
A new side-channel attack called pixelsnapping enables a malicious Android app to extract sensitive data by stealing pixels displayed by applications or websites and reconstructing them to derive content.
The content may include sensitive personal data such as chat messages from secure communication apps like Signal, emails to Gmail, or two-factor authentication codes from Google Authenticator.
The attack, designed and demonstrated by a team of seven US university researchers, works on fully patched modern Android devices and can steal 2FA codes in less than 30 seconds.
Google attempted to fix the problem (CVE-2025-48561) in the September Android update. However, researchers were able to bypass the mitigation and an effective fix is expected in the December 2025 Android security update.
How does picsnapping work?
The attack begins with a malicious app that abuses Android’s intent system to launch the target app or webpage, so its window is submitted to the system’s structure process (SurfaceFlinger), which is responsible for combining multiple windows when they appear at the same time.
In the next step, the malicious app maps target pixels (for example, the pixels making up the digits of a 2FA code) and determines through several graphical operations whether they are white or non-white.
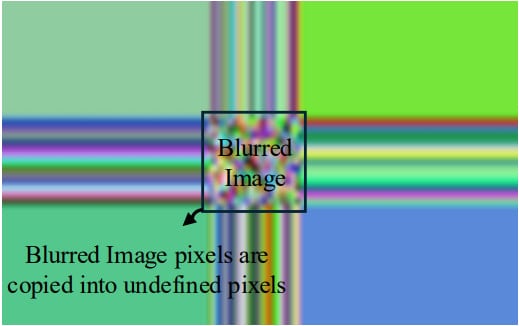
It’s possible to isolate each pixel by unleashing what the researchers call a ‘masking activity’, which sits in the foreground, hiding the target app. The attacker then makes the cover window “all opaque white pixels except the pixel at a location chosen by the attacker which is set to be transparent.”
During a pixelsnapping attack, individual pixels are enlarged, allowing SurfaceFlinger to take advantage of a “quirk” in the way blur is applied that creates a stretch-like effect.
Source: pixnapping.com
After all victim pixels are recovered, an OCR-style technique is used to isolate each character or digit.
“Conceptually, it’s as if the malicious app was taking screenshots of screen content it shouldn’t have access to,” the researchers said. explain,
To steal data, the researchers used a GPU.zip side-channel attack, which exploits graphical data compression in modern GPUs to leak visual information.
Although the data leakage rate is relatively low, ranging from 0.6 to 2.1 pixels per second, the optimization demonstrated by the researchers shows that 2FA codes or other sensitive data can be exfiltrated in less than 30 seconds.
impact on android
The researchers performed pixelsnapping on Google Pixel 6, 7, 8, and 9 devices, as well as a Samsung Galaxy S25 running Android versions 13 to 16, and all of them were vulnerable to the new side-channel attack.
Since the underlying mechanisms that enable pixelsnapping are found on older Android versions, presumably, most Android devices and older OS versions are also vulnerable.
Researchers analyzed nearly 100,000 Play Store apps, detecting hundreds of thousands of invocable actions via Android Intent, indicating that the attack is widely implemented.
The technical paper presents the following examples of data theft:
- Google Maps: Timeline entries occupy ~54,264-60,060 pixels; Unoptimized recovery of an entry takes ~20-27 hours on all devices.
- Venmo: Activities (profiles, balances, transactions, details) are openable through implicit intents; Account-balance areas are ~7,473-11,352 pixels and leakage is unoptimized at ~3-5 hours.
- Google Messages (SMS): Explicit/implied intentions can start a conversation. The target areas are ~35,500–44,574 pixels; Non-adapted recovery takes ~11-20 hours. The attack differentiates sent versus received by examining blue versus non-blue or gray versus non-gray pixels.
- Signal (Private Message): Underlying intentions can start a conversation. The target areas are ~95,760–100,320 pixels; Unoptimized recovery takes ~25-42 hours, and the attack works even if Signal’s screen protection is enabled.
Both Google and Samsung have committed to fixing the flaws before the end of the year, but neither GPU chip vendor has announced patching plans for the GPU.zip side-channel attack.
While the original exploit method was mitigated in September, Google received an updated attack that demonstrated a bypass of the original fix. Google has developed a more in-depth patch to be released with the Android security updates for December.
Google says that taking advantage of this data leak technique requires specific data about the targeted device, which, as the researchers noted, reduces the success rate. The current verification found no malicious apps taking advantage of the Pixnapping vulnerability on Google Play.



