Researchers have revealed the details of a new hardware attack displayed against the AMD and Intel System, but the chip giants do not look worried because the method requires physical access to the target device.
Method of attack, name battering ramKU Luvenes in Belgium and Birmingham University in Britain and a team of academic researchers representing Durham University were discovered.
Researchers revealed the details of Badram later last year, an attack that used $ 10 tools to break the reliable execution environmental protection of AMD, enabled the attackers to gain access to potentially sensitive information stored in memory.
He has now presented the beating RAM, which can bypass modern rescue by Intel and AMD Cloud Processor.
According to the researchers, the attack can break up the Intel SGX and AMD SEV-SNP confidential computing technologies that are widely used by cloud providers and are also designed to protect sensitive data from malicious internal sources and attackers that have access to host systems.
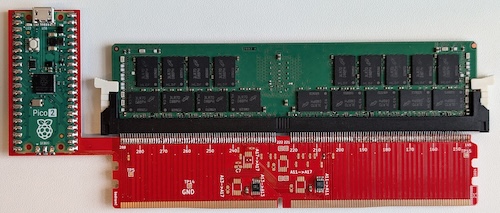
Batting RAM involves installing an instrument called an interpreting between CPU and DRAM memory. The interpozer, which the researcher managed to manufacture for only $ 50, is connected to the DIMM and can sit quietly to avoid detection. However, with a flip of a switch, the device can be enabled to quietly redirect the preserved memory address at the locations controlled by the attacker.
Researchers explained, “Our secretly bypasses the interpreting memory encryption and state-of-the-art boot-time defense, bypassing both invisible for the operating system.” “It enables arbitrary plaintext access to SGX-protected memory, and breaks the attitude feature of the SEV on a fully patched system. Finally, beating the RAM exposes the boundaries of today’s scalable memory encryption.”
A batting RAM attack requires physical access to the targeted system to conduct a RAM attack, but researchers argue that the attacker only requires access to the device for a short time. He believes that such attacks in the real -world environment can be conducted through evil cloud employees, data center technicians, law enforcement, and manufacturing or shipping a memory module during manufacturing or shipping.
Researchers mentioned that the interpreting designs they only work against DDR4 memory, but believes that a more advanced interpreting may be able to conduct attacks on DDR5 and at the same time the underlying issues may not be corrected.
Intel And AMD In February 2025, the findings were reported. While the two vendors published security advice on Tuesday, the day the research was published, they reported that the two reported that the attacks required by the physical access to the target system are not under the risk of the danger model of their products.
Intel reported that some of its Xeon processors include a feature called total memory encryption-malty-key (TME-MK), which can provide additional protection against such attacks. The seller urged customers to ensure physical security of equipment through the equipment provided by the company.
Researchers confirmed that software or firmware updates could not patch vulnerability.
In addition to one paper Describing the findings, experts made everyone public Technical information There is a need to create a batting ram interpocer.
Connected: Intel TDX Connect Bridge to CPU-GPU Safety Interval
Connected: Chipmaker Patch Tuesday: Many weaknesses addressed by Intel, AMD, Nvidia
Connected: Intel employee exposed by data weaknesses


