
ORACLE has added an ongoing forcibly recovery campaign claimed by the clop ransomware gang packed with e-business suits (EBS) weaknesses in July 2025.
While the company has so far credited the attack for this ransomware operation, Oracle’s Chief Security Officer, Rob Duhart confirmed that customers had received forcible recovery emails from the gang.
Duhart urged Oracle customers to update their software and advised people requiring further assistance to contact the Oracle Support Team.
“Oracle knows that some Oracle e-business suits (EBS) customers have received forcible recovery emails, Duhart said Thursday details“Our ongoing investigation has found a possible use of pre -identified weaknesses addressed in July 2025 Critical Patch updates. Oracle has confirmed his strong recommendation that customers apply the latest important patch updates.”
Although it did not indicate a specific vulnerability that could be exploited, Oracle addressed Nine security flaws The July 2025 Critical Patch updates affect their e-business suit as part of them, three of them (CVE-2025-30745, CVE-2025-30746, and CVE-2025-50107) user credentials without a distant trendy.
Mandiant and Google Threat Intelligence Group (GTIG) told Bleepingcomputer this week that officials of many companies have received emails required to prevent ransom to prevent the allegedly stolen sensitive data from their OraCle e-Business Suite Systems from being leaked online.
According to GENEVIEVE Stark, head of GTIG’s cybercrime unit, the attackers started sending emails of these forced recovery on or before “on or before 29 September, 2025, and danger analysts are still investigating this malicious activity.
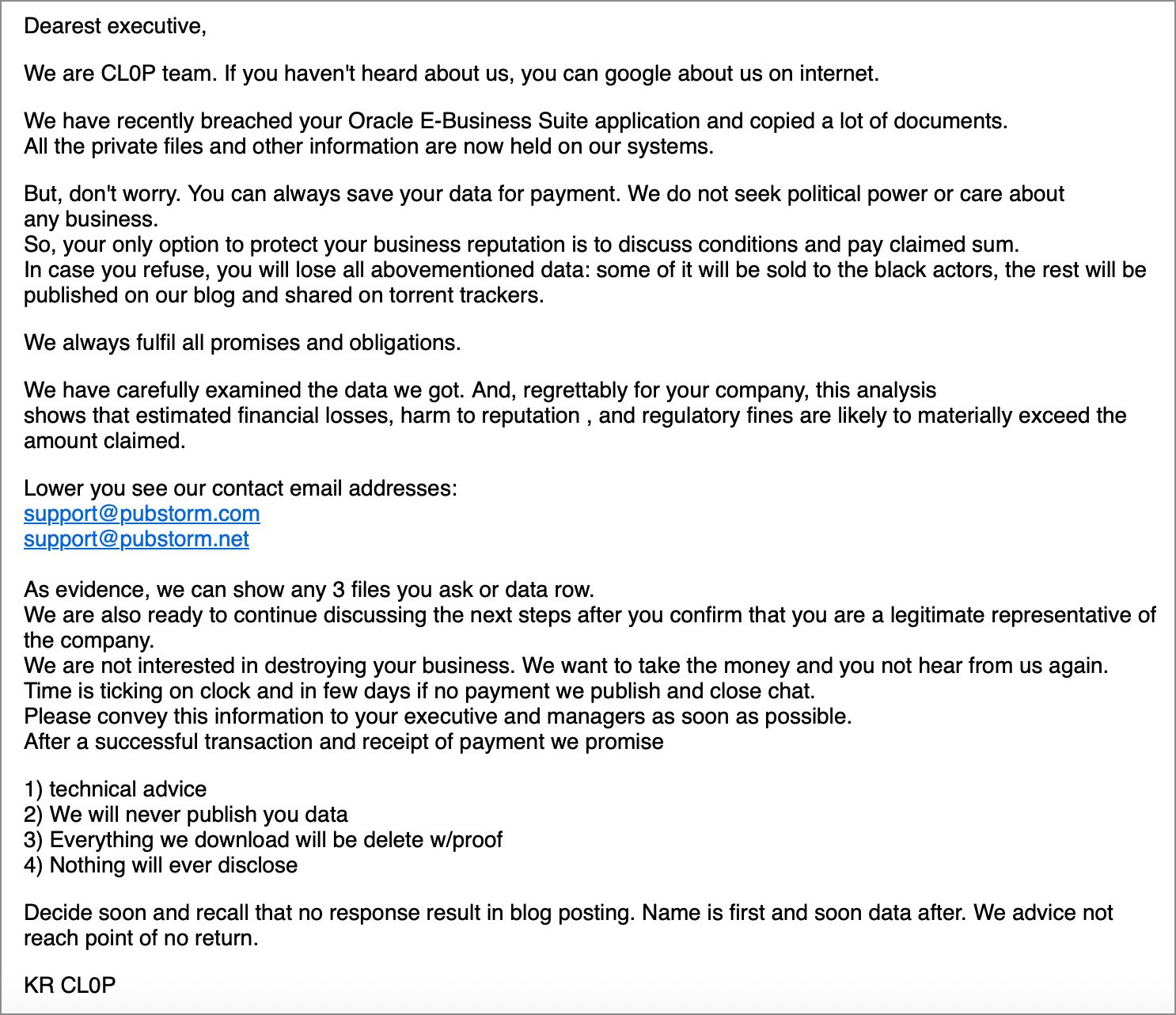
“We are CL0P teams. If you have not heard about us, you can go to Google on the Internet. Email.
While Mandient Chief Technology Officer Charles Karmakal said that there is insufficient evidence to determine whether the data is actually stolen, the clop gang claimed in a statement shared with the Blapping computer claimed that they are involved in the extortion campaign, which adds attacks with a bug in an Oracle product.
Clope said, “Soon all will be clear that Oracle provoked his main product and once again, work to save the day is on clop.
Clop claims follow the extortion of dozens of victims in January, which was violated in a huge wave of data theft attacks targeting zero-day vulnerability (CVE-2024-50623) in Cleo’s safe file transfer software.
Earlier, the cybercrime group was linked to several other data theft campaigns, which later, along with impact, targets zero-day flaws in ACC-Day, Goeni MFT, and Movit Transfer. Over 2,770 organizations worldwide,
The US State Department now offers a reward of $ 10 million for any information that connects the clop ransomware attacks to a foreign government.



