Six major password managers with ten million users are currently unsafe for unexpected clicking flaws that may allow the attackers to steal account credentials, 2FA code and credit card details.
When the victims are unsafe for cross-site scripting (XSS) or cash poisoning on a malicious page or websites, actor of danger can take advantage of safety issues, where attackers overlay the invisible HTML elements on the password manager interface.
While users believe that they are interacting with harmless clickable elements, they trigger sensitive information leaking autofil actions.
Flaws were presented by independent researcher recently during the Def Con 33 Hacker Conference Marke tothLater researchers from cyber security company socket Verified the findings And helped inform the affected vendors and coordinate public disclosure.
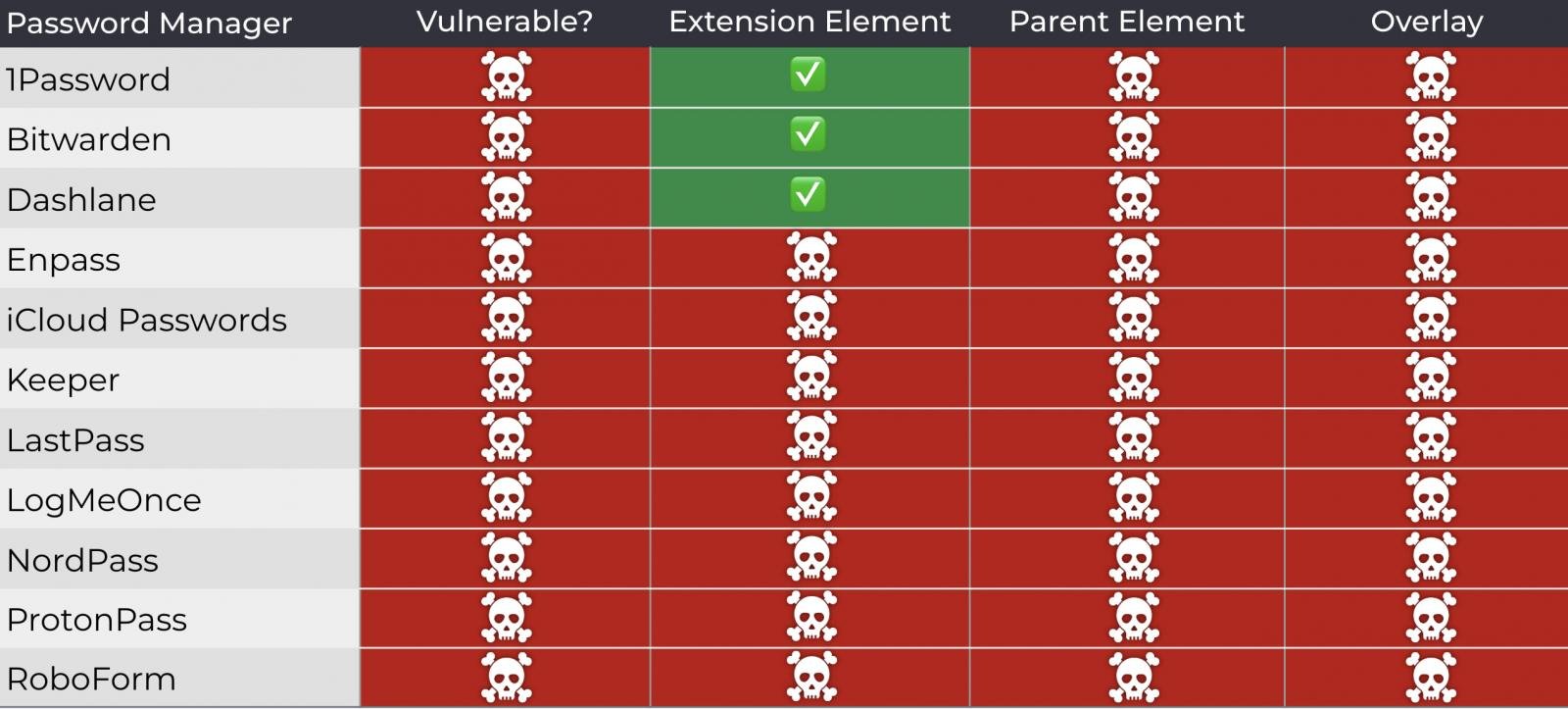
The researcher tested his attack on 1Password, Bitwarden, EnPASS, ICLUD password, lastpas and some versions of Logmeonce, and found that all their browser-based variants could leak sensitive information under some landscapes.
