorox described the cognizant’s response and recovery support as highly disable, resulting in delay in application of container measures, failure to close the compromised accounts, and sending undercurfeized personnel on the premises.
“As a result, cyber attack was weakening. It crippled Chlorox’s corporate network and crippled business operations,” Describes the legal complaint,
“And to make cases worse, when Chlorox called Cagnizant to provide reactions to the event and disaster recovery assistance services, Cognizant provoked its response and reduced the damage that had already been done.”
Clorox’s complaint is a violation of contract due to misunderstanding of the training of employees on cognitive failure, good faith and violation of fair behavior, gross negligence, and the credential reset processes of clients on the credible reset processes of the client.
For these functions, the resulting commercial disruption caused the lost sales, with hundreds of million dollars as well as long-term results, chlorox is demanding $ 49 million in direct therapeutic damage and $ 380,000,000 in total damage.
(Updated 7/24 03:00 AM EST) – A cognitive spokesperson sent the comment below to Blapping computer:
“It is shocking that a corporation of chlorox had such an unworthy internal cyber security system to reduce this attack. Chlorox has tried to blame us for these failures, but the reality is that Chlorox has hired cognitive for a narrow scope of help desk services, which was extended to the cognitive manner for which Chloraux was unconcerned. Did not manage cybersity. ” – cognitive
CISOS knows how to purchase a board begins with a clear, strategic approach how the cloud safety runs the business price.
This helps to introduce the risk, impact and priorities to the free, editable board report deck deck security leaders in clear business terms. Convert security updates into meaningful conversations and take fast decision in boardroom.



