
ICLUD calendar invitations are being abused for sending a hired Callback Fishing email as direct purchases from Apple’s email server, making them more likely to bypass spam filters to enter the inbox of goals.
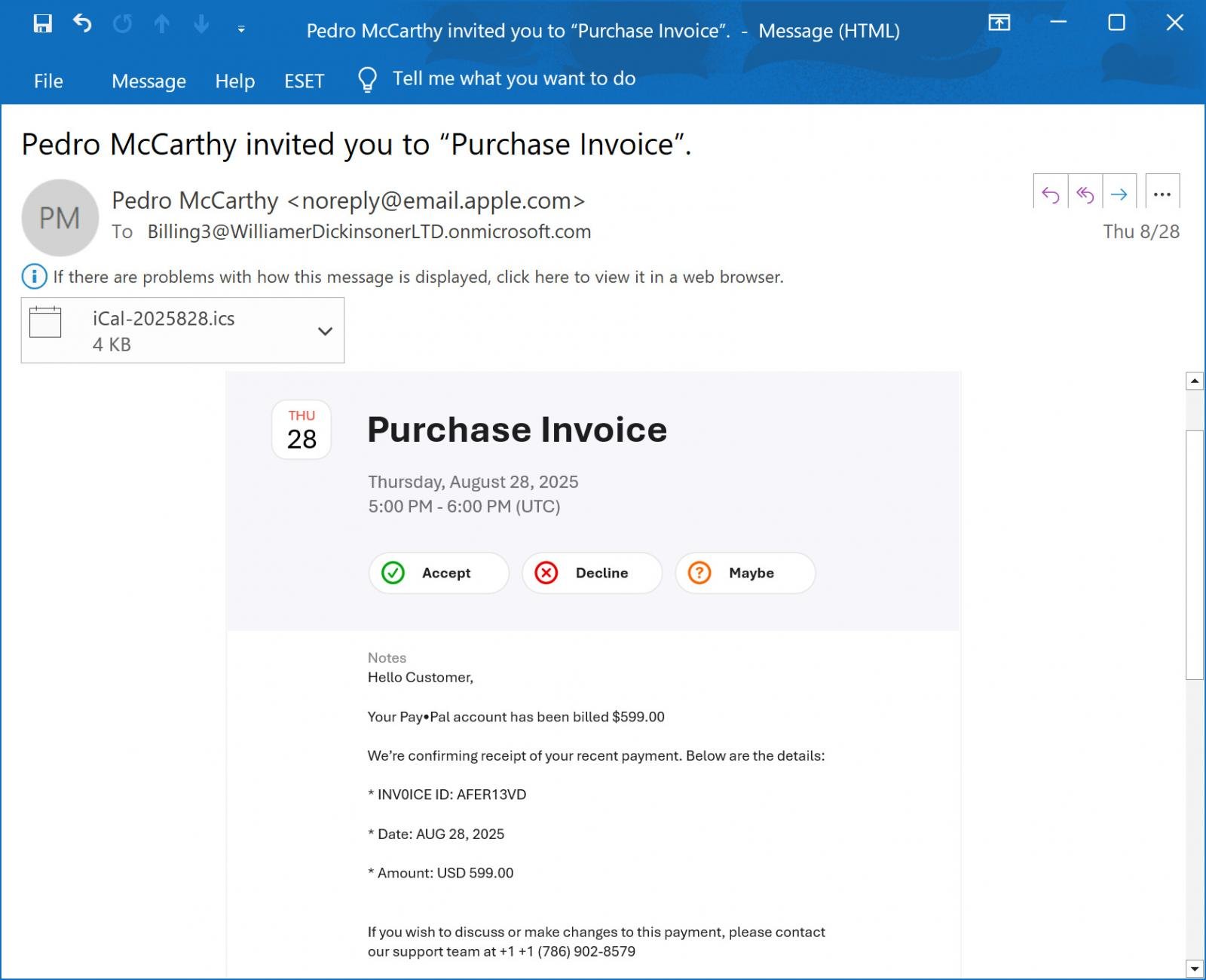
Earlier this month, a reader shared an email with Bleepingcomputer, claiming the payment receipt for $ 599 against the recipient’s PayPal account. This email included a phone number if the recipient wanted to discuss the payment or change it.
“Hello customer, your PayPal account has been given a $ 599.00 bill. We are confirming your recent payment,” read the email.
“If you want to discuss or change this payment, please contact our aid team at +1 +1 (786) 902-8579. Contact us to cancel the +1 (786) 902-8579,” Email continued.
Source: Bleepingcomputer
The goal of these emails is to think that their Papail account was fraudulently charged to purchase and the email recipient was accused of intimidating the scammer’s “support” phone number.
While calling the number, a scammer will try to scare you thinking that your account was hacked or they need to connect to your computer to start the refund, you have been asked to download and run the software.
However, in such previous scams, this remote access was used to steal money from bank accounts, deploy malware or steal data from computer.
ICLUD invites to send email misuse of calendar
The greed in this email is a specific callback phishing scam, but it was strange that it was sent from noreply@email.apple.com, SPF, DMARC and DKIM Email passing the safety tests, showing that it came legally from Apple’s mail server.
Authentication-Results: spf=pass (sender IP is 17.23.6.69)
smtp.mailfrom=email.apple.com; dkim=pass (signature was verified)
header.d=email.apple.com;dmarc=pass action=none header.from=email.apple.com;
As you can see from the above fishing email, this email is actually an iCloud calendar invited, where the danger actor included the fishing text within the notes field and then invited a Microsoft 365 email address that he controlled.
When the iCloud calendar event is created and outsiders are invited, an email invitation is sent from the Server of Apple in the name of the owner of the iCloud Calendar with the email address.
In the email viewed by Bleepingcomputer, the invitation has been addressed to Microsoft 365 accounts, “billing3@williamerdickinsonerltd.onmicrosoft.com”.
Similar to the previous fishing campaign, which used the “new address” of Payal, it is believed that the Microsoft 365 email address that is sent is actually a mailing list that automatically receives any other group members.
In this case, the members of the mailing list are the goals of the fishing scam.
As the email initially started from the email server of Apple, if it is forwarded by Microsoft 365, it usually fails in the SPF email check.
To prevent this, the Microsoft 365 uses the sender rewriting plan (SRS) to re -write the return path on the address associated with Microsoft, allowing it to pass the SPF check.
Original Return-Path: noreply@email.apple.com
Rewritten Return-Path: bounces+SRS=8a6ka=3I@williamerdickinsonerltd.onmicrosoft.com
While nothing is particularly special about the fishing lur, the legitimate iCloud calendar inviting feature, the email server of the Apple, and the misuse of an apple email address adds a sense of legitimacy to the email and also allows potentially to bypass the spam filter as it comes from a reliable source.
As a general rule, if you receive an unexpected calendar inviting with a strange message within it, it should be treated with caution.
Bleepingcomputer contacted Apple about the scam, but our email did not receive a response.