Methods of exploitation
The main attack mechanic is to run a script on a malicious or compromise website that uses opacity settings, overlay or pointer-event tricks to hide the autofil dropdown menu of a browser-based password manager.
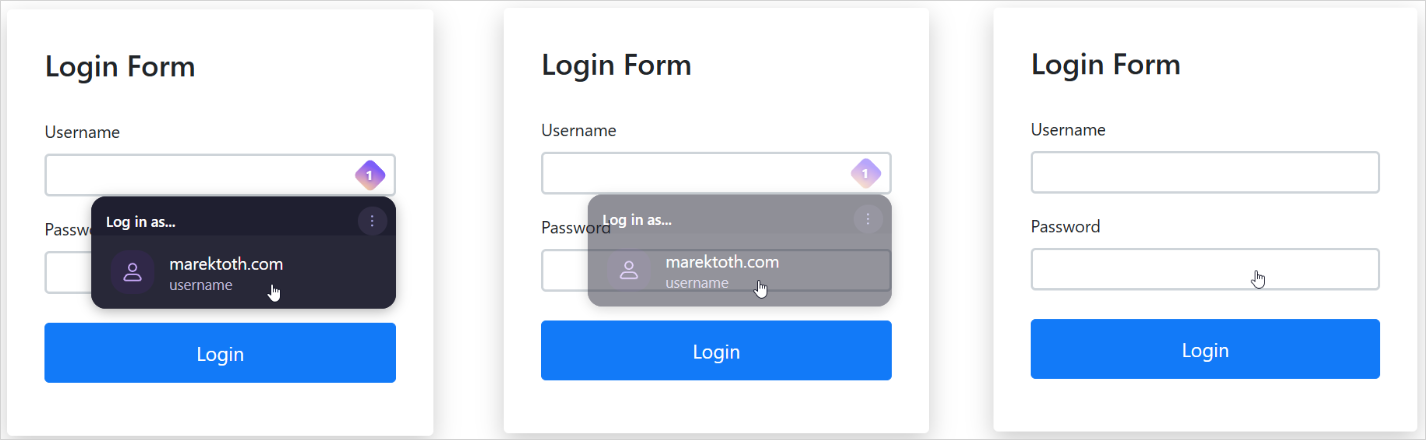
Source: Mark Tath
The attacker then overlays fake intruders (such as cookie banners, popups, or captcha), so that the user clicks come to the hidden password manager controls, resulting in the formation of the form with sensitive information.
Tóth demonstrated several DOM-based sub-factories, which forms the exploitation variants of the same defect, including direct DOM element optricity manipulation, root element optimity manipulation, original element opthetic manipulation and partial or complete overlaying.
The researcher also demonstrated the possibility of using a method where UI follows the mouse cursor, so any user clicks, no matter wherever it is posted, the data triggers autofils.
Source: Mark Tath
Toth says that a universal attack script can be used to identify the active password manager on the target browser and then adapt the attack in real time.
