
A novel tapjacking technique can take advantage of the user interface animation to bypass the permission system of Android and allow sensitive data or trick users to perform disastrous actions, such as wipes of the device.
Unlike traditional, overlay-based tapsacing, the taprap attack also works with zero-parametic applications to launch a harmless transparent activity on top of a malicious one, also with a behavior that remains unmate in Android 15 and 16.
Taptrap was developed by a team of security researchers at Tu Wien and Bayreth University (Philip Beer, Marco Squarsina, Sebstian Roth, Martina Lindorfer), and will be presented in the next month Usenix Safety Seminar,
However, the team has already published Technical letter It outlines the attack and A Website It summarizes most of the details.
How does tiprap work
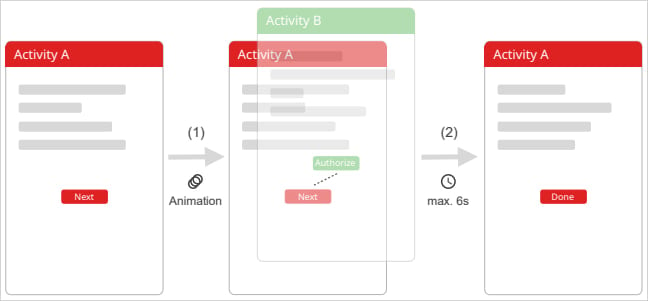
TAPTRAP abuses the way android activity handles infections with custom animation that sees the user and the device actually registers.
A malicious app installed on the target device launches a sensitive system screen (permission Prompt, System Settings, etc.) from another app using ‘Startectivity ()’ with a custom low-opesity animation.
“The key to the taprap is using an animation that provides the target activity almost invisible,” the researchers said that The website that explains the attack,
“It can be achieved by defining a custom animation, with both beginners and expired op variety (alpha) a low value, such as 0.01,” thus made malicious or risky activity almost completely transparent.
“Alternatively, a scale animation can be applied to zoom in a specific UI element (eg, an permission button), allowing it to occupy full screen and increase the opportunity to tap the user.”
Source: Taptrap.Click
Although the prompt a launched prompts receive all the touch events, all the users see that the underlying app shows its own UI elements, as it has a transparent screen on top of which the user is actually attached.
Thinking that they interact with the Benning app, a user can tap on specific screen positions that suit risky tasks, such as “permission” or “authorized” button on almost invisible signals.
A video released by the researchers shows how a game app can avail tattrap to enable camera access to a website through Chrome browser.
Risk risk
To check if the Tipp Play Store could work with the application in the official Android repository, researchers analyzed around 100,000. They found that 76% of them are insecure for tattrap as they include a screen (“activity”) that meets the following conditions:
- Can be launched by another app
- Calling runs in the same task as app
- Infection does not override to animation
- User does not wait for animation to end before reacting to input
Researchers say that animations on the latest Android version are enabled until the user deactivates them with developer options or accessibility settings, exposing the device to tatrapy attacks.
When developing the attack, the researchers used Android 15, the latest version at that time, but after the arrival of Android 16, they also conducted some tests on it.
Marco Squarsina told BlappingCopper that she had tried to tippe on Android 16 on Google Pixel 8A and can confirm that the issue is precious.
Mobile operating system graphinos, which focuses on privacy and security, also confirmed the Blapping computer that the latest Android 16 is unsafe for tattrap technology, and announced that their next release would be Include a fix,
Bleepingcomputer has approached Google about Taptrap, and a spokesman said that the taprap problem will be reduced in future updates:
“Android is continuously improving its existing mitigation against tapjacking attacks. We know about this research and we will address the issue in future updates. Google Play has policies to keep users safe, which should follow all developers, and if we find that we have a violation of our policies.”



