
State-proposed hackers involved in the Silk Typhoon Activity Cluster, abducting web traffic and targeted diplomats by kidnapping on a malware-serving website.
Hackers used an advanced anti-in-in-media (AITM) technique to hijack the network’s captive portal and sent the target to first-step malware.
The Google Threat Intelligence Group (GTIG) tracks the danger actor as UnC6384 and based on tooling, targeting and infrastructure, assumes that this Chinese threat is associated with actor Tempax.
Kidnapping chrome request
GTIG researchers believe that Aitm was possible after compromising an age device on the target network; However, he did not find evidence to support this principle.
The attack begins when the Chrome browser checks if it is behind a captive portal, a web page where a network users certify before connecting to the Internet.
With hackers in the event of kidnapped web traffic, they redirect the target to a landing page, which applies an adobe plugin update site.
The victims download a digitally signed ‘Adobeplugins.exe’ file, which is presented as an essential plugin update, and directed for step-by-step instructions on the site to bypass Windows safety signs when installing it.
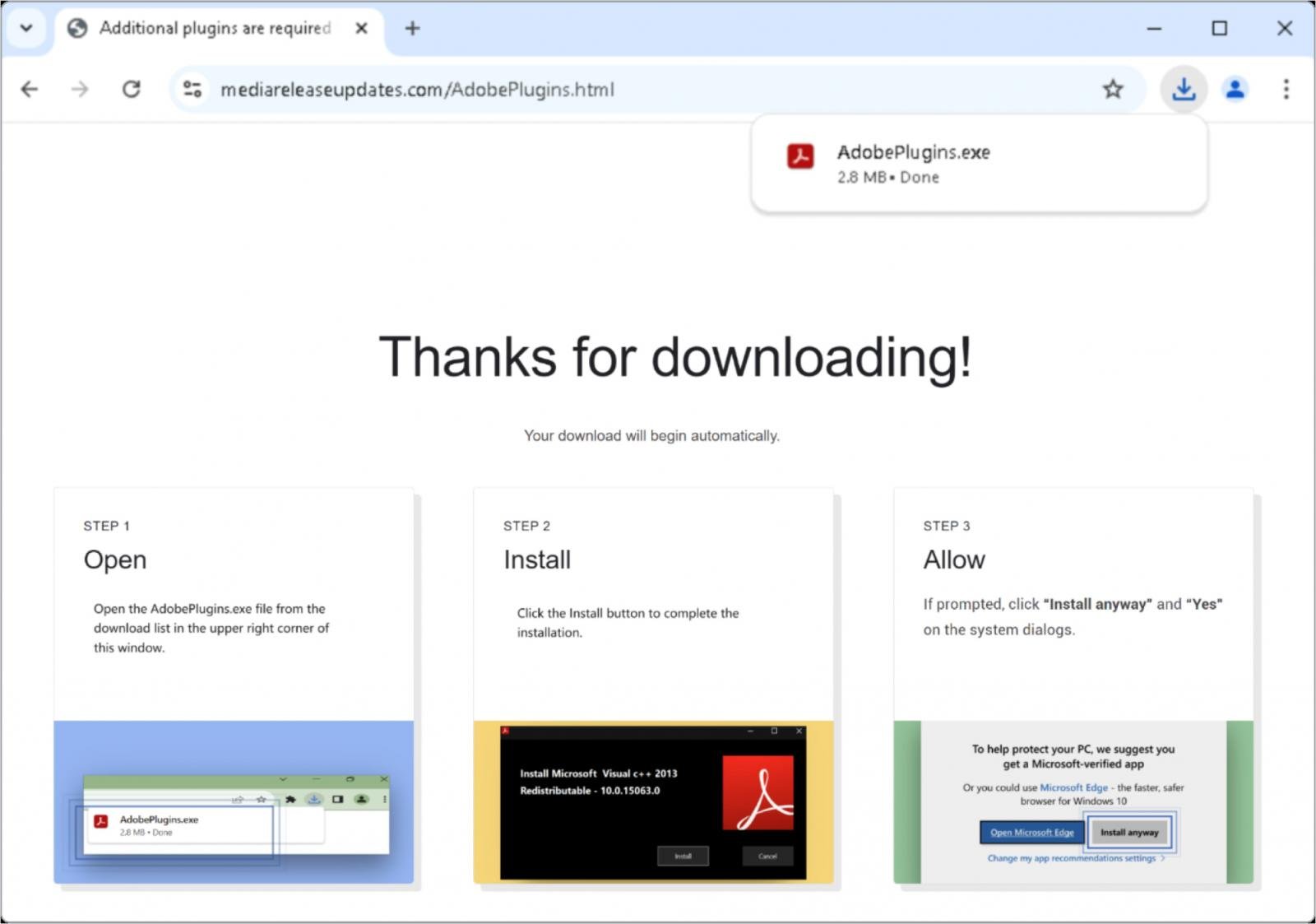
Source: Google
Launching that file displays a Microsoft Visual C ++ Installer, but it secretly downloads a disguised MSI package (20250509.bmp) in which a valid canon printer tool, a DLL (cannstager), and RC-4 encrypted forms contains sagu.SEC backdur.
