
Threatening actors are using several websites promoted through Google advertisements, to distribute a PDF editing app, distributing an information-chori malware called Tamperedchef.
This campaign is part of a large operation with several apps that can download each other, some of them are cheating users to nominate their system in residential proxy.
More than 50 domains have been identified to host fraudulent apps signed with a fraud certificate issued by at least four different companies.
Researchers say the campaign seems wide and well orchestrated as operators waited for ADS to run their course, which was to run their course before activating malicious components in applications.
Complete updated infostealer distributes
A technical analysis of the cyber security services company TrueSEC describes the process of tamperedchef infostealer being tampered with in the user’s system.
Researchers found that malware was distributed through several websites, which promoted a free device called Appsuite PDF Editor.
Based on the Internet record, investigators determined that the campaign began on 26 June, when many of the websites involved were either registered or advertising the Appsuite PDF editor.
However, researchers found that the malicious app was verified through the app Wirstotal Malware scanning services on 15 May.
It seems that the program was treated normally till August 21, when he received an update that activates malicious abilities manufactured to collect sensitive data such as credentials and web cookies.
According to Trueesec, the tamperedchef infostealer is given with “-Bullupdate” logic for the executable of the PDF editor.
Checks malware for various security agents on the host. It also questions the database of web browsers installed using DPAPI (Data Safety Apps Programming Interface) – an ingredient in Windows that encrys sensitive data.
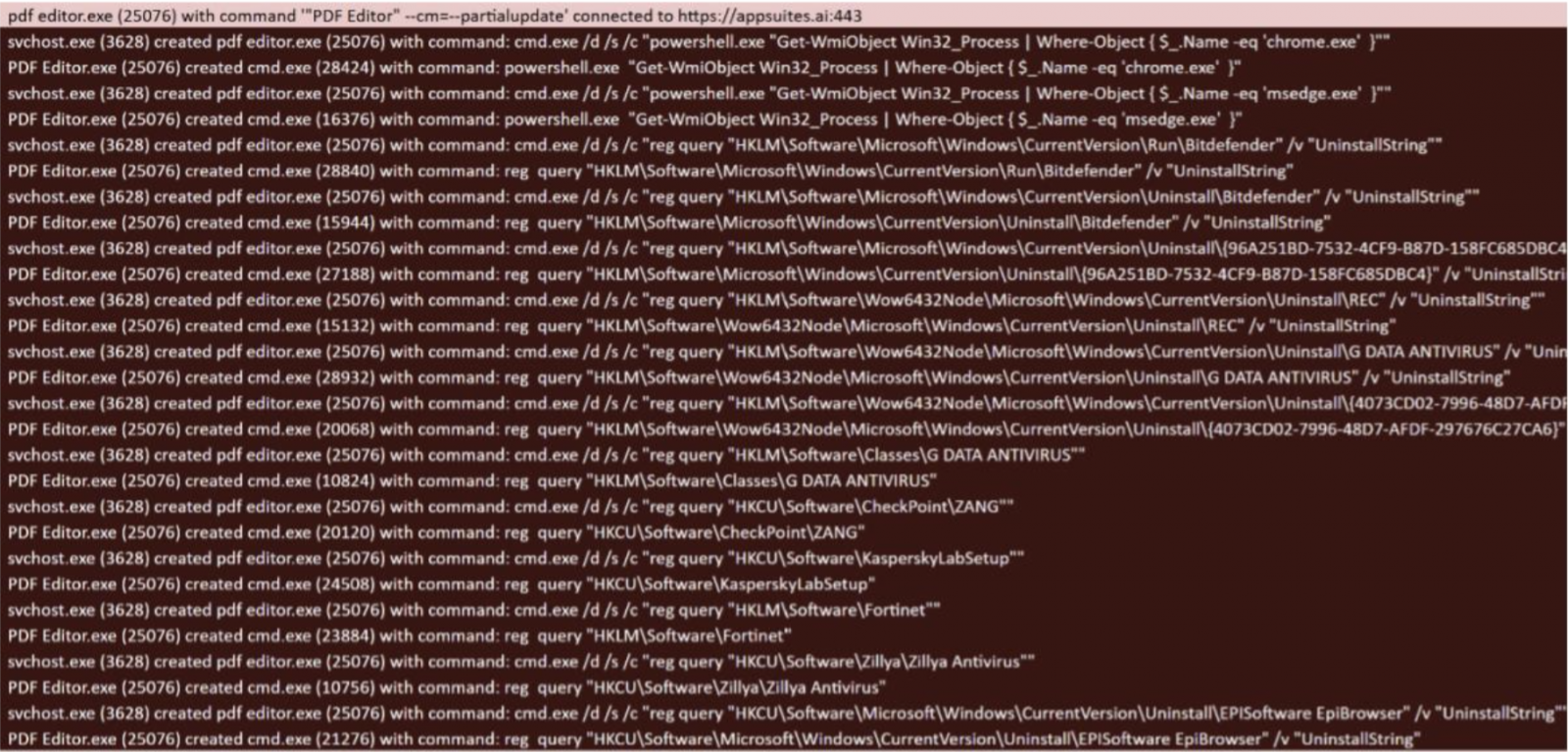
Source: Truesec
Digging deeply for the distribution method, the TrueSEC researchers found evidence that the actor with danger trusted the Google advertisement to promote the malicious program that spreads the tamperedchef within the Appsuites PDF editor.
“Truesec has seen at least 5 different Google Campaign IDs that suggest a comprehensive campaign” – Truesec
The danger actor had a strategy to maximize the number of downloads before activating the malicious ingredient in the Appsuites PDF editor, as he had informed the infostealer four days before the 60 -day typical termination period for the Google Advertising Campaign.
Further in Appsuites PDF Editor, researchers found that various versions of the program were signed by “at least four companies” certificates, among them Echo Infini SDN BHD, G Gult by J SDN. BHD, and Summit Nexus Holdings LLC, BHD.
Join a residential proxy
Trueesec found that the operator of this campaign has been active since August 2024 and has promoted other devices, including Onstart and Epibrowser browser.
It is worth noting that Onstart usually shows a green signal Potential unwanted program (Pup), which is usually the word for adhaware.
However, the researchers of the managed detection and response company also also examined the events involving the events that involve the events involving appsuits PDF editor, manualfinder, and onestart, all “excessive suspected files, executing unexpected commands and turning the hosts in residential proxy.
He found that Onstart Appsuite-PDF (an eco Infini sdn. Signed by BHD Certificate), which can get the PDF editor.
“Onstart, Appsuite-PDF, and initial downloads for PDF editors are being distributed by a large advertising campaign advertisement PDFS and PDF editors. Expelled,
The codes used in this campaign have already been canceled, but the risks still exist for the current establishments.
In some examples of the PDF editor, the app will show a message to the users, who in turn seek permission to use their device as a residential proxy to use the tool for free.
Researchers noted that the proxy network provider may be a valid unit that is not included in the campaign and is capitalization as an operator of the PDF editor.
It seems that anyone who is behind the PDF editor is trying to maximize its profit at the cost of users worldwide.
Even if programs in this campaign are considered puppies, their abilities are distinctive to malware and they should be considered in this way.
Researchers warned that the operation they exposed more apps include some of them have not yet weapons, are able to distribute malware or suspected files, or execute the command on the system.
Both reports from Trueesec and expelled (1, 2) A large set of indicators of the agreement (IOCS) involves that can help defenders from being infected by users and assets from being infected.



