
Microsoft has warned that a danger actor tracked as Storm -0501 has developed his operation, which is away from encrypting devices with ransomware to focus on cloud -based encryption, data theft and extortion.
Hackers now abuse the abuse of indigenous cloud features to exfiltrate data, wipe backup and destroy storage accounts, allowing traditional rangesware encryption tools to put pressure and to expel the victims without deploying the encryption tool.
Storm -0501 is a danger an actor who is active since at least 2021, deploys Sabbath Rainmware in attacks against organizations worldwide. Over time, the danger actor joined various ranges-a-A-Services (RAAS) platforms, where he used encrypters from Hive, Blackcat (Alfav), Hunters International, Lockbit and, recently, Ambargo ranges.
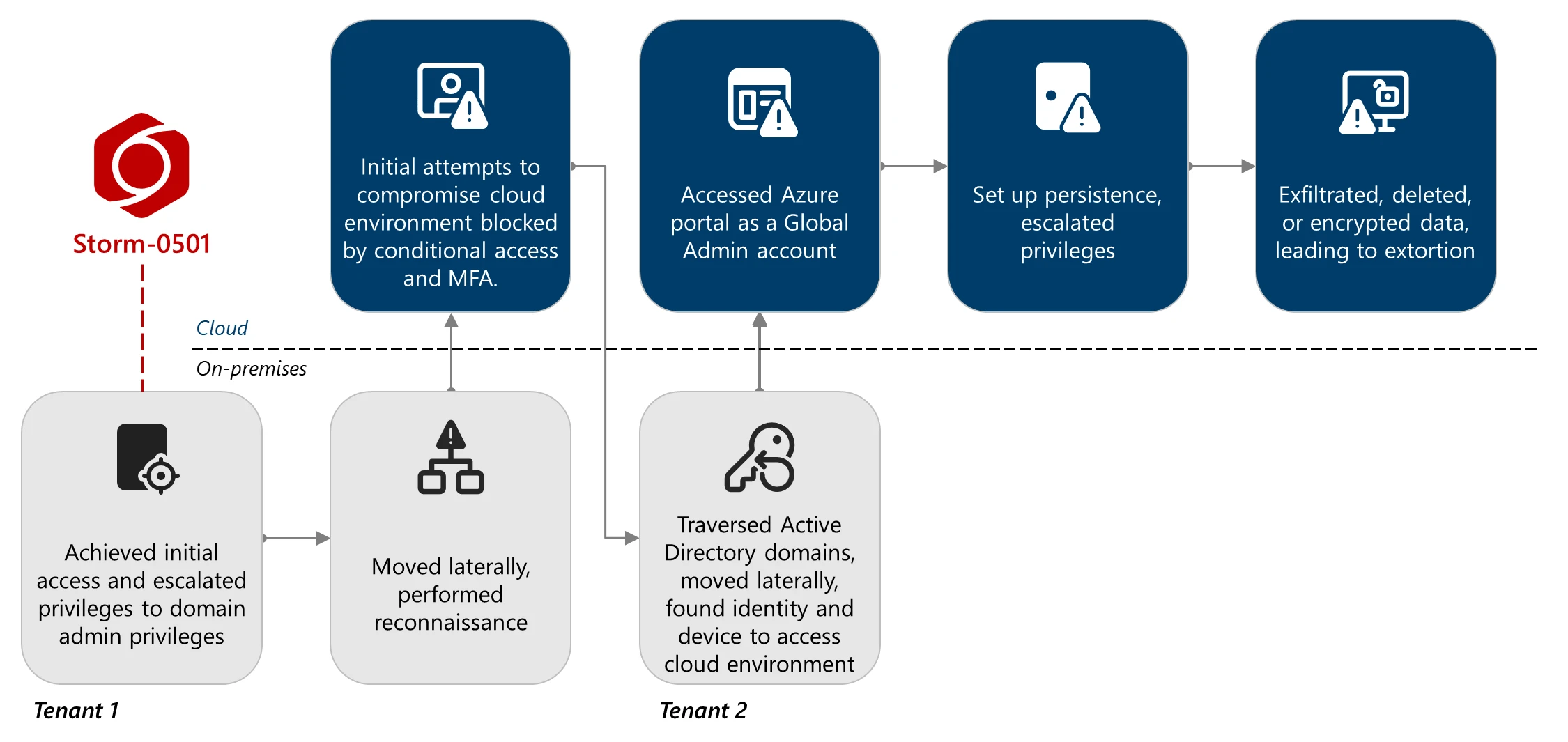
In September 2024, Microsoft explained in detail how Hurricane -0501 extended its operation into the hybrid cloud environment, from compromising active directory to entra ID tenants. During these attacks, the danger actors either created a continuous backdoor through malicious federal domains or encrypted the on-primesies device using ransomware such as ransomware.
A new report of Microsoft underlines changes in the strategy today, in which Storm -0501 is no longer dependent on on -radius encryption and instead conducts purely attacks in the cloud.
“Unlike traditional on-primeses ransomware, where the actor usually deploys malware to encryptuate important files in endpoints within the network within the network and then interactions for a decrying key, cloud-based ransomware introduces a fundamental change,” reported in the report. , Microsoft Danger Wisdom,
“Storm -0501 eliminates large versions of rapid data, destroying data and backups within the environment, taking advantage of cloud -country abilities, and demands ransom without relying on traditional malware perfection.”
Cloud-based ransomware attacks
In recent attacks viewed by Microsoft, hackers tied up with several active directors domains and entra tenants by taking advantage of the interval in Microsoft Defenders Perinogen.
Storm -0501 then used the stolen directory Synchronization Accounts (DSAS), with devices such as AzureHound to calculate users, roles and azure resources. The attackers eventually discovered a global administrator account, which led to a lack of multifarmer authentication, allowing him to reset his password and get complete administrative control.
With these privileges, he established firmness by adding malicious federated domains under his control, making them able to bypass MFA security in almost any user and domain.
Microsoft says that he carried forward his reach in Azure by misusing Microsoft.Authorization/Elevateaccess/Action, which finally allowed him to hand over themselves to the role of the owner, effectively to handle the entire azure environment of the suffering.
Source: Microsoft
Once under the control of the cloud environment, Hurricane -0501 began to disable the defense from the azure storage accounts and steal sensitive data. The danger actors attempted to destroy storage snapshots, restoration points, recovery services vaults and storage accounts to prevent the target from recovering data for free.
When the actor could not remove the data from the actor recover services, he used cloud-based encryption by creating new key vaults and customer-related keys, effectively encrypted the data with the new key and made it inaccessible to the company until they pay ransom.
After the theft of data stealing, destroying backups, or encrying cloud data, the storm -0501 contacted the victims through Microsoft teams using the compromised accounts to meet the ransom demands.
Microsoft’s report shared safety advice, Microsoft defender XDR detection, and hunting questions that can help find and find out the strategy used by this danger actor.
Since the ransomware encrypters are rapidly blocked before encrypting the device, we can transfer other danger actors to cloud-based data theft and encryption from on-primesies encryption, which can be difficult to detect and block.