The canonstager DLL decips and loads the last payload in the system memory using the side-loading technique.
Sogu.Sec, which Google says that plugx is a type of malware, which is used extensively by many Chinese danger groups, can collect system information, upload or download files, and provide operative with remote command shells.
.jpg)
Source: Google
GTIG researchers noted It is not clear that the Signing Unit used in this campaign, Chengdu Nauzin Times Technology Company, Limited, was deliberately participating or compromised in these works.
However, GTIG tracks at least 25 malware samples signed by this unit from the beginning of 2023, which is associated with various Chinese activity groups.
Treating all certificates from Chengdu Nauzin Times Technology Company, Limited has a proper defensive action as incredible until the situation becomes clear.
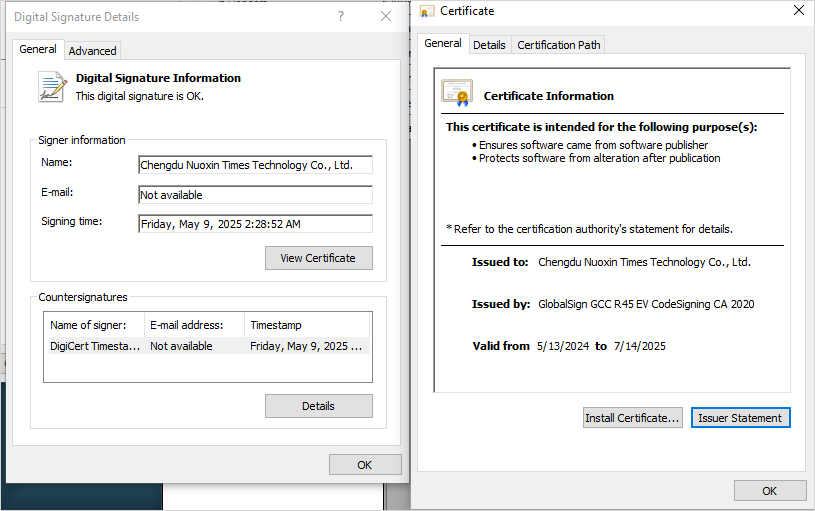
Source: Google
Google blocked the malicious domain and affected the file hash through safe browsing and issued a government -backed attacker alerts affecting Gmail and workspace users.
The tech giant has also shared the Yara rules to detect staticPlugin and cannostagers, and indicators of compromise (IOCs) for all files sampled by these attacks.
This latest campaign is a sign of the growing refinement of Chinese-Naxus detective actors, which are very likely to switch to new infrastructure and binary build and rebound quickly.



