
Large network scans are targeting Cisco ASA devices, warning cyber security researchers that it may indicate an upcoming defect in products.
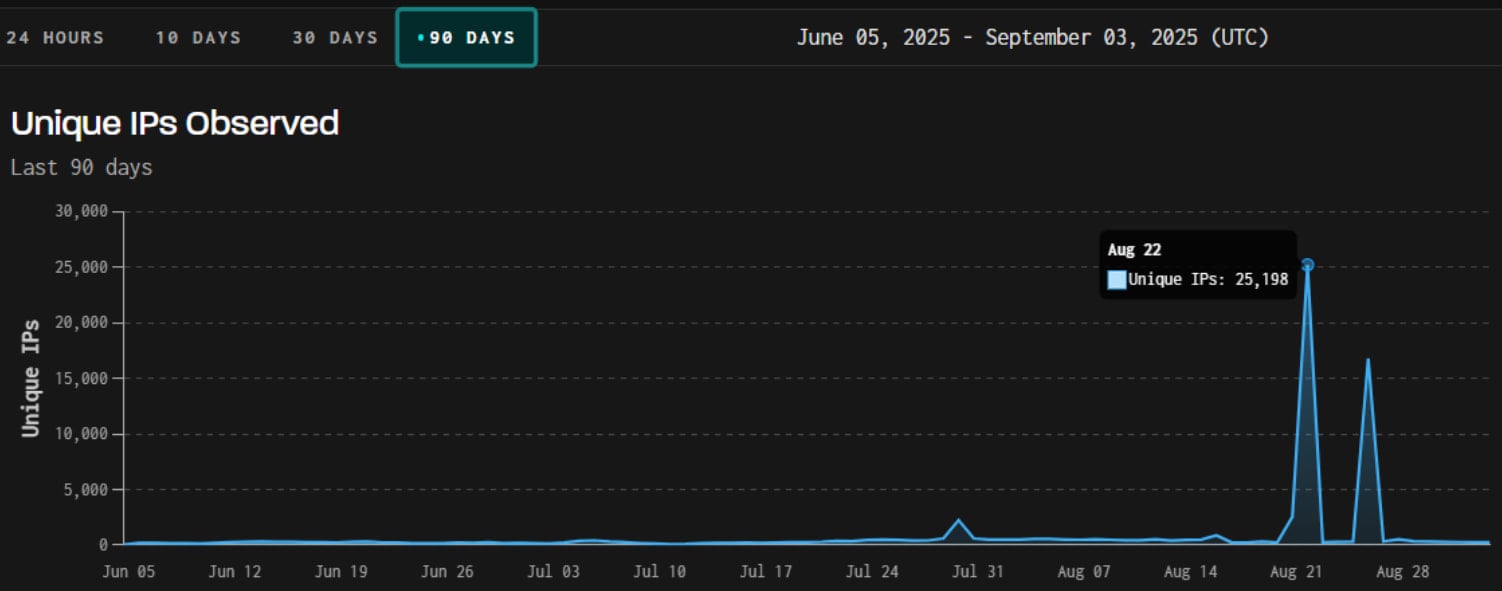
GRIYNOISE has recorded two Important scanning spikes In late August, ASA login portals and Cisco iOS Telnet/SSH with more than 25,000 unique IP addresses.
The second wave, login on August 26, 2025, largely (80%) was powered by a Brazilian botnet, using around 17,000 IP.
In both cases, the danger actors used to overlap user agents such as Chrome, suggesting a common origin.
Scanning activity mainly targeted the United States, while the UK and Germany were also targeted.
GRIYNOISE has previously explained that such reconnaissance activity occurs in 80% of cases before the disclosure of new weaknesses on scanned products.
Statistically, this correlation was weak compared to other vendors for Cisco, but information about such spikes may still be helpful to defenders in their monitoring and active measures.
These scans usually fail in the efforts to exploit the bugs already identified, but they may also be attempted to exploit new flaws and efforts to mapping.
A separate report published earlier by System Administrator ‘Nadsec – Rat5ak’ Activity starting on 31 July with a low opportunistic scan with overlapping activity which rose in mid -August and ended on August 28.
Rat5ak watched 200,000 hits at Cisco ASA Endpoints within 20 hours, with a similar 10K/IP traffic that appeared highly automatic.
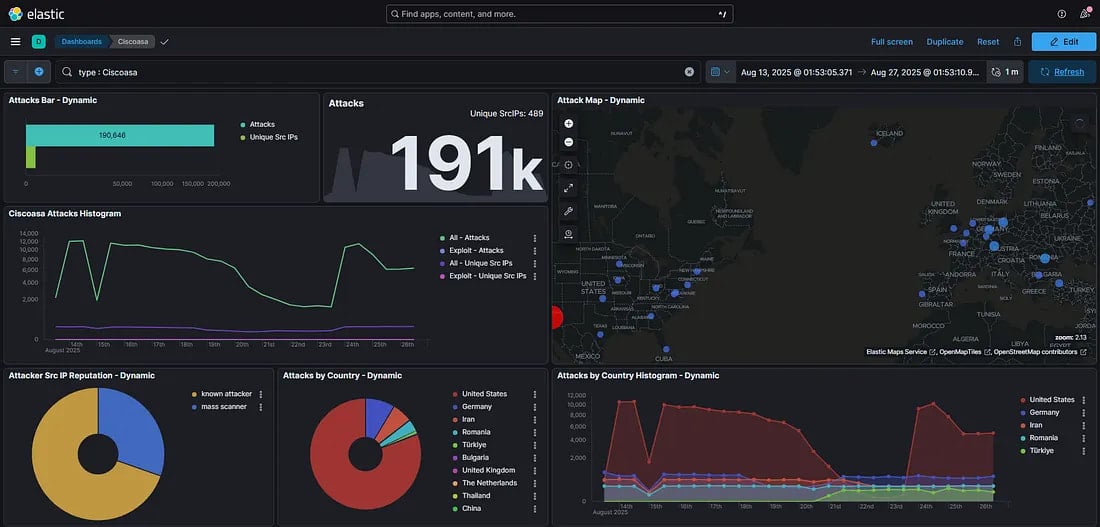
The administrator reports that the activity has come from three ASNs, namely NYBula, cheap-host and global connectivity solutions LLP.
System administrators are advised to implement the latest security updates on Cisco ASA, which to patch clarifications, apply multi-factor authentication (MFA) for all remote ASA logins, and avoid exposes /++cscoe+/logon.html, Webvpn, TELNET, or SH.
If external access is required, a VPN concentrator, reverse proxy or access gateway must be used to apply additional access control.
Finally, use scanning activity indicators shared in GRYNOISE and Rat5ak reports to block these efforts in advance, or to limit the geo-blocking and rates to the areas away from your organization.
Bleepingcomputer has approached Cisco for a comment on the activity seen, and we will update this post when we listen to them.