Vendor effects and reactions
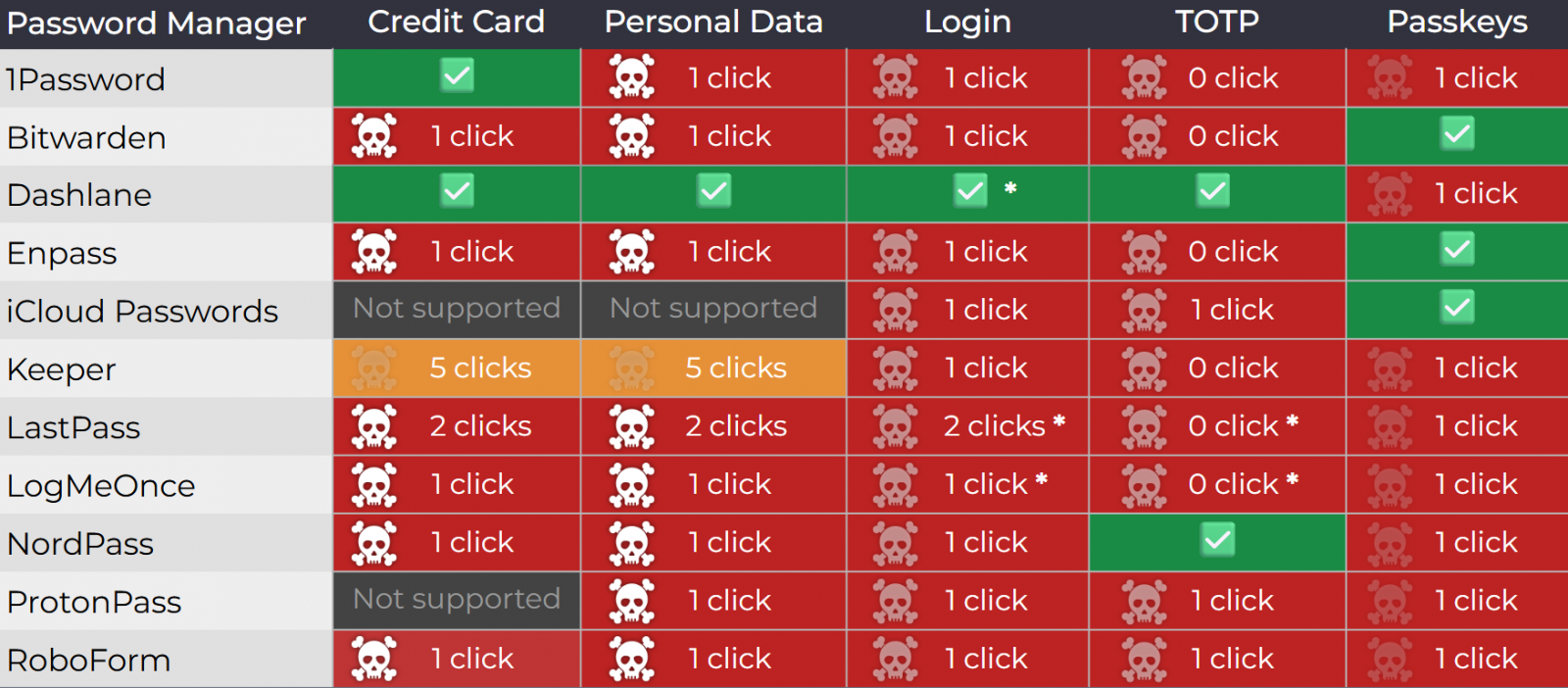
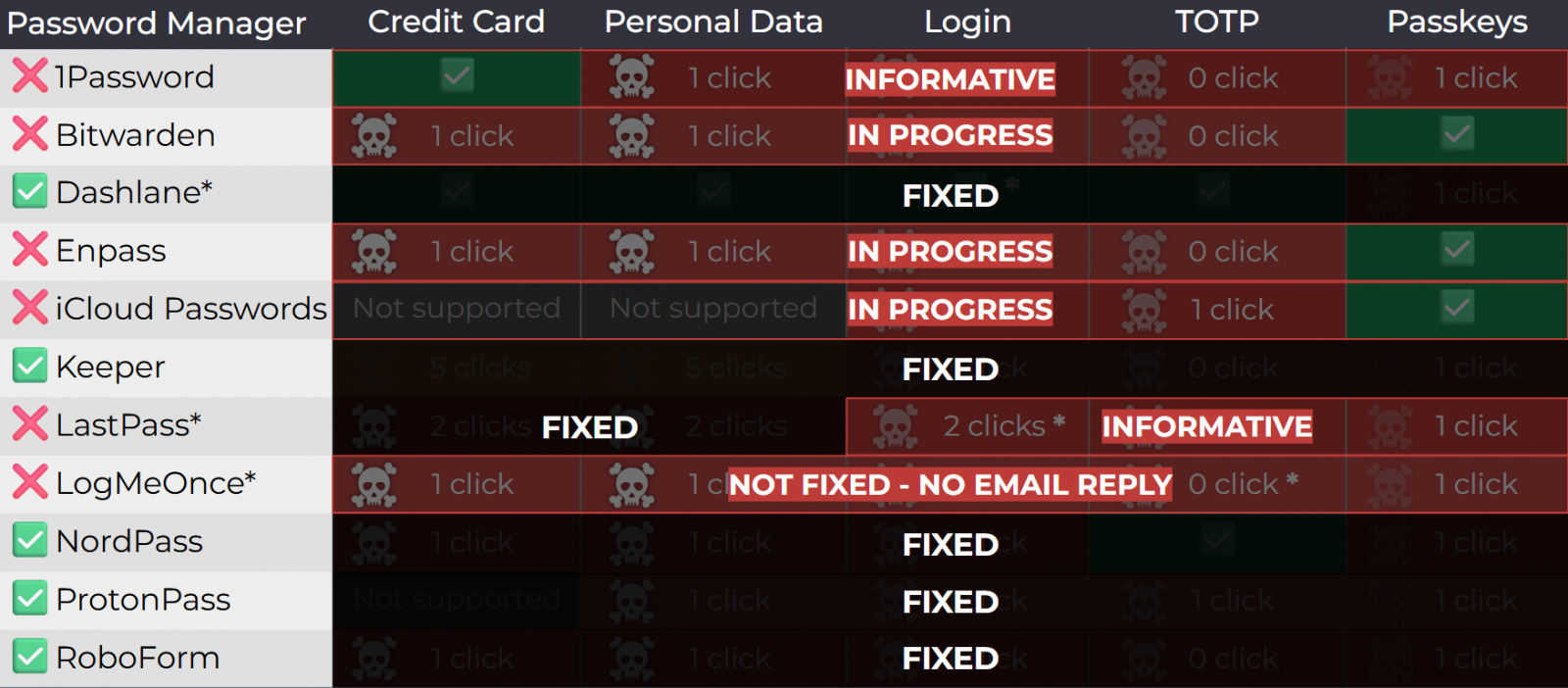
The researcher tested 11 password managers selected for their popularity and found that they were all unsafe for at least one attack method.
Source: Mark Tath
With the help of socket, all vendors were informed about issues in April 2025. The researcher also warned him that public disclosure would follow in August 33.
1password rejected the report, classifying it as “out-off-scope/informative”, arguing that clickjacking should reduce a general web risk users.
Similarly, the lastpass marked the report as “informative”, while Bitwardon accepted the issues but reduced the severity. However, Bitwardon told Bleepingcomputer that this week’s versions are fixed in the 2025.8.0 edition, rolling out this week.
It is not clear whether the lastpass and 1password are planned to solve the problem.
Logmeonce did not respond to any communication efforts, either by Tóth or socket.
Currently, the following password manager, who is simultaneously around 40 million users, is unsafe for the methods of attack of taths.
- 1password 8.11.4.27
- Bitwardon 2025.7.0
- Enpass 6.11.6 (Partial fixed applied in 6.11.4.2)
- iCloud Password 3.1.25
- Lastpass 4.146.3
- Logmeonce 7.12.4
The sellers applying the fix are Dashlen (V6.2531.1 issued on 1 August), Nordpass, Protonpass, Roboform and Kipper (V17.2.0 July). However, users should ensure that they are running the latest available versions of products.
Source: Mark Tath
Till the time the fix is available, Tóth recommends that the users disable autofil function in their password managers and use only copy/paste.
Bleepingcomputer has approached all vendors who have not yet improved their products, and we will update this post with their reactions, once they reach us.



